The HIPAA Journal Annual Survey
During the last two weeks of December 2024 and the first week of January 2025, we invited subscribers to our newsletter to take part in The HIPAA Journal Survey of Best Practices in HIPAA compliance. One of the objectives of the exercise was to collect insights into HIPAA compliance best practices and identify challenges to HIPAA compliance.
To help meet this objective, we isolated responses from participants who identified as having senior roles in privacy, compliance, administration, and/or IT security. This enabled us to narrow our analysis of responses to those submitted by professionals who are directly involved in – or who have the responsibility for – compliance activities in HIPAA covered organizations.
Our analysis shows that, although larger organizations tend to adopt more compliance best practices than smaller organizations, some may be over-reliant on technical safeguards and underestimate the “human element” in security incidents. Therefore, while smaller organizations can benchmark their compliance activities against those of larger organizations, larger organizations still have challenges to overcome in order to effectively safeguard the privacy and security of Protected Health Informations.
7 Key Takeaways
- Of the respondents that have deployed HIPAA compliance tracking and management software, 58.1% were larger organizations with more than 200 members of the workforce.
- Of the larger organizations using HIPAA compliance software, only four respondents experienced a notifiable data breach affecting more than 100 individuals in the past year.
- Of the respondents that do not use HIPAA compliance software, 40.7% were unable to answer the question about how frequently Business Associate Agreements are reviewed and updated.
- Of all respondents that experienced a notifiable data breach affecting more than 100 individuals in the past year, none had adopted HHS’ HPH Cybersecurity Performance Goals.
- Although most respondents (94.3%) provide annual HIPAA refresher training to members of the workforce, only 79.3% test workforce members on HIPAA knowledge and awareness.
- Although most respondents are completely (12.6%), fairly (50.6%) or somewhat (24.1%) confident their organization’s cybersecurity defenses will prevent cyberattacks, only 29.9% of respondents provide monthly security awareness training.
- Approximately 25% of respondents representing smaller organizations (<200 members of the workforce) said they did not feel adequately supported by management in following HIPAA procedures.
Summary of Survey Findings
HIPAA Compliance Tracking and Management Software
Our interest in analyzing responses in the context of which organizations use HIPAA compliance tracking and management software stems from a survey conducted in Q4 2024 in which 57% of respondents said they were using software for HIPAA compliance tracking and management as opposed to fragmented manual processes, paper-based systems, or no system at all.
While it is not surprising that the majority of respondents that use software to track and manage HIPAA compliance are larger organizations, what is noticeable is that respondents of all sizes that do not use software tended to answer more questions with “don’t know” responses. This was particularly noticeable in questions relating to risk analyses and Business Associate Agreements.
How Management Software Helps Support HIPAA Compliance
Management software helps support HIPAA compliance by managing and tracking the frequency of activities such as risk analyses, workforce training, and reviews of Business Associate Agreements. It is also often used as a repository for HIPAA documentation, policies, and security incident response procedures to help mitigate the impact of a data breach.
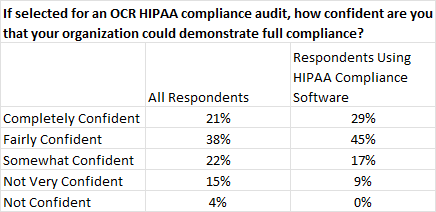
Interestingly, of the respondents that have deployed HIPAA compliance software, only 9% said they would not be very confident of demonstrating full HIPAA compliance if selected for an audit by HHS’ Office for Civil Rights. By comparison, 17% of respondents said they were somewhat confident, 45% said they were fairly confident, and 29% said they were completely confident.
Verification of Business Associate Agreements
At the time the survey was conducted, there were no mandatory requirements to review and update Business Associate Agreements unless a covered entity became aware of a material breach or violation of the business associate’s obligations. This may be about to change if HHS’ proposals to strengthen cybersecurity for electronic PHI (ePHI) are finalized.
Under the proposals, covered entities will be required to obtain annual verification from business associates that they have deployed the (new) technical safeguards required by the HIPAA Security Rule to protect ePHI. Covered entities that are not on top of their Business Associate Agreements will be in violation of the new HIPAA regulations.
HHS’ HPH Cybersecurity Performance Goals
Also included in HHS’ proposals are new regulations to align HIPAA compliance with the Healthcare and Public Health (HPH) Cybersecurity Performance Goals (CPGs). Originally outlined in December 2023, adoption of the CPGs until now has been voluntary – and 43.6% of respondents have either adopted CPGs or plan to within the next 12 months.
While the results of our analysis suggest that adopting HHS’ CPGs is worthwhile to reduce the likelihood of a data breach, respondents with no plans to adopt the CPGs – and those who have not yet decided – may have no option to adopt all the essential CPGs and many of the enhanced CPGs if the measures proposed in HHS’ Notice of Proposed Rulemaking are finalized.
Workforce Knowledge and Awareness
Although the percentage difference in respondents that provide annual HIPAA refresher training and those that test workforce knowledge and awareness is relatively small (~16%), it implies one-in-six HIPAA covered entities are “going through the motions” of providing annual HIPAA refresher training without any consideration of whether the training is absorbed and applied.
It is important to test HIPAA training is absorbed and applied as it has been calculated that 80% of data breaches in healthcare have a “human element” once interactions with phishing emails, misconfigured servers, snooping, and misdeliveries are accounted for. Many of these data breaches are avoidable with greater workforce knowledge and awareness.
The Frequency of Security Awareness Training
One of the reasons for a high percentage of healthcare data breaches having a human element is that security awareness training is not provided often enough. Although the HIPAA Security Rule does not state a frequency, the standard (§164.308(a)(5)) calls for a security and awareness training “program” – implying that security awareness training should be ongoing.
Almost half of respondents to the survey either did not provide any security awareness training (5%), did not know the frequency of training (12%), or provided training annually (28%). While taking the bare data at face value can be misleading, the responses to the survey indicate that many organizations do not include workforce members among their cybersecurity defenses and may be underestimating the human element in security incidents.
Management Support is Vital for HIPAA Compliance
The final three questions in the survey provided some interesting responses inasmuch as 90.9% of respondents stated their workplace culture supported HIPAA compliance, and 80.5% stated the organization’s commitment to enforcing HIPAA policies was either excellent or good. Despite these positive responses, approximately 25% of smaller organizations said they did not feel adequately supported by management.
Management support is vital for HIPAA compliance because it is a “key driver – or inhibitor – affecting the success of security success and security compliance” (JW Brady 2010). It may be a coincidence, but none of the “unsupported” respondents had implemented HHS’ CPGs, only two provided monthly security awareness training, and three respondents in this category had experienced notifiable data breaches in the past twelve months.
Are Larger Organizations Over-Reliant on Technical Safeguards?
It is not possible to arrive at a definitive answer to this question from the responses to the survey because several technology-related questions only offered “yes”, “no”, or “don’t know” options. Therefore, if an organization did not use video conferencing tools to communicate PHI, the response to the question “Are video conferencing tools used for PHI communications HIPAA-compliant?” would be “no”.
However, it is notable that the percentage of organizations that have adopted HIPAA compliant email systems and secured work issued mobile devices with encryption is higher than the percentage of organizations that train employees on how to use email systems in compliance with HIPAA or conduct phishing simulations – further supporting the argument that many organizations may be underestimating the human element in security incidents.
Survey Respondent Profile
Roles of Respondents
The survey drew participation from a range of professionals involved in HIPAA compliance and naturally skewed toward the readership of The HIPAA Journal. The respondents were exclusively working for HIPAA covered entities and involved in HIPAA compliance activities in their organizations. Respondents were classified into the following primary roles:
- Compliance Officer (50.6%): This group formed the largest segment of respondents, reflecting the integral role compliance officers play in ensuring adherence to HIPAA regulations.
- Privacy Officer (10.3%): Privacy officers, HIM managers and C Suite officers responsible for protecting patient information and ensuring confidentiality, represented a significant subset of the respondents.
- Healthcare Administrator/Management (25.3%): These participants, typically involved in organizational operations and decision-making, provided a broader perspective on compliance issues.
- IT/Security Manager (13.8%): This group emphasized the importance of cybersecurity and technological safeguards in HIPAA compliance.
Responsibility for HIPAA Compliance
The level of responsibility for HIPAA compliance among respondents varied, offering insight into how compliance is managed across organizations:
- Solely Responsible (23.0%): A smaller segment of respondents reported being the sole individual accountable for HIPAA compliance at their organizations, indicating a more centralized compliance structure.
- Jointly Responsible (63.2%): The majority of respondents reported shared responsibility for HIPAA compliance, underscoring the collaborative and cross-functional approach many organizations adopt.
- Not Responsible (13.8%): A minority indicated no direct responsibility in managing HIPAA compliance, reflecting roles that might support compliance indirectly or focus on related areas such as IT security.
Professional Experience
Respondents demonstrated a substantial level of expertise in the healthcare and compliance sectors, with the majority of respondents indicating they had held compliance related roles for eight or more years. This depth of experience suggests the survey results are informed by seasoned professionals with a comprehensive understanding of compliance practices and challenges.
Years worked in the healthcare or compliance sector:
- Less than one year – 2.3%
- One to three years – 9.3%
- Three to seven years – 12.8%
- Eight or more years – 75.6%
Organizational Size
The survey captured responses from organizations of varying sizes. Organizations with a designated HIPAA compliance officer reported an average size of 436 employees, suggesting that larger entities are more likely to employ dedicated compliance personnel to meet the complexities of HIPAA requirements.
- <10 employees – 9.2%
- 10-50 employees – 16.1%
- 51-200 employees – 23.0%
- 201-500 employees – 12.6%
- More than 500 employees – 39.1%
Significance of the Respondent Profile
The survey respondent profile reflects a diverse and experienced group of professionals operating within organizations of varying sizes. The breadth of roles, responsibilities, and organizational contexts represented in the survey ensures that the findings provide valuable insights into HIPAA compliance practices across the healthcare sector. By understanding the characteristics of the respondents and their organizations, readers can better interpret the results and draw meaningful conclusions applicable to their own compliance efforts.
HIPAA Compliance Benchmarks
Dedicated HIPAA Compliance Officer or Team
- 87.4% of organizations reported having a dedicated HIPAA compliance officer or team, which is important for ensuring structured compliance efforts.
- 12.6% of organizations lack this role, which may suggest either resource limitations or a reliance on decentralized compliance strategies.
Insights: A dedicated HIPAA compliance officer or team acts as a focal point for all HIPAA-related activities, including policy enforcement, training, audits, and incident response. Organizations without such roles – or who designated the responsibility for HIPAA compliance to the general IT Department – often struggle to maintain cohesive compliance programs, leading to increased risks of non-compliance and regulatory scrutiny.
Oversight of HIPAA Compliance
- 66.3% of organizations assign oversight to a dedicated HIPAA Compliance Officer or team, indicating that many respondents work in a structured compliance environment.
- Healthcare Administrators/Management oversee compliance in 16.3% of organizations, often serving dual roles in operational and compliance responsibilities.
- Other oversight models include:
- IT Departments: 5.8%
- Privacy Officers: 4.6%
- C Suite/Legal Team: 2.3%
- External Consultants: 1.2%
- Other/Don’t Know: 3.5%
Implications: The data highlights that many organizations already have centralized oversight for HIPAA compliance. Assigning this responsibility to a dedicated compliance officer or team ensures accountability, aligns organizational efforts, and provides expertise in navigating regulatory requirements. Organizations with unstructured compliance environments may lack the focus required for robust compliance programs – potentially leading to gaps in training, documentation, and monitoring.
Frequency of HIPAA Compliance Audits
- 54.0% of organizations conduct annual compliance audits – considered a minimum benchmark for effective compliance monitoring.
- Other frequencies reported include:
- As Needed 21.9%
- Bi-annual audits: 14.9%
- Never: 4.6%
- Don’t know: 4.6%
Analysis: Annual audits are a cornerstone of HIPAA compliance. They provide organizations with the opportunity to assess risks and vulnerabilities, ensure documentation accuracy, and verify that safeguards are up to date. Organizations with compliance officers are slightly more likely to prioritize these audits (59.6%). In contrast, entities that do not have a dedicated compliance officer are more likely to conduct unscheduled “as needed” compliance audits.
Covered entities not yet conducting annual compliance audits should note that, among the proposals to update the HIPAA Security Rule, a new implementation specification requires documented compliance audits at least every twelve months.
Approach to HIPAA Compliance
- 69.0% of organizations adopt a proactive approach, implementing regular training, audits, and monitoring.
- 18.4% of organizations take a reactive approach, addressing issues only when they arise.
- 12.6% describe their approach as minimal, citing limited resources and insufficient focus on compliance.
Key Insights: Proactive compliance reflects a mature and strategic mindset. Organizations that invest in regular audits, comprehensive training, and monitoring systems not only reduce the likelihood of violations but also foster a culture of accountability. Reactive or minimal approaches, however, suggest a lack of prioritization and preparedness.
Written Incident Response Plans
- 85.2% of organizations have a written incident response plan for HIPAA violations.
- 8.0% do not, and 6.8% are unsure.
Significance: A written incident response plan is critical for addressing HIPAA breaches effectively and demonstrating regulatory compliance. It provides clear guidelines for identifying, mitigating, and reporting breaches, ensuring a swift and coordinated response. Organizations without such plans are not only at greater risk of operational chaos during incidents but may also face harsher penalties for failing to meet regulatory standards for breach management.
Documentation of Policies and Procedures
- 90.8% of organizations maintain documented HIPAA policies and procedures.
- 5.8% lack documentation, and 3.4% are unsure of their status.
Interpretation: Documenting policies and procedures is essential for supporting HIPAA compliance and serves as evidence during audits or investigations. Organizations that lack documentation or are unsure of its status face significant risks, including non-compliance penalties and operational inefficiencies. Best practices include regularly reviewing and updating documentation to align with evolving regulations and organizational/technological changes.
Business Associate Agreement Usage
- 79.3% of organizations maintain BAAs with all applicable vendors, demonstrating a commitment to ensuring third-party compliance with HIPAA standards.
- 8.1% of organizations do not maintain BAAs, leaving them vulnerable to compliance breaches and potential legal liabilities.
- 12.6% of organizations are unsure if they have BAAs in place, indicating a lack of oversight and awareness in their compliance frameworks.
Significance: The high percentage of organizations maintaining BAAs reflects recognition of their importance in safeguarding Protected Health Information (PHI). However, the 20.7% combined organizations that either lack BAAs or are unsure highlights an area of concern. Without Agreements, organizations face increased risk of non-compliance and penalties.
Frequency of Business Associate Agreement Reviews
- 35.6% of organizations review BAAs as required, aligning with operational or regulatory changes.
- 21.8% conduct annual reviews, ensuring consistent evaluation and updates to meet evolving compliance standards.
- 11.5% conduct reviews every few years. These were mostly respondents from smaller organizations who may have fewer BAAs to manage.,
- 26.5% are unsure of their review frequency, signaling potential gaps in compliance oversight.
- 4.6% never review BAAs, leaving agreements potentially outdated and ineffective.
Best Practices: Under current regulations, regular reviews of BAAs are important to ensure they remain relevant and enforceable. Annual reviews provide a systematic approach, while as-needed reviews address specific changes, such as vendor updates or regulatory shifts. However, if/when proposals to update the HIPAA Security Rule are finalized, an annual review of BAAs may become mandatory.
HIPAA Compliance Tracking and Management Software
- Only 35.6% of respondents to this survey use compliance tracking and management software.
- 50.6% do not use such tools, and 13.8% are unsure of their use.
Interpretation: There is no obvious explanation for the discrepancy between the results of this survey and the one conducted in Q4 2024 in which 57% of respondents said they were using software for HIPAA compliance tracking and management. The low adoption rate among respondents to this survey suggests many organizations are missing an opportunity to enhance compliance efficiency and effectiveness, particularly in complex regulatory environments.
It is also worth repeating the observation from earlier in this analysis that respondents of all sizes who do not use software for HIPAA compliance tracking and management tended to answer more questions with “don’t know” responses.
Certification of HIPAA Compliance
- 19.5% of respondents stated their organizations were certified as HIPAA compliant by an independent third party.
- 65.6% of respondents have not sought certification, while 14.9% of respondents were unsure of their certification status.
Observation: Although certifications of HIPAA compliance are not required by HHS’ Office for Civil Rights, they demonstrate a good faith effort to comply with HIPAA in the event of a HIPAA audit or compliance investigation. Furthermore, fulfilling the criteria for achieving a certification of HIPAA compliance reduces the likelihood of a HIPAA violation or notifiable data breach.
Confidence in OCR Audit Readiness
- 20.7% of respondents are completely confident in their organization’s ability to demonstrate full compliance in the event of an OCR audit.
- 37.9% are fairly confident, while 21.8% are somewhat confident.
- 19.6% expressed low or no confidence in their readiness.
Analysis: It was mentioned previously in this analysis that respondents that have deployed HIPAA compliance software are more likely to express confidence in their readiness for an OCR audit. It is also the case that confidence in audit readiness strongly correlates with a proactive approach to HIPAA compliance, rather than a reactive approach.
Of the respondents that answered they were completely confident in their ability to demonstrate full compliance, 89% also stated their organization has adopted a proactive approach to HIPAA compliance. Similarly, 84% of respondents that answered they were fairly confident in their ability to demonstrate full compliance also stated they had adopted a proactive approach.
Frequency of Risk Analyses
- 11.5% of respondents conduct comprehensive risk analyses “as required”.
- 6.9% of respondents conduct risk analyses every six months, while 55.2% of respondents conduct an annual risk analysis.
- 8.0% of respondents said they conduct risk analyses every two years, while the remaining 18.4% did not know the frequency.
Interpretation: The wide range of responses – and the high percentage of respondents who did not know the frequency of their risk analyses – is likely attributable to the inclusion of the word “comprehensive” in the question. Risk assessments should be conducted whenever there is an operational, regulatory, or technicology change to activities, but – according to §164.306(e) – further risk analyses should be conducted “as needed to continue provision of reasonable and appropriate protection of electronic PHI”.
Notifiable Data Breaches
- 12.6% of respondents reported experiencing a notifiable data breach affecting more than 100 individuals in the past twelve months.
- Of concern is that 8% of respondents – some of whom identified as HIPAA Compliance Officers – did not know if their organizations had experienced a notifiable data breach.
Significance: There is no calculable benchmark for data breaches per organization due to a lack of transparency in breach reporting. It is also the case that benchmarks could be unreliable in this category due to some organizations experiencing multiple data breaches per year. Furthermore, the apparently low percentage of respondents who reported experiencing a notifiable data breach in the past twelve months could reflect the compliance-conscientious nature of respondents (i.e. subscribers to The HIPAA Journal newsletter).
Experience of Ransomware Attacks
- 18.4% of respondents said their organization had experienced a ransomware attack.
- 16.1% of respondents did not know if their organization had ever experienced a ransomware attack.
Analysis: Although larger organizations tend to be the primary targets for ransomware attacks – because they own more data than smaller organizations and have larger attack surfaces – our analysis of responses showed an equal distribution of successful attacks across organizations of all sizes.
Our analysis of “Don’t Know” responses found that the majority originated from respondents who had been in compliance roles for relatively short periods and who may be unaware of historic security incidents.
Adoption of HHS’ HPH Cybersecurity Performance Goals
- 8.0% of respondents have already adopted both the essential and the enhanced Healthcare and Public Health (HPH) Cybersecurity Performance Goals (CPGs).
- 4.6% of respondents have adopted the essential CPGs only, while 31.0% of respondents plan to adopt some or all CPGs within the next twelve months.
- Of the remainder, 9.2% of respondents have no adoption plans, while 47.2% of respondents are undecided or do not know what their organizations’ plans are.
Comment: Until such time as it is known what essential and/or enhanced CPGs will be mandated in HHS’ proposals to update the HIPAA Security Rule, it is difficult for organizations to plan future CPG adoption with any confidence. Nonetheless, 12.6% of respondents have already adopted some or all CPGs and these organizations will be better positioned to adjust their existing measures if necessary if/when HHS’ proposals are finalized.
Organizations that Conduct Phishing Simulations
- 70.1% of respondents said their organizations conduct phishing simulations.
Implication: The implication that almost 30% of organizations in the healthcare industry do not provide effective training on phishing is alarming. Approximately 80% of all healthcare data breaches have a “human element”, and a considerable number of data breaches are initiated by a workforce member interacting with a phishing email.
Confidence in Cybersecurity Defenses
- 12.6% of respondents claim to be completely confident their organization’s cybersecurity defenses will prevent cyberattacks.
- 50.6% of respondents are fairly confident their organization’s cybersecurity defenses will prevent cyberattacks, while 24.1% of respondents are somewhat confident.
- The remainder have little confidence (5.8%) or no confidence (2.3%) in their organization’s cybersecurity defenses, while 4.6% of respondents chose not to answer.
Interpretation: Although 12.6% of respondents were completely confident in their organization’s cybersecurity defenses, this was not the same 12.6% of respondents who had adopted HHS’ HPH Cybersecurity Performance Goals (most of whom responded they were fairly confident).
Our interpretation of these responses – including those who chose not to answer – is that while many organizations adopt appropriate cybersecurity defenses that are capable of preventing cyberattacks, some organizations may be over-reliant on technical safeguards (or over confident in their abilities) and underestimate the “human element” in security incidents.
Workforce Training Benchmarks
Workforce Knowledge Assessments
- 79.3% of respondents test workforce members on their HIPAA knowledge and awareness.
- The remaining 20.7% do not test or do not know if they test workforce knowledge.
Significance: Testing workforce members’ HIPAA knowledge and awareness is a key element of a HIPAA risk assessment. Organizations that are unaware of issues with workforce knowledge are unable to comply with the General Requirements of the HIPAA Security Rule requiring HIPAA covered entities to protect against reasonably anticipated uses or disclosures of electronic PHI that are not permitted or required by the HIPAA Privacy Rule (§164.306(a))
Of interest, respondents who said their organizations did not test workforce knowledge represented organizations of all sizes. Therefore – for the purposes of this question – it is not the case that organizations might not test workforce knowledge due to lack of resources. Many larger organizations still have work to do in this area in order to address compliance challenges.
Annual HIPAA Refresher Training
- 94.3% of respondents stated their organizations provide annual HIPAA refresher training to all members of the workforce.
Comment: While it is encouraging that nearly all respondents to the survey provide annual HIPAA refresher training, the lack of workforce testing (see previous question) implies that many organizations are “going through the motions” of implementing best practices without sufficient thought with regards to the purpose of HIPAA training.
How is HIPAA Training Delivered?
- 42.5% of respondents said HIPAA training is delivered both online and in-person
- 52.9% of respondents rely on online channels only to deliver HIPAA training.
- 4.6% of respondents deliver HIPAA training in-person.
Observation: There are no right or wrong ways to deliver HIPAA training, and each organization should determine which channels of delivery are most suitable for members of the workforce to understand, absorb, and apply the content of HIPAA training.
Workforce Certification of Training
- 58.7 % of respondents test workforce members during HIPAA training and certify the results of the test.
Best Practice: Although the certification of workforce training is not currently required, it is considered by many to be a best practice because the certification is proof that training has been provided, that the training was relevant to workforce members’ roles, and that workforce members obtained the required level of HIPAA knowledge to pass the test.
Maintenance of HIPAA Training Completion Records
- 96.6% of respondents maintain HIPAA training completion records
Discussion: Whether or not there is a requirement to maintain HIPAA training records depends on how the documentation standard of the HIPAA Security Rule is interpreted. The standard states HIPAA covered entities and business associates must maintain records of any activity, action, or assessment that is required by the Security Rule to be documented.
Although there is no requirement for the completion of HIPAA training to be documented in the Security Rule training standard, the Security Management Process standard (§164.308(a)) requires covered entities to “Implement policies and procedures to prevent, detect, contain, and correct security violations”.
The documentation of these policies and procedures is required by the HIPAA Security Rule and, as it could be assumed that some of the policies and procedures implemented to comply with this standard would be covered in HIPAA training, it could also be assumed that the provision and completion of HIPAA training should also be documented.
In addition, maintaining HIPAA training completion records is advisable to demonstrate HIPAA compliance in the event of an OCR audit or investigation. The records can also help guide the content of future HIPAA training, be a source of reference to determine which workforce members require further training (i.e., to qualify for a promotion), or be used to resolve accountability disputes when enforcing workforce sanctions for violations of HIPAA.
Availability of HIPAA Training Materials
- 94.3% of respondents make HIPAA training materials available to workforce members at all times.
Best Practice: Workforce members that work in healthcare organizations are required to be compliant with multiple regulations and standards. Making all training materials available to workforce members at all times can help support all regulatory compliance requirements.
Frequency of Phishing and Cybersecurity Awareness Training
- 29.9% of respondents provide phishing and cybersecurity awareness training at least monthly.
- 17.2% of respondents provide phishing and cybersecurity awareness training quarterly.
- 32.2% of respondents provide phishing and cybersecurity awareness training annually.
- 16.1% of respondents did not know the frequency of phishing and cybersecurity awareness training.
- 4.6% of respondents do not provide phishing and cybersecurity awareness training.
Comment: Although the HIPAA Security Rule does not stipulate the frequency of phishing and cybersecurity awareness training, the security training standard requires HIPAA covered entities and business associates to implement a “security awareness and training program for all members of the workforce”.
Not only does the inclusion of the word “program” imply that security awareness and training should be ongoing (i.e., more frequently than once a year), but the standard also applies to all members of the workforce. It would appear that not all members of the workforce are receiving security and awareness training based on the 16.1% of respondents who did not know the frequency of training.
Insights Into Communications of Electronic PHI
Organizations with written policies for communicating electronic PHI
- 86.2% of respondents said that their organizations maintained written policies for communicating electronic PHI.
Compliance: §164.316 of the HIPAA Security Rule requires HIPAA covered entities and business associates to maintain written records for most actions, activities, or assessments covered by the HIPAA Security Rule. Policies for communicating PHI electronically would be subject to this standard. Therefore, 13.8% of respondents are either violating HIPAA or not communicating PHI electronically.
Workforce Use of Personal Devices for Communicating PHI
- 77.1% of respondents prohibit workforce members from using personal devices to communicate PHI.
Observation: It is not possible to discern compliance best practices from the responses to this question because it may be the case some workforce members work remotely and communicate PHI from devices configured to support HIPAA compliance (i.e., secure video conferencing software, secure messaging apps, etc.).
Workforce Use of Corporate Mobile Devices for Communicating PHI
- 80.5% of respondents issue corporate mobile devices that are HIPAA compliant and secured with encryption.
Comment: Because there was no “does not apply” option, it may be the case that respondents who answered “no” to this question do not issue corporate mobile devices.
Emails Systems and HIPAA Compliance
- 83.9% of respondents said their organization used a HIPAA compliant email system for emailing PHI
Best Practice: Even if an organization does not ordinarily email PHI, it is advisable to implement a HIPAA compliant email system to cover events such as patients exercising their HIPAA rights to receive PHI via email and incoming communications in which PHI is disclosed by a patient.
Workforce Training on Using Email in Compliance with HIPAA
- 82.8% of respondents said their organization provided training on secure email usage under HIPAA rules.
Significance. It is significant that more organizations provide training on secure email usage (82.8%) than conduct phishing simulations (71.1%) because although 8% of all notifiable data breaches are attributable to misdirected emails, a much larger of notifiable data breaches are attributable to events that start with a workforce member interacting with a phishing email. The discrepancy between the two sets of responses further strengthens the impression that some organizations may be over-reliant on technical safeguards and underestimate the “human element” in security incidents.
Secure Messaging Usage
- 58.6% of respondents said workforce members use approved secure messaging platforms to text PHI.
Comment: Because there was no “does not apply” option, it may be the case that respondents who answered “no” to this question do not use secure messaging platforms.
Phone Call Privacy when Disclosing PHI
- 79.4% of respondents said that phone calls involving PHI are conducted in private settings to prevent unauthorized disclosures.
Best Practice: It is always a best practice to conduct phone calls in which PHI may be disclosed in private whenever possible to mitigate the risk of an unauthorized third party overhearing the conversation.
HIPAA Compliant Video Conferencing Tools
- 80.5% of respondents said their organizations used HIPAA compliant video conferencing tools when communicating PHI.
Implication: Although there may be some “no” responses to this question because it does not apply to all organizations, there is likely a large number of organizations that are communicating PHI unsecurely via video conferencing tools that do not support HIPAA compliance (i.e., WhatsApp, Discord, Slack, etc).
It is important to remember HIPAA compliant video conferencing tools have to be used for internal video calls as well as provider-to-patient video calls. The failure to use HIPAA compliant tools can result in PHI being transmitted via unsecured services and subject to man-in-the-middle interception. .
Fax Machine Usage
- 75.9% of respondents said their organizations communicated PHI via fax machines.
Observation: PHI communicated via a fax machine does not necessarily qualify as a transmission of electronic PHI if the information being transmitted did not exist in electronic form immediately before the fax transmission. In this case, it would not be necessary to use a HIPAA compliant fax service.
However, if PHI did exist in electronic form before being transmitted (including when printed onto paper from an EHR and then faxed) the transmission is subject to the safeguards of the HIPAA Security Rule. In this case, safeguards such as access controls, encrypted, audit trails, and secure cover sheets would have to be implemented.
Workplace Culture Encouraging HIPAA Compliance
- 90.9% of respondents believe their workplace culture encourages HIPAA compliance.
- 9.1% feel their workplace culture does not support HIPAA compliance.
Detailed Analysis:
A workplace culture that emphasizes HIPAA compliance is essential for creating an environment where employees are vigilant about safeguarding Protected Health Information (PHI). The overwhelmingly positive response indicates that most organizations successfully embed compliance as a core value, fostering employee engagement and adherence to procedures.
However, the 9.1% of respondents who feel unsupported by workplace culture represent a potential weak link in compliance efforts. In these organizations, a lack of emphasis on HIPAA compliance may result in inconsistent application of policies, inadequate training, or increased vulnerability to violations. Leadership in these settings should assess whether sufficient training, communication, and organizational buy-in are in place to reinforce a compliance-focused culture.
Management Support in Following HIPAA Procedures
- 82.8% of respondents feel adequately supported by management in following HIPAA procedures.
- 17.2% do not feel adequately supported.
Detailed Analysis:
Management support is crucial for empowering employees to follow HIPAA procedures effectively. Support can manifest as accessible resources, ongoing training, clear communication about expectations, and leadership accountability for compliance outcomes.
The 82.8% positive response indicates that most organizations are successfully providing the tools and backing needed for compliance. However, the 17.2% of respondents who lack management support may face compliance challenges such as:
- Insufficient training or resources.
- Ambiguity in compliance expectations.
- A perception that leadership does not prioritize compliance.
Organizations with lower management support may see reduced employee confidence in handling PHI, increased likelihood of procedural errors, and diminished effectiveness in responding to incidents. Addressing these gaps requires leadership to actively champion compliance initiatives and foster open communication channels to resolve barriers faced by staff.
Rating of Organizational Commitment to Enforcing HIPAA Policies
- 34.5% rated their organization’s commitment as excellent.
- 46.0% rated it as good.
- 14.9% rated it as fair.
- 4.6% rated it as poor.
Detailed Analysis:
The data reveals a generally positive perception of organizational commitment, with 80.5% of respondents rating their organization’s commitment to HIPAA compliance as either excellent or good. These organizations likely have robust enforcement mechanisms, regular audits, and a proactive approach to addressing compliance challenges.
However, the 14.9% fair and 4.6% poor ratings indicate areas for improvement in a significant minority of organizations. Potential issues in these organizations may include:
- Inconsistent enforcement of policies.
- Infrequent audits or lack of monitoring mechanisms.
- Insufficient training or communication about HIPAA standards.
- Leadership gaps in holding employees accountable for compliance violations.
Key Insights:
Organizations with fair or poor ratings should evaluate their compliance frameworks to identify shortcomings. This includes assessing enforcement consistency, providing refresher training for employees, and ensuring leadership prioritizes compliance across all levels of the organization. Clear disciplinary measures for non-compliance, coupled with incentives for adherence, can reinforce a stronger commitment.



