Hacking and Phishing Attacks Continue to Plague Healthcare Organizations
Hacks, phishing attacks, malware, ransomware, insider incidents, and W-2 scams – cyberattacks on healthcare organizations are now coming from all angles. Attacks are also happening much more frequently than in years gone by. The healthcare industry is clearly under attack and is being extensively targeted by cybercriminals. As long as it remains profitable to do so, those attacks will continue.
The value of healthcare data may have fallen with a glut of stolen data listed for sale on darknet marketplaces, but large healthcare databases still net cybercriminals considerable profits. Furthermore, cyberattacks on healthcare organizations are easy in many cases due to relatively poor defenses, outdated operating systems, poor patch management practices, and a lack of cybersecurity and anti-phishing training for employees.
2016: A Torrid Year for The Healthcare Industry
2016 may not have been the worst year for healthcare industry data breaches in terms of the number of healthcare records stolen, nor did we see the worst ever healthcare industry data security incident; however, 2016 saw more healthcare data breaches than any other year.
More healthcare data breaches were reported in 2016 than in 2015, and even the total from 2014 – widely reported as ‘The Year of the Healthcare Data Breach’ – was surpassed.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Ransomware was extensively used to attack healthcare organizations in 2016. In February, Hollywood Presbyterian Medical Center was attacked. A ransom payment of $17,000 was paid to obtain the keys to unlock encrypted files. MedStar Health System also suffered a huge ransomware attack that resulted in more than 260 of its facilities having to work without computers while the infection was resolved.
Insiders also played a major role in healthcare data breaches in 2016. According to the Breach Barometer from Protenus for 2016, 48% of incidents involved insiders.
While the threat from within cannot be ignored, the most serious data security incidents were reported as hacks. Out of the 12 largest healthcare data breaches of 2016, three quarters were due to hacking/IT incidents. Hacks and IT incidents also accounted for 87% of the total number of records exposed or stolen for the year.
The Main Causes of Healthcare Data Breaches
While much attention is focused on vulnerabilities in software and operating systems – which are often exploited to gain access to sensitive data – the other main threat is phishing.
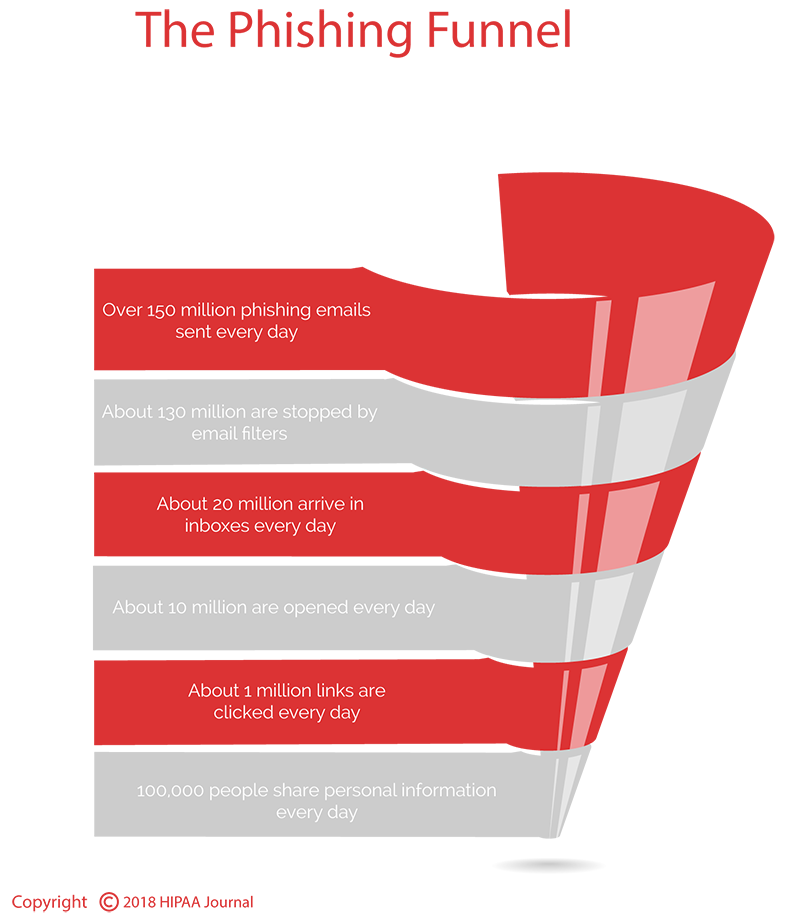
Phishing is an easy way to gain access to healthcare networks. According to PhishMe, 91% of cyberattacks start with a phish. Knowledge of software vulnerabilities, SQL injection, and cross-site scripting is not needed. Malware (or ransomware) can be easily hired and distributed with little in the way of skill required. All that is required is an email with a link or infected attachment. Those emails are sent in massive spam campaigns, and many get delivered to healthcare employees’ inboxes.
Phishing attacks use tried and tested social engineering techniques to get users to open malicious attachments and click on links to phishing sites and malware-downloading webpages.
Even with cybersecurity awareness training, employees are still fooled by phishing emails. Links are clicked out of curiosity, fear, urgency, and for recognition and rewards, entertainment, and to take advantage of opportunities, according to PhishMe.
Preventing healthcare data breaches is a complex process requiring multi-layered security defenses, next generation firewalls, endpoint security, antivirus and anti-malware solutions and extensive training for healthcare employees.
However, the volume of healthcare data breaches reported last year clearly demonstrates that healthcare organizations are struggling to implement the appropriate technologies, policies and procedures to repel attacks.