January 2024 Healthcare Data Breach Report
In January, 61 data breaches of 500 or more records were reported to the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR), which is a 22% month-over-month reduction in reported data breaches, with data breaches falling to two below the monthly average of 63 data breaches a month. While the reduction in data breaches is good news, January is typically a relatively quiet month for healthcare data breaches, and January’s figures are 45% higher than January 2023.
For the second consecutive month, there was a fall in the number of breached records with 8,800,875 healthcare records breached in January. As with the number of reported breaches, the reduction is good news but the number of breached records is much higher than in previous years.
Further, in January 2024, 4 cyberattacks were reported to OCR where the total number of records involved has yet to be determined. To meet the reporting requirements of the HIPAA Breach Notification Rule – which requires data breaches to be reported within 60 days of discovery – those four data breaches were reported using a placeholder of 500 or 501 records. January’s total will therefore be considerably higher.
Biggest Healthcare Data Breaches in January 2024
24 data breaches of 10,000 or more healthcare records were reported to OCR in January, including one breach of half a million records, one of more than 2 million records, and a breach that exposed the records of almost 4 million individuals. Two of those data breaches occurred at the transcription service provider, Perry Johnson & Associates, Inc. (PJ&A), but were reported by the affected covered entity. In November 2023, PJ&A reported a cyberattack to OCR that affected 8.95 million individuals. The totals from Concentra Health Services and North Kansas City Hospital take the total number of individuals affected by the PJ&A data breach past 13.45 million.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
The second largest data breach of the month was a ransomware attack on Integris Health that saw the data of 2,385,646 individuals compromised. Integris Health was able to recover files from backups and chose not to pay the ransom to prevent the publication of the stolen data. When it became clear that the ransom would not be paid, the threat actor tried to extort patients, contacting them directly and threatening them with the publication of data if they did not pay $50. This was not the first time that a ransomware attacker has gone after patients, and it is unlikely to be the last. With fewer victims of ransomware attacks paying ransoms, these aggressive tactics are likely to increase.
OCR investigates all healthcare data breaches of 500 or more records to determine if they were the result of a failure to comply with the HIPAA Rules. OCR has also indicated that it will be restarting its HIPAA audit program to assess compliance with the HIPAA Rules across the healthcare industry. When the HIPAA audits were last conducted in 2017, they revealed the majority of HIPAA-regulated entities were not fully compliant with the HIPAA Security Rule.
A report from IBM in February suggests little has changed and healthcare organizations are failing to implement basic security measures. The study found that 85% of cyberattacks in critical infrastructure sectors could have been prevented with “basic security measures,” such as prompt patching, multi-factor authentication, and implementing the principle of least privilege. This is an area that OCR is attempting to address with its voluntary cybersecurity performance goals, and potentially, with the HIPAA Security Rule update OCR is due to propose this spring.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Breach |
| Concentra Health Services, Inc. | TX | Healthcare Provider | 3,998,162 | Cyberattack on business associate (PJ&A) |
| INTEGRIS Health | OK | Healthcare Provider | 2,385,646 | Ransomware attack (Data theft confirmed) |
| North Kansas City Hospital | MO | Healthcare Provider | 502,438 | Cyberattack on business associate (PJ&A) |
| Azura Vascular Care | PA | Business Associate | 348,000 | Hacking incident |
| Des Moines Orthopaedic Surgeons, P.C. | IA | Healthcare Provider | 307,864 | Hacking incident (Data theft confirmed) |
| The Harris Center for Mental Health and IDD | TX | Healthcare Provider | 238,463 | Ransomware attack (Data theft confirmed) |
| HORNE, LLP | MS | Business Associate | 170,052 | Hacking incident |
| Columbus Regional Healthcare System | NC | Healthcare Provider | 132,887 | Hacking incident (Data theft confirmed) |
| Cooper Clinic, P.A. | TX | Healthcare Provider | 124,341 | Hacking incident |
| Psychological Holdings, PLLC d/b/a Senior PsychCare | TX | Healthcare Provider | 75,349 | Hacking incident |
| CNO ACE | IN | Health Plan | 65,295 | Hacking incident |
| ConsensioHealth, LLC | WI | Business Associate | 60,871 | Ransomware attack (Data theft confirmed) |
| Veterans Health Administration | DC | Healthcare Provider | 46,677 | No public report about the breach – Unauthorized access/disclosure of paper/films |
| Hampton-Newport News Community Services Board | VA | Healthcare Provider | 44,312 | Ransomware attack (Data theft confirmed) |
| United Regional Health Care System | TX | Healthcare Provider | 36,900 | Hacking incident at a business associate |
| Air Methods, LLC | NV | Healthcare Provider | 34,016 | Theft of an unencrypted laptop computer |
| Coastal Hospice & Palliative Care | MD | Healthcare Provider | 29,100 | Hacking incident |
| AHS Management Company, Inc. | TN | Business Associate | 23,686 | Ransomware attack (Data theft confirmed) |
| Burr & Forman LLP | AL | Business Associate | 19,893 | Hacking incident |
| Insurance ACE/Humana Inc. | KY | Health Plan | 12,539 | Mailing error resulted in documents being sent to incorrect recipients |
| InHealth Technologies | CA | Healthcare Provider | 12,143 | Hacking incident |
| TGI Direct | MI | Business Associate | 11,556 | Hacking incident |
| Fincantieri Marine Group, LLC | DC | Health Plan | 11,535 | Ransomware attack (Data theft confirmed) |
| Midwest Long Term Care Services d/b/a Senior Scripts | MO | Healthcare Provider | 10,566 | Hacking incident |
Data Breach Causes and Locations
Hacking/IT incidents dominate the breach reports and account for 21 of the 24 data breaches of 10,000 or more records. 47 of the month’s 61 data breaches were reported as hacking/IT incidents which is 77% of the month’s data breaches. Across those data breaches, the records of 8,687,590 individuals were exposed or impermissibly disclosed, which is 98.7% of the month’s breached records. The average size of a hacking-related data breach in January was 184,842 records and the median breach size was 6,457 records.
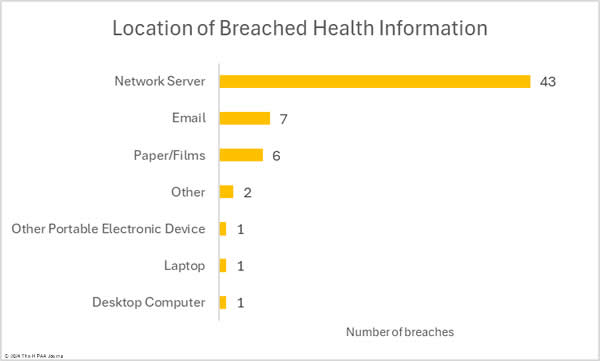
There were 12 reported unauthorized access/disclosure incidents involving a total of 78,162 records. The average breach size was 6,514 records and the median breach size was 1,069 records. There were two loss/theft incidents reported, both of which involved the loss or theft of unencrypted electronic devices. Those devices contained the records of 35,123 individuals. The most common location of breached healthcare data in January was network servers. Email accounts were involved in 7 data breaches and there were 6 data breaches involving physical records.
There has been some good news on the ransomware front. In February, the notorious and prolific LockBit ransomware-as-a-service group had its infrastructure taken down after a months-long international law enforcement operation. LockBit has been the most active ransomware group for a large proportion of the 4 years it has been active and the group has conducted many attacks on the healthcare sector.
34 servers were taken down, along with the affiliate portal, data leak site, and Tor sites. The group has exploited vulnerabilities in the past to gain access to victims’ networks, and it was an unpatched vulnerability that allowed law enforcement to gain access to its infrastructure. More than 2,000 decryption keys were obtained and 200 cryptocurrency wallets were seized. The core members of the group remain at large and may rebuild their infrastructure and relaunch under a different name, but the operation has caused severe disruption and has damaged the group’s reputation within the hacking community.
Where did the Data Breaches Occur?
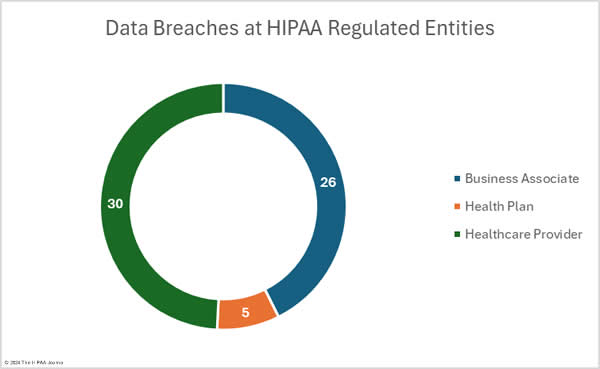
The raw data on the OCR data breach portal shows there were 38 data breaches at healthcare providers (8,030,189 records), 12 data breaches at health plans (122,803 records), 9 data breaches at business associates (644,716 records), and two data breaches at healthcare clearinghouses (3,167 records). These figures do not tell the whole story; however, as the entity reporting a data breach is not always the entity that suffered the data breach. When a data breach occurs at a business associate, it may be reported by the business associate, the affected covered entities, or a combination of the two, as was the case with the PJ&A data breach. Looking a little deeper into the data shows where the data breaches occurred. The pie charts below take this into account and show where the data breaches occurred rather than the entities affected by the data breaches.
Geographical Distribution of Healthcare Data Breaches
Data breaches of 500 or more records were reported by HIPAA-regulated entities in 31 U.S. states and Washington D.C. in January. California was the worst affected state with 9 reported breaches, followed by Texas with 6 breaches.
| State | Number of data breaches |
| California | 9 |
| Texas | 6 |
| Alabama, Tennessee, & the District of Columbia | 3 |
| Arkansas, Florida, Indiana, Iowa, Michigan, Missouri, Nevada, North Dakota, Pennsylvania & Virginia | 2 |
| Arizona, Colorado, Kansas, Kentucky, Maryland, Massachusetts, Mississippi, Nebraska, New Hampshire, New Mexico, New York, North Carolina, Ohio, Oklahoma, Oregon, Washington & Wisconsin | 1 |
HIPAA Enforcement Activity in January 2024
No HIPAA compliance enforcement actions were announced by OCR in January, but State Attorneys General took action over HIPAA violations. Refuah Health Center Inc. agreed to settle alleged violations of the HIPAA Security and Breach Notification Rules and New York General Business Law. The investigation identified risk assessment and risk management failures, a lack of reviews of records of system activity, and other security failures. Refuah Health Center paid a $450,000 penalty and agreed to invest $1.2 million in cybersecurity.
The California Attorney General announced that a settlement had been reached with Quest Diagnostics to resolve alleged violations of state laws, including allegations that Quest Diagnostics improperly disposed of the personal information of patients. A series of inspections of Quest Diagnostics laboratories and patient service centers uncovered widespread unlawful disposal of medical and hazardous waste and the unredacted personal health information of patients. Quest Diagnostics agreed to address the issues discovered during the investigation and paid a $5 million financial penalty.