June 2024 Healthcare Data Breach Report
In June 2024, 47 data breaches of 500 or more healthcare records were reported to the HHS’ Office for Civil Rights (OCR), the fewest number of breaches since October 2023. Data breaches were down 9.6% from May 2024, and 30.9% down from June 2023, and were well below the 12-month average of 64 data breaches a month.
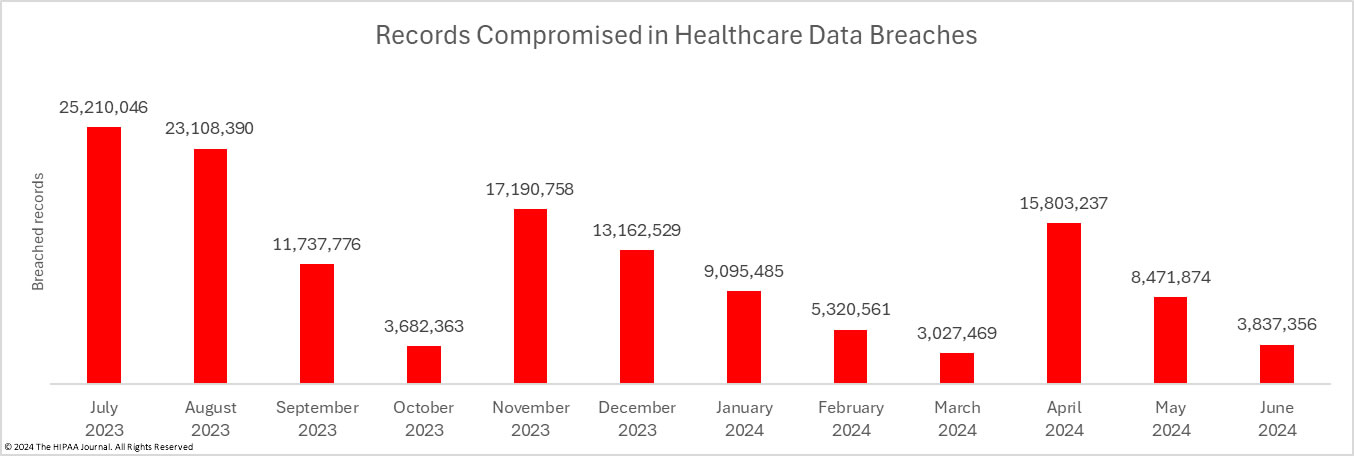
For the second consecutive month, the number of breached records has fallen. Across the 47 breaches reported in June, the protected health information of 3,837,356 individuals was exposed, stolen, or impermissibly disclosed.
June’s compromised record total is the second lowest monthly total in 2024, 54.7% lower than May 2024, and well below the 12-month average of 11,637,320 breached records a month. It is likely to be a very different story next month, as Change Healthcare will be mailing breach notification letters to the individuals affected by its February 2024 ransomware attack from July 20, 2024, which means OCR will soon be notified about the extent of the breach. The CEO of Change Healthcare’s parent company, UnitedHealth Group, told a senate hearing that the breach is likely to affect as many as 1 in 3 Americans – up to 113,000,000 individuals.
Largest Healthcare Data Breaches in June 2024
The largest data breach of the month was reported by the Pennsylvania health system Geisinger and involved the protected health information of 1,276,026 individuals. Unusually, for such a large data breach, it was not a hacking incident or ransomware attack. Geisinger discovered that a former employee of a business associate had accessed patient records after being terminated. The business associate failed to terminate the employee’s access rights before terminating the employee.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Lurie Children’s Hospital reported the biggest hacking incident of the month – a ransomware attack involving the theft of the protected health information of 775,860 current and former patients. The attack caused considerable disruption and resulted in the electronic health record (EHR) system being offline for months. The attack occurred in January, but the hospital was not able to restore the EHR until May. Lurie Children’s refused to pay the ransom as there was no guarantee that the data would be returned. The threat group behind the attack claimed to have sold the stolen data.
The Minnesota radiology services company, Consulting Radiologists, also reported a major breach involving the protected health information of 583,824 patients. Few details have been disclosed about the attack, other than it being a hacking incident with possible data theft. Two eye care providers reported ransomware attacks that each affected more than 300,000 patients. Panorama Eyecare’s incident occurred a year previously, with the LockBit ransomware group stealing patient data in May 2023, and Texas Retina Associate’s attack was detected in March 2024; however, the Monto ransomware group had access to its network since October 2023.
Financial Business and Consumer Solutions suffered a breach that was reported to OCR as involving the protected health information of 117,567 individuals. The breach also affected some clients that were not HIPAA-covered entities, as the breach was initially reported to the Maine Attorney General as involving the personal information of 1,955,385 individuals. As the investigation progressed it became clear that the breach was far worse. The Maine Attorney General has now been informed that the breach has affected 4,050,711 individuals. It is currently unclear if any of the additional 2,095,326 individuals were patients of its HIPAA-covered entity clients.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Type of Breach |
| Geisinger | PA | Healthcare Provider | 1,276,026 | Former employee of a business associate accessed patient data after being terminated |
| Ann & Robert H. Lurie Children’s Hospital of Chicago | IL | Healthcare Provider | 775,860 | Ransomware attack with data theft – ransom not paid |
| Consulting Radiologists LTD. | MN | Healthcare Provider | 583,824 | Hacking incident with potential data theft |
| Panorama Eyecare | CO | Healthcare Provider | 377,911 | Ransomware attack with potential data theft |
| Texas Retina Associates | TX | Healthcare Provider | 312,867 | Ransomware attack with potential data theft |
| Financial Business and Consumer Solutions, Inc. | PA | Business Associate | 117,567* | Hacking incident with potential data theft |
| Signature Performance, Inc. | NE | Business Associate | 106,540 | Hacking incident with potential data theft. Also involved the data of 70,000 Adventist Health Tulare patients |
| County of Los Angeles Department of Health Services | CA | Healthcare Provider | 41,444 | Phishing attack involving 53 compromised email accounts |
| Radiology and Imaging Specialists | FL | Healthcare Provider | 37,210 | No information is available other than a hacking/IT incident involving email |
| The Mount Kisco Surgery Center LLC d/b/a The Ambulatory Surgery Center of Westchester | NY | Healthcare Provider | 22,139 | Compromised employee email account |
| Aptihealth, Inc. | NY | Healthcare Provider | 19,805 | Hacking incident at a business associate (Sisense) with potential data theft |
| Wisconsin Department of Health Services | WI | Healthcare Provider | 19,150 | Accidental disclosure of patient data via email by a business associate |
| Neurobehavioral Medicine Consultants, P.C. | OH | Healthcare Provider | 18,182 | Hacking incident with potential data theft |
| The Lash Group, LLC | PA | Business Associate | 15,196 | Hacking incident with potential data theft affecting Cencora and The Lash Group. The breach was reported to OCR separately by AmerisourceBergen Specialty Group as affecting a total of 255,316 individuals |
| Insurance ACE/Humana Inc. | KY | Health Plan | 15,003 | Unauthorized disclosure of paper records |
| Kairos Health Arizona, Inc. | AZ | Business Associate | 14,364 | Unauthorized access to patient data by a former business associate |
| SkinCure Oncology | IL | Business Associate | 13,434 | Multiple email accounts accessed by an unauthorized individual |
| Memorial Sloan Kettering Cancer Center | NY | Healthcare Provider | 12,274 | Multiple email accounts compromised in a phishing attack |
Data Breach Causes and Location of Compromised PHI
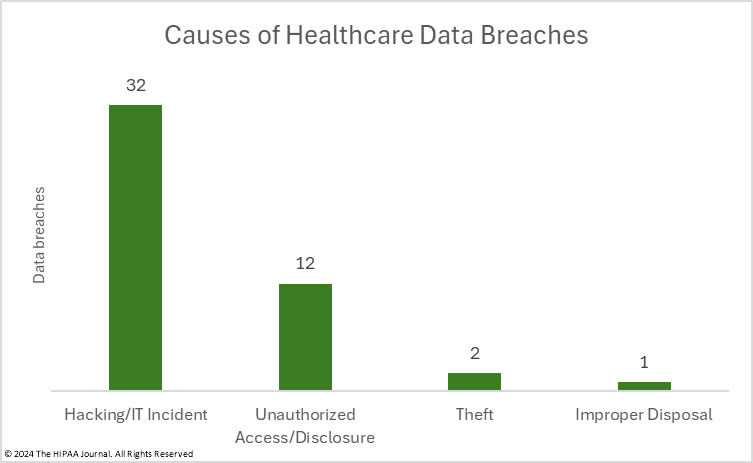
There was an 18% month-over-month fall in the number of reported hacking incidents, although even with the reduction, hacking incidents continue to outnumber all other data breach causes. Hacking accounted for 68% of the reported large data breaches in June and 65.5% of the month’s breached records. In total, 2,512,792 records were compromised in hacking and other IT incidents. On average, hacking incidents involved the protected health information of 45,562 individuals with a median data breach size of 6,419 records.
12 unauthorized access/disclosure incidents were reported in June, one more than in May; however, there was a 2,138% month-over-month increase in the number of records exposed in these incidents due to a massive insider breach at a business associate of Geisinger. Across the 12 incidents, the records of 1,319,305 individuals were impermissibly accessed or disclosed. The average breach size was 109,942 records and the median breach size was 1,648 records. Two theft incidents were reported that involved the protected health information of 4,018 individuals, one involving a stolen laptop and the other stolen paper records, and there was 1 improper disposal incident involving the protected health information of 1,241 individuals.
The most common location of breached protected health information was network servers. HIPAA Security Rule compliance can make it much harder for hackers to breach networks; however, many breaches occur at HIPAA-regulated entities that have implemented robust cybersecurity defenses. This week, healthcare CISSP, Josh Ablett, shared his views with readers of the HIPAA Journal about the importance of conducting cyber fire drills and how they can reduce the stress on staff following a successful cyberattack and shorten the recovery time. Email was the next most common location of breached protected health information. Email-related breaches are among the easiest to prevent. This month we have highlighted some of the most common ways that email is involved in HIPAA violations.
Where did the Data Breaches Occur?
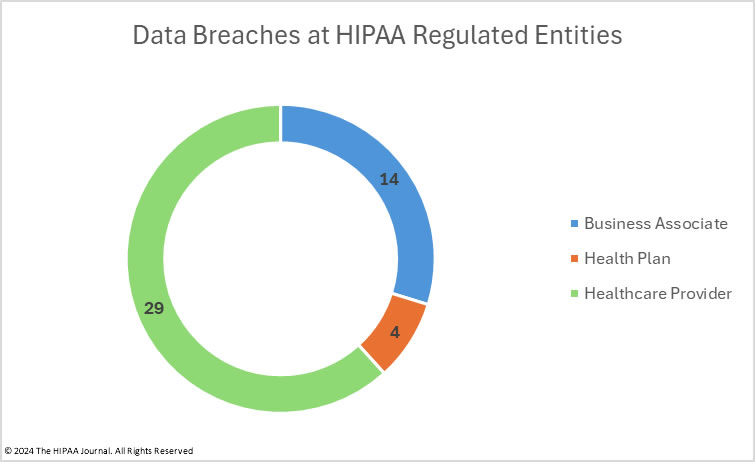
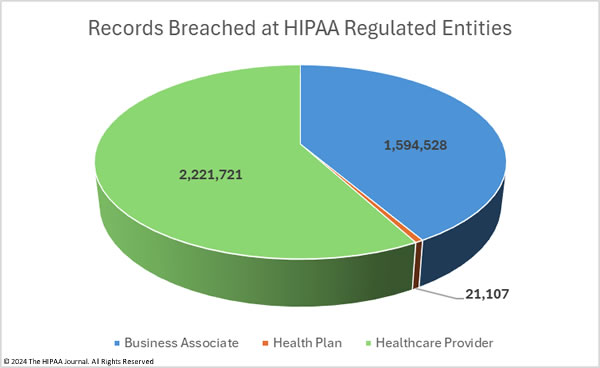
The OCR breach portal lists data breaches by the reporting entity. In June 2024, 34 breaches were reported by healthcare providers involving 3,538,078 records. The mean breach size was 104,061 records and the median breach size was 3,029 records. 7 breaches were reported by health plans involving 25,905 records, with a mean breach size of 3,701 records and a median breach size of 1,867 records. Business associates reported 6 breaches involving 273,373 healthcare records, with a mean breach size of 45,562 records and a median breach size of 14,780 records.
Under HIPAA, it is ultimately the responsibility of each covered entity to ensure that data breaches are reported to OCR and individual notifications are sent, so some HIPAA-covered entities report breaches when they actually occurred at one of their business associates. Each month, the HIPAA Journal determines where the breach occurred to better reflect the number of data breaches occurring at business associates. The adjusted data has been used for the pie charts below.
Geographical Distribution of Healthcare Data Breaches
HIPAA-regulated entities in 24 states reported breaches of 500 or more healthcare records in June 2024, with New York and Pennsylvania the worst affected states with five reported data breaches in each state; however, there was a considerable difference in the number of compromised records. In New York, 59,945 records were breached across those 5 incidents whereas the Pennsylvania data breaches affected 1,416,019 individuals.
Illinois was also badly affected, and while only experiencing 2 daya branches, the records of 789,294 individuals were compromised. There was only one reported breach in Minnesota, Colorado, and Texas, but they were all major incidents, affecting 583,824 individuals, 377,911 individuals, and 312,867 individuals respectively.
| State | Breaches |
| New York & Pennsylvania | 5 |
| Massachusetts & Ohio | 4 |
| Georgia | 3 |
| California, Connecticut, Florida, Illinois, Michigan, Nebraska & Oregon | 2 |
| Alabama, Arizona, Arkansas, Colorado, Iowa, Kansas, Kentucky, Maine, Minnesota, New Mexico, Texas & Wisconsin | 1 |
HIPAA Enforcement Activity in June 2024
OCR did not announce any HIPAA enforcement actions in June; however, the California Attorney General agreed to settle potential violations of HIPAA and state laws with two HIPAA-regulated entities, Blackbaud and Adventist Health Hanford.
California Attorney General Rob Bonta announced that a $6.75 million settlement had been agreed with the South Carolina-based data management software provider Blackbaud, to resolve violations of HIPAA and California’s consumer privacy and data protection laws. Blackbaud was investigated over a cyberattack that was disclosed in May 2020. Hackers had access to its systems for 3 months before the breach was detected.
The investigation confirmed that Blackbaud had not implemented appropriate security measures and did not follow standard security practices. Blackbaud stored large amounts of sensitive data, retaining sensitive data when there was no longer any legitimate business purpose for retention, was not properly monitoring for suspicious activity within its systems, was not keeping up to date on security standards, and had not implemented multifactor authentication. In addition to the financial penalty, Blackbaud is required to implement robust data security improvements to reduce the risk of further cyberattacks.
The California Attorney General also announced a settlement with Adventist Health Hanford to resolve alleged unauthorized disclosures of patient data to law enforcement without a warrant. The allegations relate to two patients who had stillbirths at the hospital, who had their medical information disclosed to law enforcement about their alleged drug use. Adventist Health maintained that there was no wrongdoing but agreed to settle with the state and pay a nominal financial penalty of $10,000.