Healthcare Providers Targeted in Evernote Phishing Campaign
A malicious phishing campaign has been identified that is targeting healthcare providers. The emails have an Evernote-themed lure to trick recipients into downloading a Trojan file that generates a login prompt to steal credentials.
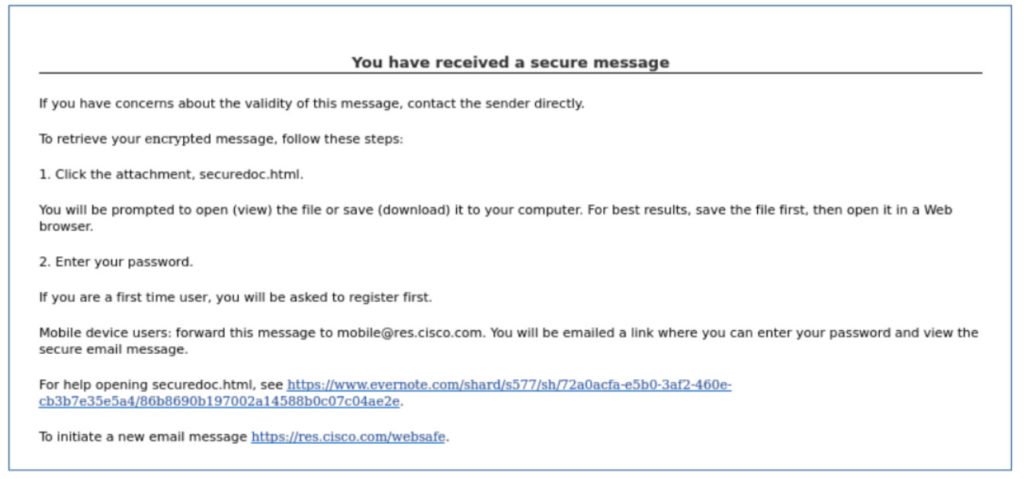
The Health Information Cybersecurity Coordination Center (HC3) has recently issued an alert about the campaign which has targeted several healthcare providers in the United States. Malicious emails are sent to targeted organizations that contain a malicious link to an Evernote-themed website. The emails are personalized and the lures used in the phishing emails may vary; however, the emails seen by HC3 have the subject line “[Organization Name] [Date] Business Review” and have a Secure Message theme.
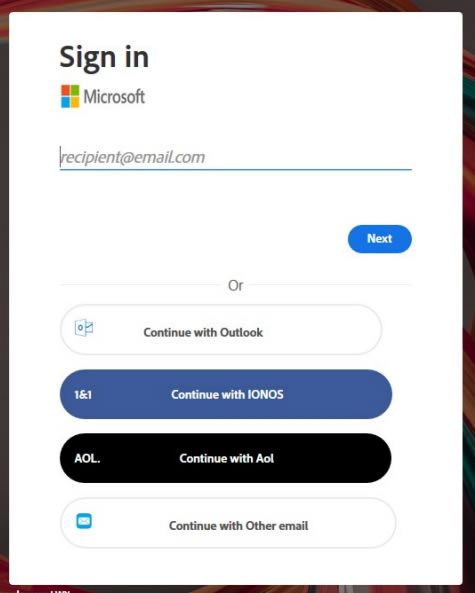
The link included in the email directs the user to the Evernote site, where they are prompted to download an HTML file – called message (3).html. The file includes JavaScript code that renders an Adobe or Microsoft-themed page that attempts to harvest Outlook, IONOS, AOL, or other credentials.
The credentials obtained in phishing campaigns such as this can give cyber threat actors access to email accounts, which can contain significant amounts of sensitive data, including protected health information. Compromised email accounts can be used to conduct phishing attacks internally and can give threat actors the foothold they need to conduct more extensive attacks on the organization. Many ransomware attacks start with phishing emails.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Protecting against phishing attacks requires a combination of measures, including email security solutions for blocking phishing emails, web filters for preventing access to malicious websites where malware is downloaded, antivirus software for identifying Trojans and other malicious code, and multifactor authentication to block unauthorized access to email accounts. It is also important to provide regular security awareness training to the workforce on the risks of phishing and train employees on how to recognize phishing emails.
Further information on this phishing campaign, along with other recommended mitigations, can be found in the HC3 security alert.