State Of HIPAA – 2025 Predictions
 It has been almost three decades since President Clinton signed the Health Insurance Portability and Accountability Act (HIPAA) into law in 1996 and 23 years since the first of the Administrative Simplification Rules took effect, yet HIPAA compliance is still proving a challenge for many HIPAA-regulated entities. Noncompliance with the HIPAA Rules is frequently identified by OCR and State Attorneys General in compliance audits and data breach and complaint investigations.
It has been almost three decades since President Clinton signed the Health Insurance Portability and Accountability Act (HIPAA) into law in 1996 and 23 years since the first of the Administrative Simplification Rules took effect, yet HIPAA compliance is still proving a challenge for many HIPAA-regulated entities. Noncompliance with the HIPAA Rules is frequently identified by OCR and State Attorneys General in compliance audits and data breach and complaint investigations.
This article explores the current state of HIPAA and compliance and some of the main aspects of the HIPAA Rules that are proving difficult for HIPAA-regulated entities, and includes predictions for 2025.
How Did We Do With Our 2024 HIPAA Predictions?
- OCR will increase enforcement actions for violations of the HIPAA Security Rule that have contributed to data breaches and HIPAA Breach Notification Rule violations for failing to issue timely notifications to individuals whose PHI has been compromised in data breaches. 2024 will see record numbers of settlements and civil monetary penalties.
- I was not far off, as the OCR Director confirmed that 22 HIPAA enforcement actions were closed in 2024 with financial penalties, which almost made it a record year for penalties; however, I was a little too hopeful that there would be a clampdown on late breach notifications. Individual notifications continue to be issued by some regulated entities, many months after a data breach has occurred.
- The HIPAA Right of Access will continue to be an enforcement priority for OCR – This is low-hanging fruit. The investigations are straightforward and require few OCR resources, and the findings of investigations are unlikely to face legal challenges.
- OCR has continued to target noncompliance with this HIPAA Privacy provision and has now imposed 51 penalties for failing to provide timely access to medical records and charging excessive amounts for providing those records.
- OCR is planning a HIPAA Security Rule update in Spring 2023, which we predict will include several new mandatory requirements for cybersecurity, including stricter access control requirements such as mandatory multi-factor authentication.
- It took longer than planned; however, OCR published its proposed HIPAA Security Rule in December 2024, and multifactor authentication, encryption, network segmentation, penetration tests, annual internal Security Rule audits, 6-monthly vulnerability scans, anti-malware software, checks of Security Rule compliance, and other cybersecurity measures will – if enacted – become mandatory.
- A final rule will be introduced regarding disclosures of reproductive health information, which will be prohibited for reasons other than treatment, payment, and healthcare operations and for PHI to be used for identifying, investigating, and prosecuting patients, providers, and others involved in the provision of legal reproductive health care services, in response to the overturning of Roe v. Wade
- This was one of OCR’s key priorities, and the final rule was added to the Federal Register on April 26, 2024, and took effect on December 23, 2024.
- The lawsuit filed by the AHA in response to OCR’s December 2022 guidance on tracking technologies makes strong arguments that OCR has stretched the definition of protected health information to more than the current statute can bear. Should that challenge not prove to be successful, 2024 will see the first enforcement action over the use of tracking technologies on hospital websites. If the lawsuit is successful, further rulemaking will be proposed regarding tracking technologies to ensure patient privacy.
- The challenge was successful, and the guidance was partially vacated. While there were no OCR enforcement actions regarding tracking technologies, the New York Attorney General imposed a $300,000 financial penalty on New York Presbyterian Hospital for using pixels and other website tracking tools.
- The HHS’ Centers for Medicare and Medicaid Services (CMS) will introduce new cybersecurity requirements as a condition for participation in the Medicare and Medicaid programs.
- The HHS has confirmed that the CMS will do this, but it is still on the to-do list.
- State Attorneys General will step up enforcement of HIPAA compliance and will impose more financial penalties against healthcare organizations that have failed to meet minimum standards for cybersecurity.
- I was wrong on this one, as only New York increased its enforcement activities to a significant degree, fining 4 healthcare organizations for cybersecurity failures in 2024, including one multi-state action with Connecticut and New Jersey. California and Indiana both announced two penalties for cybersecurity failures.
HIPAA Predictions for 2025
The administration change makes predictions for 2025 somewhat challenging. Robert F. Kennedy Jr. will take the helm as the new HHS Secretary, and he has controversial views on certain aspects of healthcare and public health, and President Trump has committed to reducing rather than increasing regulations. The last Trump administration had a policy that two regulations should be scrapped for every new regulation introduced, and this time around, Trump has stated that the policy will be even stricter, with 10 regulations cut for every new one introduced.
That policy could see the 2024 HIPAA Privacy Rule change that strengthened protections for reproductive healthcare information scrapped but even if that does not turn out to be the case, it is hard to see the new administration actively enforcing the new rule. This year is likely to see the Texas Attorney General succeed in his attempts to prevent the HHS from enforcing the Rule in the state of Texas, which is likely to trigger other states with bans on abortion to file similar lawsuits.
The fate of the HIPAA Security Rule update proposed by the OCR in December 2024 lies with the Trump administration. While there is a pressing need to improve cybersecurity in healthcare, it is unclear whether pushing through an update to the HIPAA Security Rule proposed by the Biden Administration will be a priority for the new Trump Administration. OCR did not introduce a final rule implementing the HIPAA Privacy Rule changes proposed by the previous Trump administration during the 4-year term after receiving stakeholder feedback on the proposals.
I believe that the pressing need for increased cybersecurity protections in healthcare will see the proposed HIPAA Security Rule update being implemented in some form. While the update could potentially be hurried through, the comment period is likely to be extended past the 60-day deadline to allow more extensive feedback to be collected and a final rule is unlikely to be issued this year; however, the CMS should introduce new cybersecurity requirements as a condition of participation in the Medicare program and I believe a final rule implementing the HIPAA Privacy Rule changes – proposed by the previous Trump administration – will be issued this year.
Due to widespread noncompliance with the risk analysis requirement of the HIPAA Security Rule and its vital importance for healthcare cybersecurity, this Biden Administration enforcement initiative should continue this year, and the failure to conduct a comprehensive and accurate risk analysis will be the most common HIPAA violation to result in a financial penalty. This year should also see the return of the HIPAA compliance audit program, as suggested by the previous administration. The huge data breach at Change Healthcare and the colossal impact the ransomware attack had on the U.S. healthcare system is likely to make audits of large healthcare organizations the priority.
Regarding HIPAA enforcement, considering last year’s near-record-breaking number of enforcement actions, there will likely be a reduction in the number of fines and penalties imposed by OCR for HIPAA violations in 2025. At the state level, New York is likely to continue to be the most active state in this area, increasing the number of penalties for cybersecurity failures by New York hospitals.
HIPAA Enforcement in 2024
OCR has been enforcing HIPAA compliance more aggressively in recent years, imposing more financial penalties for HIPAA violations. In her end-of-year recap, OCR Director Melanie Fontes Rainer confirmed that 2024 was almost a record year for HIPAA enforcement with more than $9.9 million collected in 22 settlements and civil monetary penalties, including a $4,750,000 settlement with Montefiore Medical Center to resolve multiple HIPAA Security Rule violations. Six of the 22 enforcement actions were not announced by OCR until January 2025.
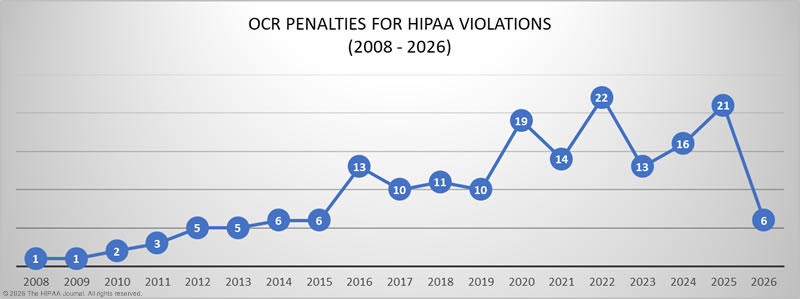
In contrast to 2022, when 17 of the 22 financial penalties resolved violations of the HIPAA Right of Access – the failure to provide individuals with timely access to their medical records and only charge a reasonable cost-based fee – only 5 of OCR’s 22 closed enforcement actions in 2024 resolved HIPAA Right of Access violations. After a successful challenge to the penalty imposed on University of Texas MD Anderson Cancer Center in 2019, which saw the financial penalty vacated, OCR has appeared reluctant to pursue penalties for HIPAA Security Rule violations, with only 2 enforcement actions for alleged Security Rule violations in 2021 and a further 2 in 2022. In 2023, 5 of the 13 enforcement actions were for alleged HIPAA Security Rule violations, and out of the 19 HIPAA enforcement actions (out of 22) that have been announced so far by OCR, 14 resolved alleged HIPAA Security Rule violations, with the most common violation the failure to conduct a comprehensive and accurate risk analysis.
OCR recently made the risk analysis requirement of the HIPAA Security Rule an enforcement priority, after years of evidence that this was one of the most common HIPAA violations. In the last round of HIPAA audits in 2016-2017, OCR found that most audited healthcare organizations were not fully compliant with this Security Rule provision, either by never having conducted a risk analysis, failing to conduct a risk analysis regularly enough, or by not conducting a comprehensive and accurate risk analysis covering all systems where ePHI is collected, stored, or transmitted.
OCR has faced challenges with HIPAA enforcement due to a significant increase in its workload while its budget has remained flat. OCR investigates all data breaches of 500 or more records, and data breaches have increased at an alarming rate. OCR explained in its annual report to Congress that since fiscal year 2017, it has received a 100% increase in large breach reports, largely driven by an increase in hacking incidents, especially ransomware attacks. In 2021, 75% of the breaches of 500 or more records were due to hacking incidents compared to 41.6% of data breaches in 2017, and the problem has been getting worse rather than better. In 2023, 81.1% of the 747 reported large data breaches were due to hacking incidents, and the provisional data for 2024 (up to Nov 30, 2024) show 81.3% of the reported data breaches were hacking/IT incidents.

In addition to having to investigate more than twice the number of data breaches as in 2017, between 2017 and 2021, OCR also saw a 28% increase in complaints about potential HIPAA violations, yet aside from annual increases for inflation, OCR is working with the same budget as in 2017. OCR explained in its 2022 report to Congress that it has been forced to decrease its enforcement staff by 45%, and with its resources under incredible strain, that naturally has an impact on the speed of investigations and the number of cases where financial penalties can be pursued. Further, with such an incredibly heavy workload, it has been difficult to retain staff.
OCR can increase funding through its enforcement actions, as the funds collected can be used for enforcement purposes, but fines and settlements are unpredictable. In addition, penalty amounts have fallen considerably. Despite OCR closing more than twice the number of HIPAA data breaches and complaint investigations in 2024, with financial penalties as in 2017, the funds raised through those actions were 49% lower than in 2017 and 65.5% lower than in 2018. The average HIPAA fine in 2017 was approximately $1,939,000, and $2,607,000 in 2018. In 2023, the average HIPAA penalty was $321,000, and around $450,000 in 2024.
The decrease in penalty amounts is due to a reinterpretation of the language of the HITECH Act, which has seen the maximum penalties for HIPAA violations reduced in three of the four penalty tiers. OCR has asked Congress to increase the maximum penalties for HIPAA violations and is constantly pushing to have its budget increased, but there are no indications at present that additional funding will be provided, nor that penalty amounts will be increased as requested.
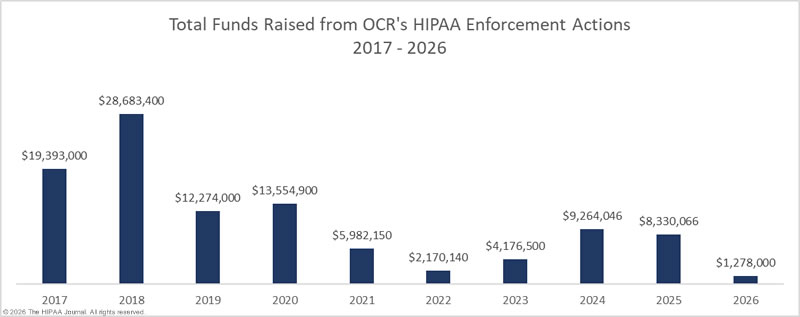
* The OCR Director stated that $9.9 million was raised in enforcement actions in 2024, although some of the enforcement actions closed in 2024 were not announced until 2025.
Budgetary pressures have forced OCR to look at other ways of increasing funding, such as improving efficiency and productivity by restructuring to get better use of its existing resources. In 2023, OCR restructured and created a new enforcement division, and that appears to have been effective; however, restructuring alone has not been enough to make much of a dent in the backlog of data breach investigations. The new enforcement initiative targeting risk analysis compliance should make a difference. Investigations of data breaches require a lot of resources, as do enforcement actions. By targeting the risk analysis requirement, the most common HIPAA Security Rule violation, OCR will be able to 1) hold more HIPAA-regulated entities to account for violating this essential Security Rule requirement, and 2) be able to investigate data breaches more quickly, helping to clear the backlog a lot faster. As of May 31, 2025, OCR has announced 16 penalties for HIPAA violations, including 9 under the new risk analysis enforcement initiative.
State attorneys general also enforce the HIPAA Rules, and in 2023, 16 investigations resulted in settlements or civil monetary penalties to resolve violations of HIPAA and state privacy laws. There was actually a reduction in State Attorney General enforcement actions in 2024, with only 9 actions resulting in financial penalties. Last year, only State Attorneys General in California, Indiana, New York, and Washington took action against HIPAA-regulated entities for cybersecurity and privacy failures, with New Jersey and Connecticut also participating in one multi-state action.
New York was the most active, with 3 enforcement actions and $1,500,000 collected in settlements, plus a share of a $450,000 settlement from its multi-state action with Connecticut and New Jersey. Washington collected $5,000,000 in one enforcement action, and California collected $11,760,000 in its three enforcement actions, including a $6,75,000 financial penalty for Blackbaud. In October 2024, New York implemented new legislation that requires general hospitals in the state to implement a raft of new cybersecurity measures. Statewide IV and Statewide V funding totaling $650 million was released to help those hospitals implement the new cybersecurity requirements, and in 2025, it should start to become clear how effective that initiative has been.
The State of HIPAA Compliance
OCR has conducted two rounds of compliance audits to assess the state of HIPAA compliance since the HIPAA Privacy and Security Rules were enacted. The second phase of HIPAA audits was launched in 2016, and while OCR has stated its intention to conduct an ongoing program of compliance audits, they have failed to materialize due to budget constraints. Last year, the OCR Director said HIPAA compliance audits would be recommencing in 2024, although the rekindled audit program does not appear to have materialized.
The 2016-2017 HIPAA audit program identified many areas of noncompliance, with most covered entities found to have failed to achieve full compliance in the following areas:
- The HIPAA Security Rule risk analysis and risk management requirements
- Timely breach notifications and adequate content of breach notifications
- Prominent posts of Notices of Privacy Practices on websites and insufficient content of those notices
- Timely responses to individuals’ right of access requests and charges for copies of medical records
It has been 7 years since the second phase of the compliance audits came to an end, and many of the compliance issues identified by OCR continue to pose problems for HIPAA-regulated entities, as can be seen in OCR’s enforcement actions, which give an indication of the current state of HIPAA compliance.
Most Common HIPAA Violations in OCR’s Enforcement Actions (2020-2024)
| HIPAA Violation | Enforcement Actions |
| HIPAA Right of Access | 50 |
| Risk Analysis | 25 |
| Reviews of System Activity | 10 |
| Risk Management | 6 |
| Notice of Privacy Practices | 4 |
| Business Associate Agreements | 4 |
| Lack of Technical Safeguards | 4 |
| Audit Controls | 3 |
| Impermissible Disclosure on Social Media/Internet | 3 |
| Technical and Nontechnical Evaluation | 3 |
| HIPAA Privacy Rule Policies | 2 |
| Policies and Procedures for Responding to Security Incidents | 2 |
| Appointment of a HIPAA Privacy Officer | 2 |
The above list of the most common recent HIPAA violations identified in OCR enforcement actions includes many that could have been avoided with HIPAA training, such as HIPAA Right of Access violations and ineffective HIPAA compliance program management. The number of risk analysis failures demonstrates a need for updated guidance on exactly what a risk analysis should entail, as well as more specific regulatory requirements, as have been included in the proposed 2024 HIPAA Security Rule update.
Top HIPAA Security Rule Compliance Challenges in 2025
 Complying with all HIPAA provisions and implementation specifications can be a challenge, especially for smaller healthcare providers and business associates who do not have extensive resources to devote to HIPAA compliance.
Complying with all HIPAA provisions and implementation specifications can be a challenge, especially for smaller healthcare providers and business associates who do not have extensive resources to devote to HIPAA compliance.
While there are many aspects of the HIPAA Security Rule that can prove challenging, there are some common areas of vulnerability that are identified time and again in OCR’s investigations.
HIPAA compliance software can simplify and automate compliance and provide comprehensive risk management processes for both compliance officers and practice managers to follow, covering all provisions and implementation specifications of the HIPAA Rules to ensure that nothing is missed.
Risk Analyses
The HIPAA Security Rule mandates that regulated entities must conduct a comprehensive and accurate organization-wide risk analysis to identify risks and vulnerabilities to electronic protected health information (ePHI). The risk analysis process needs to be ongoing, and the best practice is to conduct these at least annually or as needed, such as following any material change to policies, procedures, technologies, and business practices. The risk analysis must be comprehensive, which means an organization must identify all ePHI within the organization, all systems that touch ePHI, and all external ePHI created, received, maintained, or transmitted by business associates. All threats to that information must be identified, including human, natural, and environmental threats to ePHI and the systems on which the ePHI is stored. The HHS has developed a Security Risk Assessment Tool to help regulated entities with this vital process.
Risk Management Processes
Once risks and vulnerabilities have been identified, they must be subjected to risk management processes to reduce them to a low and acceptable level in a timely manner. Risks must be assessed and remediations prioritized to ensure that the risks most likely to be exploited are addressed first. Risk management processes also need to be extended to third parties – business associates – which means performing due diligence on vendors throughout the supply chain and implementing processes to identify, assess, and manage vendor risk at each stage of the vendor life cycle – onboarding, ongoing, and offboarding. Reducing risk exposure from vendor relationships is one of the biggest security challenges in healthcare in 2025 and a pressing issue, as hackers are actively targeting the supply chain.
Technical Security Controls
The HIPAA Security Rule does not currently specify the technical controls that should be implemented to secure systems containing ePHI, as these need to be based on the specific IT architectures of each regulated entity. It is the responsibility of each regulated entity to ensure that appropriate security controls are implemented and that they are effective at reducing risk. Security controls need to be regularly subjected to security assessments to make sure they have been implemented correctly, are operating as intended, and are achieving the desired outcome. HIPAA-regulated entities should conduct regular vulnerability scans and penetration tests to gain a better understanding of their security posture and identify security gaps that need to be addressed.
Audit Controls and Information System Activity Reviews
All IT systems that touch ePHI must have audit controls and create logs of system activity, and reviews of information system activity should be conducted on audit logs, access reports, and security incident tracking reports on an ongoing basis. Despite information system activity reviews being a requirement of the HIPAA Security Rule, OCR’s investigations have revealed many organizations only conduct reviews on an ad-hoc basis in response to potential security incidents. Regular reviews allow HIPAA-regulated entities to rapidly identify unauthorized access to ePHI by malicious insiders and hackers. All too often, regulated entities discover unauthorized access by insiders and hackers that has been ongoing for many months.
Access Controls
Technical policies and procedures need to be developed, implemented, and maintained for all electronic information systems that contain or allow access to ePHI to only permit access to persons or software programs that have been granted access rights per the organization’s access management policies and procedures. Access controls need to be based on the principle of least privilege, and access must be promptly revoked when individuals leave employment or no longer require access to ePHI. Ineffective access controls can be exploited by malicious actors to move laterally within networks and view or steal huge volumes of ePHI.
Staff Cybersecurity Training
Increased staff cybersecurity training is needed to teach employees about the different cybersecurity threats to PHI, which are increasing due to AI. Cybersecurity training helps the staff identify common threats like phishing, malware, and ransomware, and the role they must play in ensuring the cybersecurity of their organization. It also covers how to protect PHI, focusing on secure data handling, strong password practices, and spotting the signs of a security breach. The aim is to make sure all staff members know about these threats and how to prevent them to keep their networks and patient data safe and secure.
Challenges with HIPAA Privacy Rule Compliance in 2025
There are several aspects of HIPAA Privacy Rule compliance that are likely to prove challenging for HIPAA-regulated entities in 2025. OCR has confirmed that these HIPAA Privacy Rule issues are still – or will be – enforcement priorities.
Timely Access to Medical Records
The 2016 HIPAA compliance audits identified widespread noncompliance with the HIPAA Right of Access, and increasing numbers of complaints were being received from individuals struggling to obtain copies of their medical records. OCR launched a new compliance initiative in 2019 targeting noncompliance with the HIPAA Right of Access, and the bulk of OCR’s subsequent enforcement actions to date have been for noncompliance with the HIPAA Right of Access. OCR is continuing with this enforcement initiative, and further, the proposed Privacy Rule changes that are expected to be finalized in 2025 will likely see the time frame for providing records decrease from 30 days to 15 days.
Tracking Technologies
In 2022, investigations of tracking technologies on websites revealed the extent to which these third-party code snippets were being used by healthcare organizations. The code snippets collect valuable data on website and web app user activity, which can be used to improve those services; however, the code can also collect identifiable health information and transmit that information to third parties. Those third parties typically do not sign business associate agreements, and using the code without a BAA in place or first obtaining consent from individuals to share that information can violate privacy.
OCR issued guidance on tracking technologies and HIPAA in December 2022, and the OCR Director issued a statement confirming OCR will be enforcing this aspect of compliance. Many lawsuits have been filed against healthcare providers over privacy violations due to the use of tracking technologies, some of which have resulted in multi-million-dollar settlements. OCR’s guidance was challenged in court by the American Hospital Association, and a Texas judge ruled that OCR’s guidance was unlawful, partially vacating the guidance. While the ruling means that the tools can be used on unauthenticated web pages, tracking tools must not be used on authenticated web pages and apps, such as patient portals.
Disclosures of Reproductive Health Information
The decision of the Supreme Court in Dobbs v. Jackson Women’s Health Organization and the overturning of Roe v. Wade removed the federal right to abortion, leaving it to individual states to decide on the legality of abortion in their respective states. As of January 2025, 19 states have implemented total bans on abortions or have restrictions on abortions earlier than the standard set by Roe v. Wade.
There is considerable concern that anti-abortion states may attempt to take legal action against healthcare professionals for facilitating terminations in states where abortion is legal as well as prosecuting individuals who travel out of state to have legal abortions in more permissive states. OCR was concerned that the threat of criminal activity may prevent some patients from sharing important health information with their healthcare providers. Consequently, OCR finalized a new HIPAA Privacy Rule update in 2024 to strengthen reproductive health information privacy, the compliance date for which was December 23, 2024. Covered entities are now only permitted to disclose reproductive health information (other than for TPO purposes) to third parties who attest the disclosure will not be used to prosecute individuals or facilitators of terminations in states where abortions are legal. False attestations are considered wrongful disclosures under §1177 of the Social Security Act.
Staff HIPAA Training
The annual Verizon Data Breach Investigations Report highlighted the extent to which data breaches are caused by human error. Out of all data breaches analyzed by Verizon in 2024, 68% involved a non-malicious human element. Those data breaches include misconfigurations, responses to phishing and social engineering attacks, failures to set strong passwords, and other mistakes. These mistakes often expose ePHI and make it easy for hackers to gain access to healthcare networks. The only way of tackling human error is through education. The HIPAA Privacy Rule requires regulated entities to provide training on HIPAA policies relevant to each individual’s role, while the HIPAA Security Rule requires a security awareness training program. In the case of the latter, increasing the frequency of training can help create a security culture and eradicate bad security practices.
Looking Forward – Pending Changes to the HIPAA Rules
While updates to the HIPAA Rules are made fairly infrequently, there are pending changes to the HIPAA Privacy Rule that are expected to be finalized in 2025. OCR has taken steps to improve the privacy protections for reproductive health information through new HIPAA rulemaking, and the HHS’ Centers for Medicare and Medicaid Services (CMS) has proposed updates to transaction code sets to enable the electronic transmission of healthcare attachment transactions. States are also introducing new laws to better protect the privacy of state residents and ensure they are notified quickly in the event of privacy breaches, while New York has introduced new cybersecurity requirements for general hospitals. Staying up-to-date with changes to federal and state laws and ensuring compliance will be an ongoing challenge.
In January 2024, OCR published its healthcare cybersecurity performance goals (CPGs), which consist of two sets of goals—essential and enhanced. The intention is to encourage healthcare organizations to implement measures to improve baseline cybersecurity in healthcare, starting with the measures that will have the greatest impact on security posture. As more organizations adopt these voluntary goals, hacking incidents should start to reduce, although it is likely to take further regulatory requirements – the proposed HIPAA Security Rule update – to force healthcare organizations to adopt cybersecurity best practices before hacking incidents start to significantly reduce. Funds must also be made available to help smaller healthcare organizations and rural and critical access hospitals implement those requirements.
While the proposed HIPAA updates are intended to improve the privacy and security of personally identifiable information and reduce the administrative burden on HIPAA-regulated entities, they are a cause of concern for many HIPAA-regulated entities that will have to spend considerable time and effort implementing the changes and ensuring their employees are fully trained. For smaller healthcare organizations and rural hospitals, the financial and operational burdens of compliance will be a big concern, which is why the HHS needs a grant program to help them with the cost of compliance.
The HHS will provide a grace period to allow the changes to be implemented before compliance becomes mandatory, but it is important to start updating policies and procedures as soon as possible to ensure compliance with these new requirements to ensure the deadlines are not missed.
Steve Alder, Editor-in-Chief, HIPAA Journal





