What is CMMC Compliance?
Following a recent review of the Cybersecurity Maturity Model Certification (CMMC) framework, the requirements for CMMC compliance have changed considerably. This blog discusses the reasons for the change, what it means for companies in the Defense Industrial Base, and what prime contractors and subcontractors now have to do to become CMMC 2.0 compliant.
The history of government procurement goes back to the 18th Century and is – some claim – enshrined in Article 6 of the U.S. Constitution. Over the years, as the number of government agencies grew, each agency developed its own acquisition guidelines – making it complicated for suppliers and contractors in the private sector to do business with different government agencies.
To resolve the complexity of supplying goods and services to different government agencies, the Federal Acquisition Regulation was introduced in 1984 (PDF) to “provide for coordination, simplicity, and uniformity in the Federal acquisition process”. However, supplying goods and services to government agencies has continued to be complicated due to frequently moving goalposts.
How We Got to CMMC 1.0
Technology providers and IT service providers have experienced more moving goalposts than most in the past twenty years. Already having to comply with the FIPS 140 standard for cryptography, from 2002 contractors had to also comply with the Federal Information Security Management Act (FISMA) – which initially required compliance with FIPS 199/200 and NIST SP 800-53, before being expanded to require compliance with sections of NIST SP 800-37, 800-39, 800-171, and 800-53A.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
From 2011, contractors who supplied cloud-based products and services to government agencies were required to comply with FedRAMP, and then – from 2013 – all providers to the Department of Defense were required to meet the requirements of the Defense Federal Acquisition Regulation Supplemental (DFARS) to protect controlled unclassified information (CUI) on non-federal systems. Additionally – from 2016 – DoD contractors had to self-assess compliance with NIST SP 800–171.
According to a news item published in 2017, only around 60% of DoD contractors complied with DFARS requirements, raising concerns about the security of government data. This prompted the Office of the Under Secretary of Defense for Acquisition and Sustainment to publish an interim rule requiring contractors to obtain third-party certification of their cybersecurity capabilities via the Cybersecurity Maturity Model Certification (CMMC 1.0) framework. Contractors that failed to obtain CMMC compliance certification would be excluded from applying for future DoD contracts.
How CMMC 1.0 Got to CMMC 2.0
The timing of CMMC 1.0 was unfortunate as it coincided with the height of the COVID-19 pandemic. Originally scheduled to come into effect in July 2020, the five-stage CMMC 1.0 framework was also criticized for a lack of “sufficient clarity and predictability in key areas” which – it was claimed – would unnecessarily generate confusion, delay, and associated costs, and potentially reduce the security of products and services supplied to the DoD and associated agencies.
Furthermore, at the time CMMC 1.0 was due to come into effect, the CMMC Accreditation Body had not yet appointed or trained Certified Third Party Assessment Organizations (C-3PAOs) responsible for assessing and verifying CMMC compliance nor revealed the process by which contractors would be certified as CMMC compliant. Contractors were told to continue self-assessing CMMC compliance under the previous DFARS model but were warned there would be audits to verify compliance.
The effective date of CMMC 1.0 was pushed back to September 2020 and was further postponed before it was announced (in December 2020) that CMMC would only apply to seven pilot contracts for which contractors would require C-3PAO certification. Almost a year later in November 2021, a “strategic direction” for CMMC was announced “simplifying the CMMC standard and providing additional clarity on cybersecurity regulatory, policy, and contracting requirements”. As it transpired, the strategic direction was a complete review of the CMMC framework and CMMC 2.0 was born.
What Does CMMC 2.0 Consist Of?
With the caveat that CMMC 2.0 is going to be rolled out over five years (2021 to 2026) and is subject to change along the way, CMMC 2.0 is more understandable than its predecessor and therefore more likely to effectively strengthen the cybersecurity of the Defense Industrial Base – the name given to the worldwide supply chain that designs, develops, produces, delivers, and maintains weapons, systems (including computer systems), and components to meet DoD requirements.
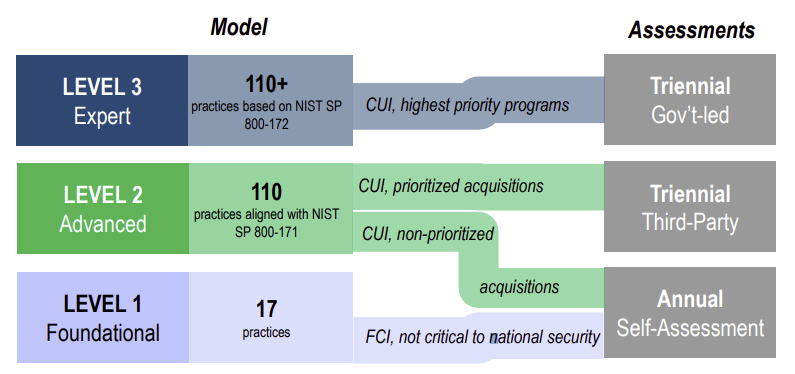
CMMC 2.0 consists of three progressively sophisticated levels depending on the type of goods and services being designed, developed, produced, delivered, and maintained, or the nature of information being stored on contractors´ servers:
| CMMC 2.0 Framework | Requirements |
| Level 1 – Foundation. For companies with access to Federal Contract Information (FCI) that requires protection, but that is not critical to national security. | Contractors and subcontractors will be required to comply with 48 CFR 52.204-21 . |
| Level 2 – Advanced. For companies with access to Controlled Unclassified Information (CUI) that – although not classified – requires protection from unauthorized access and disclosure. | Contractors and subcontractors will be required to comply with NIST SP 800-171 Revision 2 |
| Level 3 – Expert. This level is reserved for companies with access to CUI contracted to work on high priority programs. Note: The requirements for this Level are still being finalized. | Contractors and subcontractors will be required to comply with NIST SP 800-171 Revision 2 and a yet-to-be-determined subset of NIST SP 800-172. |
In order to accelerate the roll-out of CMMC 2.0, companies that do not yet meet the criteria for Level 1 contracts will be allowed to submit a time-limited Plan of Actions and Milestones (POA&M) in their applications, while companies that that do not yet meet the criteria for Level 2 contracts can apply for time-limited waivers if they have already obtained FedRAMP or FIPS 140 certification. Waivers will be granted on a case-by-case basis and are subject to senior DoD approval.
How to Become CMMC 2.0 Compliant
Achieving Level 1 and Level 2 CMMC compliance looks relatively straightforward. Level 1 CMMC compliance consists of seventeen best practices within six “domains” that most companies should already have in place to protect their own corporate data. The six domains are:
- Access Controls
- Identification and Authentication
- Media Protection
- Physical Protection
- System and Communications Protection
- System and Information Integrity
Level 2 CMMC compliance is a little more involved as it consists of eight further domains (called “families” in SP 800-171 r2) plus additional best practices and processes in Level 1 domains. There is also a significant amount of documentation. The eight further domains are:
- Awareness and Training
- Audit and Accountability
- Configuration Management
- Incident Response
- Maintenance
- Personnel Security
- Risk Assessment
- Security Assessment
As mentioned in the table above, the requirements for Level 3 CMMC compliance are still being finalized. Until such time as a Final Rule is published with the Level 3 requirements, the DoD will not require this Level for federal contracts.
How CMMC Compliance is Certified
Although one of the original intentions of CMMC was to eliminate self-assessments, companies will still be allowed to self-assess compliance with CMMC 2.0 Level 1. However, the DoD will require annual self-assessments to be accompanied by an affirmation from a senior company official that the company is meeting the requirements of 48 CFR 52.204-21. The DoD has also stated its intention that self-assessments and affirmations are registered in the Supplier Performance Risk System.
Self-assessment will also be allowed for some subsets of Level 2 contracts, although the majority of Level 2 contracts will increasingly require companies to acquire CMMC compliance certification from a C-3PAO as more third-party assessment and certification organizations are appointed and trained. Companies applying for Level 2 contracts requiring certification will also have to undergo triennial assessments by a C-3PAO to verify ongoing CMMC compliance.
Although the criteria for Level 3 CMMC compliance have yet to be finalized, the DoD will be directly responsibility for certifying and assessing companies applying for Level 3 contracts.
The Benefit of CMMC Compliance Certification for HIPAA Covered Entities and Business Associates
Although it is unlikely HIPAA Covered Entities and Business Associates would apply for DoD contracts, most already fulfil the majority of requirements for Level 2 CMMC compliance certification by complying with the HIPAA Security Rule. Therefore, only a minimal amount of effort would be needed to reach the stage of full CMMC 2.0 compliance – and there is a benefit for doing so.
In January 2021, an amendment to the HITECH Act gave the HHS´ Office for Civil Rights the discretion to reduce financial penalties and the administrative burden of Corrective Action Plans if a Covered Entity or Business Associate experienced a security-related HIPAA violation despite having implemented a recognized security framework. To qualify for relief from HIPAA penalties, organizations have to demonstrate at least twelve months compliance with –
“Standards, guidelines, best practices, methodologies, procedures, and processes developed under section 2(c)(15) of the NIST Act, the approaches promulgated under section 405(d) of the 2015 Cybersecurity Act, and other programs that address cybersecurity and that are developed, recognized, or promulgated through regulations […] consistent with the HIPAA Security Rule.”
As there are no HHS-accredited certifications for HIPAA compliance, obtaining a Level 2 CMMC compliance certification appears to be one of the simplest ways for Covered Entities and Business Associates to demonstrate compliance with a recognized security framework. It is certainly a process that Covered Entities and Business Associates who already comply with the Security Rule may wish to look further into.
CMMC Compliance FAQs
Where can I find further information about what is included in Level 1 and Level 2 CMMC assessments?
The Office of the Under Secretary of Defense for Acquisition and Sustainment has an online documentation page from which you can download a CMMC Level 1 Self-Assessment Guide and a CMMC Level 2 Assessment Guide. These two guides explain the criteria for each assessment level and suggest ways in which companies can meet the requirements.
When might the requirements for CMMC Level 3 be announced?
At present, the next CMMC Interim Rule is forecast for publication in March 2023. It is not known yet whether this will include the requirements for CMMC Level 3 or address other outstanding issues such as how companies outside the United States can become certified as CMMC compliant.
If our company achieves Level 2 CMMC compliance, do any subcontractors we use also have to be Level 2 CMMC compliant?
This depends on what information is shared with or disclosed to the subcontractor. If your company shares or discloses CUI, the subcontractor(s) will have to be Level 2 CMMC compliant. If your company shares or discloses FCI, the subcontractor will have to be Level 1 CMMC compliant. If you company does not share or disclose CUI or FCI, there is no subcontractor compliance requirements.
If our company operates in multiple locations, but only two locations have access to CUI, does every location have to be assessed for CMMC compliance?
Only the two locations that have access to CUI need to achieve Level 2 compliance. The remainder can be omitted from the CMMC certification process unless any have access to FCI – in which case a CMMC Level 1 self-assessment and affirmation should be included in the contract application.
How does NIST SP 800-171 r2 (required for CMMC Level 2 certification) differ from the HIPAA Security Rule?
Not a lot. Many of the differences are subtle (i.e., employees should be trained on recognizing insider threats as part of their security and awareness training) except where NIST families exist that do not appear in the Security Rule (i.e., Personnel Security). However, although it has been suggested that NIST SP 800-171 r2 can be used to assess compliance with the Security Rule, this can depend on how Covered Entities and Business Associates have applied the addressable implication specifications of the Administrative, Physical, and Technical Safeguards.



