New Report Provides Deep Dive into COVID-19 Themed Phishing Tactics
In early 2020, phishers started to take advantage of the pandemic and switched from their standard lures to a wide variety of pandemic-related themes for their campaigns. To coincide with the one-year anniversary of the pandemic, researchers at the Palo Alto Networks Unit 42 Team analyzed the phishing trends over the course of the past year to review the changes in the tactics, techniques, and procedures (TTPs) of phishers and the extent to which COVID-19 was used in their phishing campaigns.
The researchers analyzed all phishing URLs detected between January 2020 and February 2021 to determine how many had a COVID-19 theme, using specific keywords and phrases related to COVID-19 and other aspects of the pandemic. The researchers identified 69,950 unique phishing URLs related to COVID-19 topics, with almost half of those URLs directly related to COVID-19.
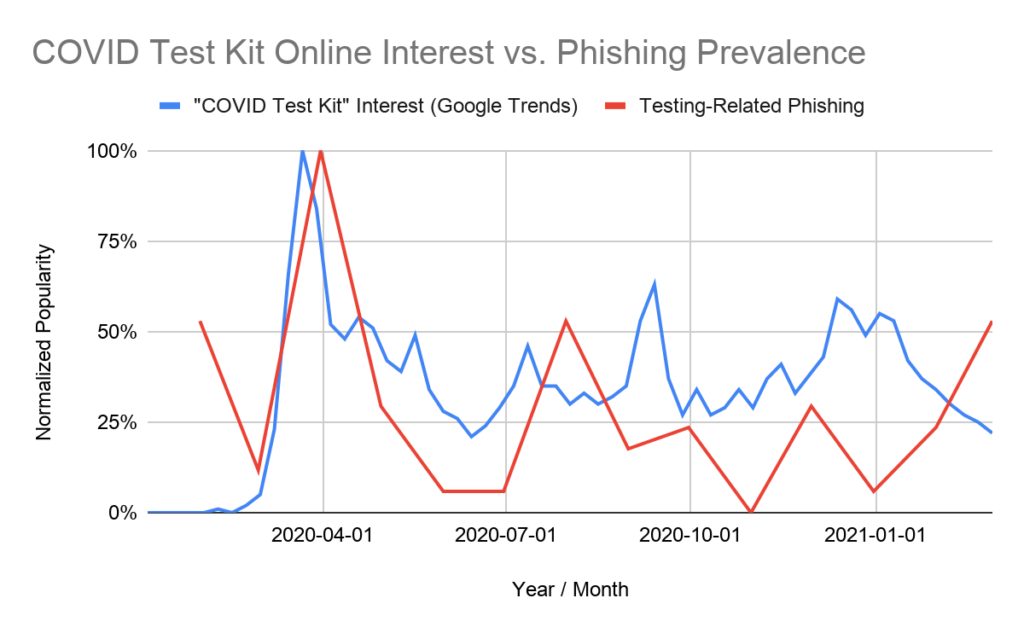
Phishing campaigns were promptly adapted to the latest news and thoughts on the coronavirus and closely mirrored the latest pandemic trends. Following the World Health Organization’s declaration of the pandemic in March 2020 there was a global shortage of personal protective equipment (PPE) and testing kits, and phishing campaigns were launched offering access to stocks. Government stimulus programs were then launched, and phishing campaigns were quickly adapted to include lures related to those programs. For instance, the volume of phishing emails related to COVID-19 online test kits closely followed the popularity of test kit-related searches on Google.
Throughout the pandemic, the websites of genuine vendors of COVID-19 test kits were targeted. Access to the sites was gained and phishing kits were uploaded to steal credentials. In December 2020, when the vaccine rollout started, campaigns switched to vaccine related lures using domains that spoofed vaccine developers such as Pfizer, BioNTech and others. The websites of pharmaceutical companies were targeted and had phishing content added related to vaccines. Between December 2020 and February 2021, vaccine-related phishing scams increased by 530%.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
One off the techniques employed by phishers to evade security solutions is to use a two-step process on their phishing websites that requires the visitor to first click to login before being presented with the phishing form – a tactic called client-side cloaking. Many anti-phishing solutions will visit the URL linked in an email to assess the content but will only check the landing page for phishing content. By using client-side cloaking the malicious content is less likely to be detected.
The report highlights the opportunistic nature of phishers. They will rapidly change their TTPs in response to new trends and use lures that are likely to get the best response, including changing targets. Between December 2020 and February 2021, phishing attacks targeting pharmacies and hospitals increased by 189% as phishers switched to targeting healthcare employees to steal their credentials.
Throughout the pandemic, Microsoft was the brand most targeted by attackers. More than 23% of COVID-19 phishing URLS targeted Microsoft credentials. Fake Microsoft login pages were set up to steal the Microsoft 365 credentials of employees at pharmaceutical firms and pharmacies. When Microsoft credentials are obtained, they can be used to access email accounts to send phishing emails from genuine pharmacy and pharma company domains, increasing the chance of those emails being delivered and acted upon by the recipients. Targeted companies include Walgreens in the US, Pharmascience in Canada, Glenmark Pharmaceuticals in India, and Junshi Biosciences in China.
Currently, large numbers of phishing emails are being sent related to vaccines and as more individuals try to get themselves and their family members registered for immunization, vaccine-related phishing scams are likely to continue.
“Individuals should continue to exercise caution when viewing any emails or websites claiming to sell any goods or services or provide any benefits related to COVID-19. If it seems too good to be true, it most likely is,” warned the Unit42 researchers. “Employees in the healthcare industry in particular should view links contained in any incoming emails with suspicion, especially from emails trying to convey a sense of urgency.”