HIPAA Breach Report: April 2014
April 2014 HIPAA Breach Summary:
The Breach Notification Rule of the Health Insurance Portability and Accountability Act requires all covered entities, and their Business Associates via their covered entity, to report all data breaches affecting more than 500 individuals to the Department of Health and Human Services’ Office for Civil Rights (OCR). These breaches must be reported with 60 days of the discovery of the breach.
This report contains a summary of the breaches which have been reported to the OCR during the month of April, 2014.
Major HIPAA Breaches in April 2014
April saw the highest number of monthly HIPAA breaches reported for the year – and the most breaches during the past 6 months – with numerous incidents reported including a major data breach at the Indian Health Service (MD) after a laptop containing unencrypted PHI resulted in the potential disclosure of 214,000 individual records.
The second largest breach affected Business Associate, Amerigroup Texas, Inc. (VA), which reported the theft of paper records of 75,026 individuals while the health plan, American Health Inc. (PR) reported a theft that resulted in 17,776 being obtained by thieves.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Business Associate, Triple-S Salud (PR), reported two data breaches for the month after unencrypted portable electronic storage devices were stolen which exposed 5,795 and 7,911 records.
Hackers were able to obtain the PHI of 12,286 patients from Centura Health (CO) as a result of a phishing scam, while a Business Associate of Boston Medical, MDF Transcription Services (MA), accidentally posted PHI on an insecure website which resulted in 15,265 healthcare records potentially being exposed.
Service Coordination, Inc. (MD) reported a hacking incident in which the Social Security numbers and medical information of 10,766 patients were stolen, although the Business Associate believes the individual responsible has been identified and his property has been seized.
Tufts Associated Health Maintenance Organization, Inc. (and Tufts Insurance Company) (MA) reported a suspected insider data breach which exposed names, birthdates and Social Security numbers of 8,830 of the health plans members.
An email hacking incident at Baylor Medical Center – Involving its McKinney, Irving and Plano facilities – exposed a total of 5,542 records while hacking incidents were also reported by Kaiser Permanente Northern CA Department of Research (CA) – 5,178 records – and Sorenson Communications (UT) – 9,800 records were also reported.
An unauthorized disclosure at IHS (MD) exposed 5,000 records, while 5,696 paper records were compromised at OptumRx (IL).
Health plan Triple-S Salud, reported two incidents in April involving 5,795 and 7,911 records after devices containing unencrypted PHI were stolen.
Summary of Reported Breaches
In April, 2014, a total of 440,315 individuals were affected in 36 data/HIPAA/HIPAA data breaches that were reported to the OCR through its breach report portal.
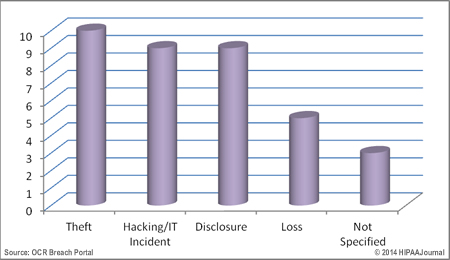
Breach Type
In April, the theft of laptops containing unencrypted data and unauthorized disclosures resulted in the most breaches, although this month has seen hackers launch attacks on healthcare providers and Business Associates, with 9 separate incidents recorded, three of which occurred at Baylor medical facilities in Texas.
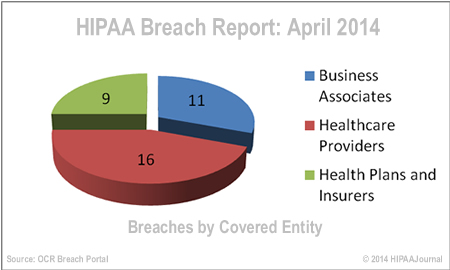
Breaches by Covered Entity
Business Associates were hit hard again in April, registering 11 separate incidents including the 75K-record data breach at Amerigroup. Healthcare providers registered 16 breaches while health plans were hit harder than in previous months with 9 incidents reported, including the 214K-record breach at Indian Health Services.
Location of Breached Information
View Breach Report for March, 2014
Data Source:
HHS OCR Breach Portal: ttps://ocrportal.hhs.gov/ocr/breach/breach_report.jsf;jsessionid=9BF4AF4A0922D09B6E1CF5DAE375E0D0.ajp13w
*Data does not include HIPAA breaches reported to the OCR after the 60-day reporting deadline, as demanded by the Breach Notification Rule. Any errors made by CEs during the submission of HIPAA breach reports via the online portal will be reflected in this breach summary. Figures are deemed to be correct at the time of publishing, although covered entities are permitted to update breach reports after the 60 day deadline as further information becomes available.