INTERPOL Issues Warning Over Increase in Ransomware Attacks on Healthcare Organizations
INTERPOL has issued an alert to hospitals over continuing ransomware attacks during the 2019 Novel Coronavirus pandemic. While some ransomware gangs have publicly stated they will be stopping attacks on healthcare providers that are on the front line dealing with COVID-19, many are still conducting attacks. Further, those attacks have increased.
Attempted Ransomware Attacks on Healthcare Organizations Increased over the Weekend
Last weekend, INTERPOL’s Cybercrime Threat Response (CTR) team detected a significant increase in attempted ransomware attacks on hospitals and other organizations and infrastructure involved in the response to the coronavirus pandemic and issued a ‘Purple Notice’ alerting police forces in all 194 member countries of the increased risk of attacks.
“As hospitals and medical organizations around the world are working non-stop to preserve the well-being of individuals stricken with the coronavirus, they have become targets for ruthless cybercriminals who are looking to make a profit at the expense of sick patients,” said INTERPOL Secretary General Jürgen Stock. INTERPOL also explained that ransomware attacks would cause a delay in providing essential care to COVID-19 patients and could also directly lead to deaths.
The medical research firm, Hammersmith Medicines Research in the United Kingdom, is one of the firms that was recently attacked. The company, which is poised to assist with the development of a vaccine for SARS-CoV-2, was attacked by the Maze ransomware gang, which published sensitive data stolen in the attack when the ransom was not paid. The Maze gang issued a press release explaining that all attacks on healthcare organization would be halted during the COVID-19 crisis and the data stolen in the attack was removed from the Maze website. However, other threat groups remain highly active and are still targeting healthcare organizations.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
A recent attack was reported by the Pleasanton, CA-based biotechnology firm 10x Genomics. The Sodinokibi (REvil) ransomware gang claimed to have downloaded 1TB of data from the firm before deploying their ransomware payload. A sample of that data was published online in an attempt to pressure the firm into paying the ransom.
In a recent SEC filing, the company explained that it is working with law enforcement and has engaged a third-party firm to assist with the investigation. 10x Genomics reports that it was able to restore normal business operations quickly, without the attack impacting daily operations. “It is particularly disappointing that we would be attacked at a time when our products are being used widely by researchers around the world to understand and fight COVID-19,” said a 10x Genomics spokesperson.
Assistance Being Offered to Healthcare Organizations
INTERPOL’s CTR team is working with hospitals and other healthcare providers that have been targeted with ransomware to help them defend against attacks and recover when attacks succeed.
INTERPOL warns that ransomware is primarily being spread via malicious code in email attachments which triggers a ransomware download when opened. Hyperlinks are also commonly used to direct users to malicious websites where ransomware is downloaded.
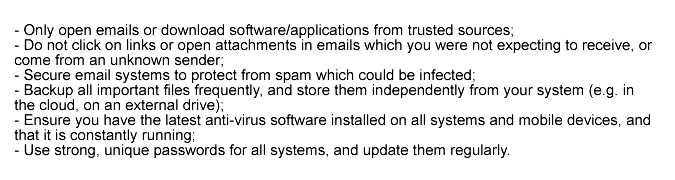
INTERPOL advises healthcare organizations to take the following steps to protect their systems from attack and ensure a fast recovery is possible in the event of an attack succeeding:
Attacks are also taking place through the exploitation of vulnerabilities in RDP and VPN systems, so it is essential for all software to be kept up to date and for patches to be applied promptly. The Sodinokibi threat group has been exploiting vulnerabilities in VPNs in attacks on healthcare organizations. In a blog post last week, Microsoft stated it has been helping hospitals secure their systems by alerting them to unpatched vulnerabilities in their VPN devices. Microsoft has also suggested best practices for securing systems to prevent attacks.