November 2024 Healthcare Data Breach Report
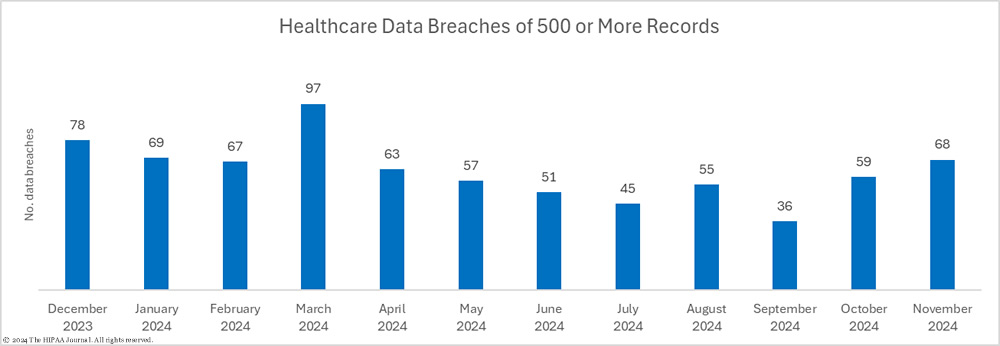
There has been a 15.3% month-over-month increase in healthcare data breaches, with 68 data breaches of 500 or more healthcare records reported to the U.S. Department of Health and Human Services’ Office for Civil Rights (OCR) in November.
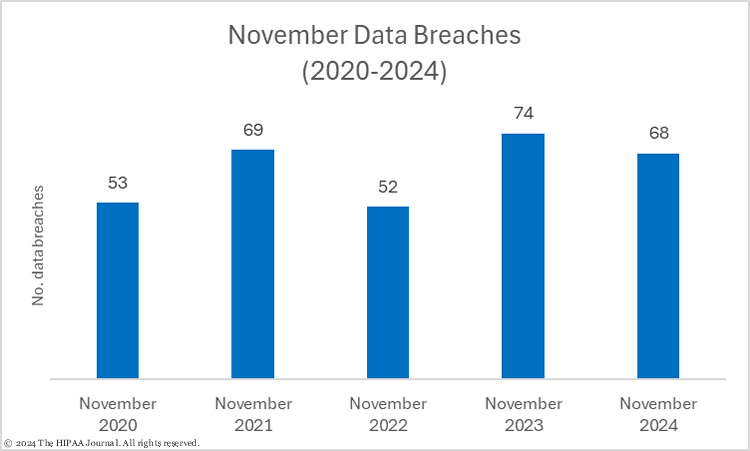
November was the worst month of H2 2024 in terms of reported data breaches, and the 4th worst month of the year; however, data breaches were down 8% from November 2024. November’s healthcare data breaches bring the 2024 total up to 667 data breaches, one short of the total for the year to November 30, 2023.
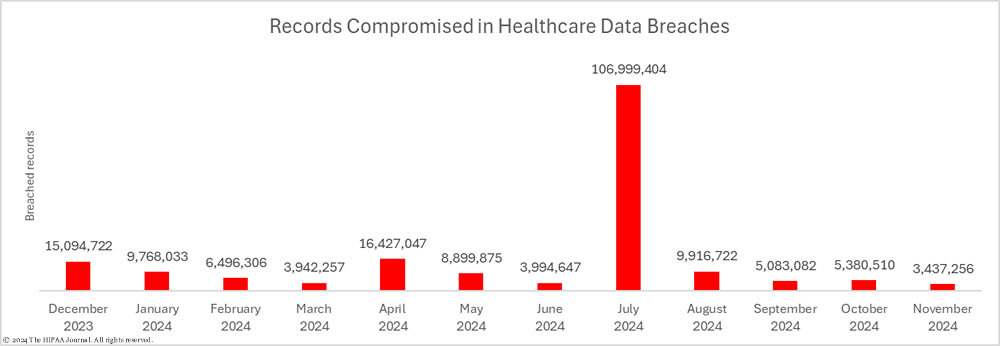
While there was an increase in data breaches there was a reduction in breached records, which were down 36.1% month-over-month to 3,437,256 breached records. In 2024, an average of 16,395,000 records were breached each month; however, that number is skewed by the massive data breach at Change Healthcare which affected an estimated 100 million individuals. The median number of breached records each month in 2024 is 6,496,306 records.
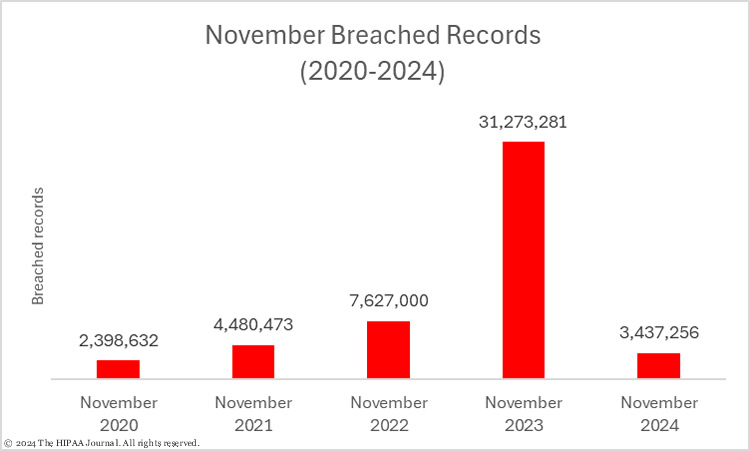
As the bar chart below shows, there was a massive decrease in breached records compared to the 31 million breached records reported in November 2023. November 2023’s total was exceptionally high due to the mass exploitation of a vulnerability in Progress Software’s MOVEit file transfer solution by the Clop group.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
With November’s breached records, the running total for 2024 is an astonishing 180,345,139 breached records. Even if no more data breaches are reported, 2024 will still be the worst-ever year for breached healthcare records, smashing the record set last year when an unprecedented 168 million healthcare records were breached.
Biggest Healthcare Data Breaches in November 2024
The three biggest healthcare data breaches in November were all due to cyberattacks by ransomware groups. Texas Tech University Health experienced a ransomware attack by the relatively new Interlock ransomware group. The protected health information of 1,465,000 patients was stolen in the attack and was leaked online when the ransom was not paid. The breach was reported separately by the two affected science centers.
Little information has been released at the time of publication of this report about the data breach at American Addiction Centers. There is currently no breach report on the American Addiction Centers website; however, the Rhysida ransomware group claimed responsibility for the attack and said 2.8 TB of data was exfiltrated, 90% of which has been uploaded to its data leak site.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Breach |
| Texas Tech University Health Sciences Center El Paso | TX | Healthcare Provider | 815,000 | Ransomware attack – Data theft confirmed (Interlock ransomware) |
| Texas Tech University Health Sciences Center | TX | Healthcare Provider | 650,000 | Ransomware attack – Data theft confirmed (Interlock ransomware) |
| American Addiction Centers, Inc. | TN | Business Associate | 410,747 | Ransomware attack (Rhysida ransomware) – No breach report published |
| Rocky Mountain Gastroenterology Associates PLLC | CO | Healthcare Provider | 366,491 | Hacking incident – Data theft confirmed |
| Thompson Coburn LLP | MO | Business Associate | 305,088 | Hacking incident involving Presbyterian Healthcare Services (NM) data |
| Great Plains Regional Medical Center | OK | Healthcare Provider | 133,149 | Ransomware attack – Data theft confirmed |
| Conceptions Reproductive Associates of Colorado | CO | Healthcare Provider | 80,000 | Ransomware attack (Inc ransomware) – No breach report published |
| ESHA, Inc. | TX | Business Associate | 76,922 | Hacking incident |
| MDLand International Corporation | NY | Business Associate | 63,052 | Hacking incident (EHR) – No breach report published |
| AuthoraCare Collective | NC | Healthcare Provider | 58,019 | Unauthorized Access/Disclosure (Network Server) – No information released |
| Radiologic Medical Services, P.C. | IA | Healthcare Provider | 56,902 | Compromised email accounts |
| Kaiser Foundation Hospitals | CA | Healthcare Provider | 44,600 | Compromised email accounts |
| Mid-Ohio Psychological Services Inc. | OH | Healthcare Provider | 40,345 | Ransomware attack (BlackSuit Ransomware) – No information released |
| Oklahoma Spine Hospital | OK | Healthcare Provider | 38,945 | Compromised email account |
| South West Family Medicine Associates, PA | TX | Healthcare Provider | 36,959 | Hacking incident |
| Colonial Behavioral Health | VA | Healthcare Provider | 29,930 | Ransomware attack (Qilin) |
| TriHealth H, LLC d/b/a TriHealth Physician Partners | OH | Healthcare Provider | 27,426 | Hacking incident at a business associate |
| Equinox, Inc. | NY | Healthcare Provider | 21,565 | Compromised email accounts |
| VPS of MI PLLC | MI | Healthcare Provider | 20,604 | Ransomware attack (Group unknown) |
| East Central Missouri Behavioral Health Services, Inc. | MO | Healthcare Provider | 20,000 | Hacking incident (Network Server) – No breach report published |
| Planned Parenthood of Montana | MT | Healthcare Provider | 18,003 | Ransomware attack (RansomHub) |
| Vann Virginia Center for Orthopaedics, PC dba Atlantic Orthopaedic Specialists | VA | Healthcare Provider | 15,264 | Compromised email account |
| Jefferson Dental Center, Inc. | IN | Healthcare Provider | 12,340 | Ransomware attack – Data theft confirmed (Ransomware group unknown) |
| Ardon Health, LLC | OR | Healthcare Provider | 10,098 | Hacking incident (Email) – No breach report published |
In November, there were 24 data breaches of 10,000 or more healthcare records, but that number could grow as there were also 10 breaches reported as affecting 500 or 501 individuals. These are commonly used placeholder figures when a data breach has been confirmed but the number of affected individuals has not yet been determined. These figures can change dramatically. The Change Healthcare data breach was initially reported as affecting 500 individuals only to be later updated to 100 million individuals, and the data breach at Ascension Health increased from 500 to 5.6 million several months later.
| Name of Covered Entity | State | Regulated Entity Type | Records | Cause of Breach |
| Lubbock County Hospital District | TX | Healthcare Provider | 501 | Ransomware attack (Brain Cipher) |
| York County | PA | Healthcare Provider | 501 | Compromised email account |
| Laboratory Services Cooperative | WA | Healthcare Provider | 501 | Hacking incident – No information released |
| Maternal Fetal Medicine Associates, PLLC, Carnegie Hill Imaging for Women, and Carnegie Women’s Health (collectively, “the Practices”) | NY | Healthcare Provider | 501 | Hacking incident – Data theft confirmed |
| Georgia Department of Public Health | GA | Healthcare Provider | 500 | Compromised email accounts |
| Western Montana Mental Health Center | MT | Healthcare Provider | 500 | Hacking incident – Investigation ongoing |
| Physicians’ Primary Care of Southwest Florida | FL | Healthcare Provider | 500 | Hacking incident – Investigation ongoing |
| Humboldt Independent Practice Association (Humboldt IPA) | CA | Healthcare Provider | 500 | Hacking incident – No information released |
| Orthopedics Rhode Island, Inc. | CT | Healthcare Provider | 500 | Hacking incident – Investigation ongoing |
| Brunswick Hospital Center | NY | Healthcare Provider | 500 | Hacking incident – Investigation ongoing |
Causes of November 2024 Healthcare Data Breaches
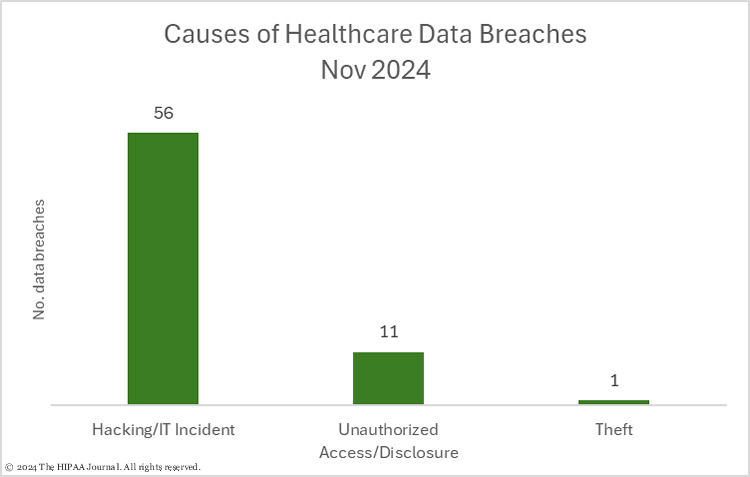
Hacking and other IT incident reports accounted for 82.4% of the month’s data breaches (56 incidents), with 16.2% of the data breaches due to unauthorized access/disclosure incidents (11 incidents), and 1.47% due to theft (1 incident). No loss or improper disposal incidents were reported in November. Hacking/IT incidents tend to involve far more records than other types of data breaches, and November was no different with 95.3% of the month’s records breached in these incidents (3,276,321 records). The average size of a hacking incident was 58,506 records and the median breach size was 2,999 records. Across the 11 unauthorized access/disclosure incidents, the records of 155,990 individuals were breached. The average breach size was 14,181 records and the median breach size was 2,945 records. The single theft incident involved the protected health information of 4,945 individuals.
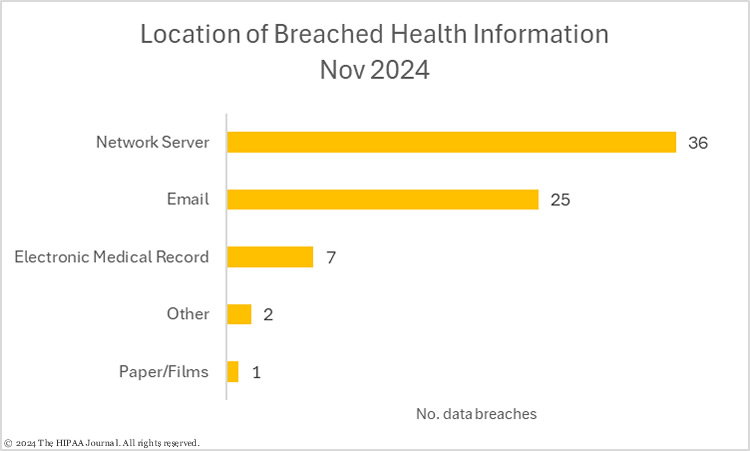
Typically, the most common location of breached protected health information is network servers. In October 60% of the month’s data breaches involved protected health information stored on network servers, but the percentage fell to 53% in November due to a significant increase in email-related data breaches. In October, 26% of the month’s breaches involved protected health information in email accounts, which jumped to 36% of data breaches in November, with 25 email account breaches reported.
The HHS Health Sector Cybersecurity Coordination Center (HC3) has recently issued a warning to HIPAA-regulated entities about ongoing credential harvesting campaigns. Setting and enforcing password complexity requirements (per the latest NIST guidance), conducting regular security awareness training, and implementing multi-factor authentication can help to prevent these email breaches.
Where did the Data Breaches Occur?
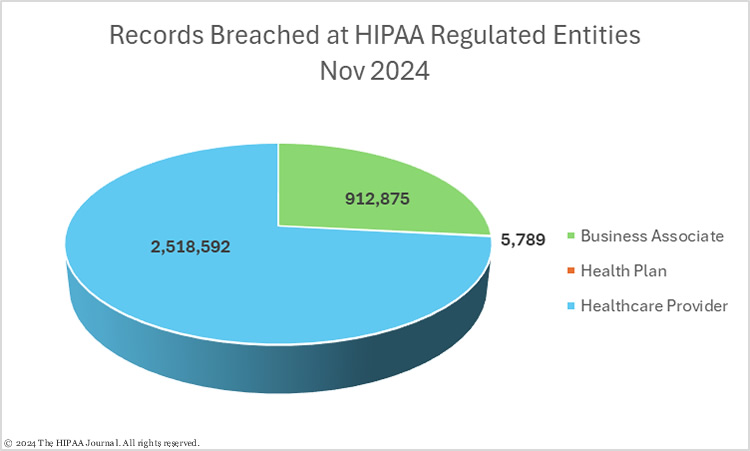
Healthcare providers reported 57 data breaches in November (2,561,190 records), 2 data breaches were reported by health plans (5,789 records), and there were no data breaches at healthcare clearinghouses. Data breaches were reported by 9 business associates of HIPAA-covered entities (870,277 records).
When a data breach occurs at a business associate, the business associate must report the data breach to each affected covered entity, and a decision must be made about who should send out individual notifications and notify the HHS’ Office for Civil Rights. Some covered entities choose to report business associate breaches to OCR and issue their own notifications, and if a business associate works with multiple covered entities, some may choose to send their own notifications while others delegate that responsibility to the business associate.
That means data breaches at business associates are often underrepresented in data breach reports. The HIPAA Journal calculates where the breach occurred rather than the entity that reported the breach to ensure business associate data breaches are reported accurately. As you can see in the pie chart below, while 9 data breaches were reported by business associates in November, another 9 data breaches occurred at business associates but were reported by the affected covered entities. The pie charts below are based on the location of the breach rather than the reporting entity.
Geographical Distribution of Healthcare Data Breaches
Illinois was the worst-affected state with 8 data breaches reported by HIPAA-regulated entities; however, the data breaches were relatively small and involved just 19,484 records. New York suffered two fewer breaches, but 91,533 individuals were affected.
| State | Breaches |
| Illinois | 8 |
| New York & Texas | 6 |
| Michigan | 5 |
| Missouri & Ohio | 4 |
| California, Florida, Massachusetts, Oklahoma & Virginia | 3 |
| Colorado, Indiana, Montana, North Carolina, Pennsylvania & Tennessee | 2 |
| Connecticut, Georgia, Iowa, Kentucky, Maryland, New Hampshire, Oregon & Washington | 1 |
There were also 6 breaches reported by HIPAA-regulated entities in Texas. They included the two largest data breaches of the month (Texas Tech University Health) and affected 14,465,000 individuals – 92% of the state’s total for the month.
| State | Individuals Affected |
| Texas | 1,586,577 |
| Colorado | 446,491 |
| Tennessee | 413,066 |
| Missouri | 326,725 |
| Oklahoma | 174,301 |
HIPAA Enforcement Activity in November 2024
The HHS’ Office for Civil Rights announced two resolutions of HIPAA violation cases in November; one civil monetary penalty and one settlement. Rio Hondo Community Mental Health Center in California was investigated after OCR received a complaint from a patient who claimed not to have been provided with a copy of their medical records within 30 days of submitting a request. Due to a stay-at-home order issued by California Governor Gavin Newsom due to COVID-19, the records could not be provided for 2 months as the center was not physically open; however, the records were not provided until 5 months after the stay-at-home order expired. OCR determined the delay violated the HIPAA Privacy Rule and that the evidence submitted by the mental health center did not support a waiver of a civil monetary penalty (CMP). OCR imposed a CMP of $100,000 to resolve the HIPAA violation. This was the 51st HIPAA Right of Access case to be resolved by OCR.
Holy Redeemer Family Medicine was investigated over an alleged impermissible disclosure of a patient’s reproductive health information to the patient’s prospective employer. OCR received a complaint from a patient alleging she gave permission to Holy Redeemer Family Medicine to release the results of a single medical test to her prospective employer – a test unrelated to reproductive healthcare. An employee mistakenly disclosed the patient’s entire medical record to the prospective employer. Holy Redeemer Family Medicine chose to settle the alleged HIPAA Privacy Rule violation and paid a $35,581 penalty.
About This Report
The data for this report was obtained from the HHS’ Office for Civil Rights on December 20, 2024, and has been supplemented with information from HIPAA Journal breach reporting and other media sources. HIPAA-regulated entities may amend their breach reports after they have been submitted to OCR when more information is known about the data breach, such as the number of affected individuals.
The HIPAA Journal does not update past monthly data breach reports to reflect any changes that come to light after publication; however, they will be reflected in future monthly breach reports and on our healthcare data breach statistics page, which is updated regularly.