$1.77 Billion Was Lost to Business Email Compromise Attacks in 2019
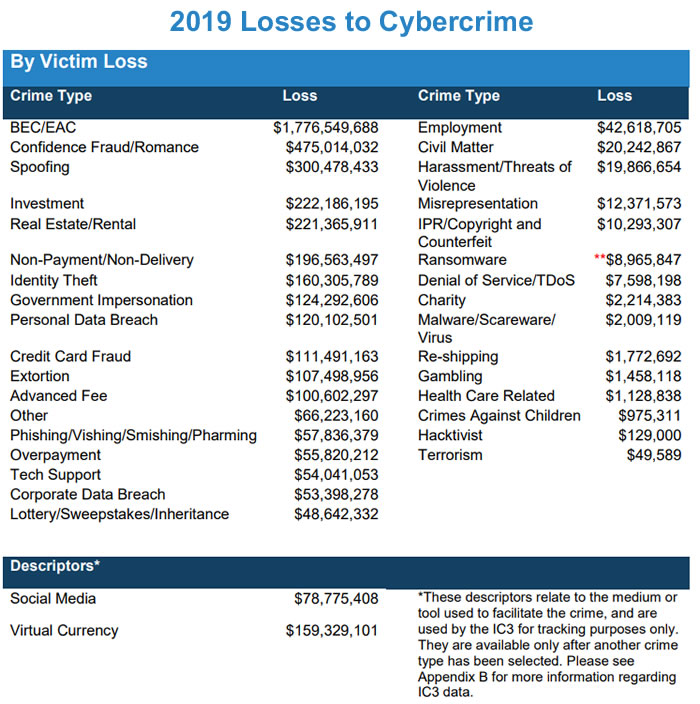
The Federal Bureau of Investigation’s (FBI) Internet Crime Complaint Center (IC3) has published its 2019 Internet Crime Report. The report shows losses to cybercrime exceeded $3.5 million in 2019. More than half of the losses were due to business email compromise (BEC) attacks.
BEC, also known as email account compromise (EAC), involves the impersonation of a legitimate person or company to obtain money via email. These sophisticated scams often start with a phishing attack on an executive to obtain email credentials. The email account is then used to send a wire transfer request to an individual in the company with access to corporate bank accounts. Sometimes this step is skipped and the attackers simply spoof an individual’s email account.
While BEC attacks mostly involve wire transfer requests, in 2019 there was an increase in attacks on human resources and payroll departments to divert employee payroll funds to attacker-controlled pre-paid card accounts. The potential profit from such an attack is lower than a wire transfer request, but changes to payroll are less likely to be queried and the attacks have a greater chance of success.
BEC/EAC attacks are popular with cybercriminals as they require little skill, are easy to execute, and the potential rewards from a successful attack are considerable. Wire transfer payments of tens or hundreds of thousands of dollars are common. Out of the 467,361 complaints, only 6.47% (23,775) were BEC/EAC attacks, yet the losses to those attacks were $1.77 billion, making these attacks the most financially damaging type of cyberattack. The average loss to a BEC/EAC attack in 2019 was $75,000.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
“Criminals are getting so sophisticated,” said IC3 chief, Donna Gregory. “It is getting harder and harder for victims to spot the red flags and tell real from fake.”
BEC attacks may result in the highest losses, but phishing attacks are more numerous. In 2019, 114,702 phishing attacks were reported to IC3. Phishing attacks – which include vishing (voice), smishing (SMS), and pharming (website redirects) – resulted in losses of $57,836,379. The average loss to a phishing attack was $504. Email is still the most common form of phishing, but SMS- and voice-based phishing attacks have increased.
Ransomware attacks certainly made the headlines in 2019 with scores of reported attacks on businesses, government agencies, healthcare organizations, cities, and municipalities. Several of those attacks saw ransomware demands issued in excess of $500,000. Even so, the losses to those attacks were relatively small, accounting for just $8,965,847 in ransom payments across 2,047 reported attacks. The average ransom payment in 2019 was $4,400. In 2018, IC3 figures show a decline in ransomware attacks and an increase in losses. In 2019, ransomware attacks increased by more than 37% and losses increased by more than 147.5%.
It should be noted that the actual losses due ransomware attacks are considerably higher as the IC3 figures do not include downtime, lost business, and remediation costs. Also, many victims of ransomware attacks quietly pay the ransom and do not report the attacks to IC3.
In the report, IC3 emphasized the importance of reporting cyberattacks and how prompt reporting can help law enforcement stop fraudulent transactions and trace the perpetrators of an attack.
“Information reported to the IC3 plays a vital role in the FBI’s ability to understand our cyber adversaries and their motives, which, in turn, helps us to impose risks and consequences on those who break our laws and threaten our national security,” said Matt Gorham, assistant director of the FBI’s Cyber Division.