OCR Encourages Healthcare Organizations to Conduct a Gap Analysis
In its April 2018 cybersecurity newsletter, OCR draws attention to the benefits of performing a gap analysis in addition to a risk analysis. The latter is required to identify risks and vulnerabilities that could potentially be exploited to gain access to ePHI, while a gap analysis helps healthcare organizations and their business associates determine the extent to which they are compliant with specific elements of the HIPAA Security Rule.
The Risk Analysis
HIPAA requires covered entities and their business associates to perform a comprehensive, organization-wide risk analysis to identify all potential risks to the confidentiality, integrity, and availability of ePHI – 45 CFR § 164.308(a)(1)(ii)(A).
If a risk analysis is not performed, healthcare organizations cannot be certain that all potential vulnerabilities have been identified. Vulnerabilities would likely remain that could be exploited by threat actors to gain access to ePHI.
While HIPAA does not specify the methodology that should be used when conducting risk analyses, OCR explained in its newsletter that risk analyses must contain certain elements:

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
- A comprehensive assessment of all risks to all ePHI, regardless of where the data is created, received, maintained, or transmitted, or the source or location of ePHI.
- All locations and information systems where ePHI is created, received, maintained, or transmitted must be included in the risk analysis, so an inventory should be created that includes all applications, mobile devices, communications equipment, electronic media, networks, and physical locations in addition to workstations, servers, and EHRs.
- The risk analysis should cover technical and non-technical vulnerabilities, the latter includes policies and procedures, with the former concerned with software flaws, weaknesses in IT systems, and misconfigured information systems and security solutions.
- The effectiveness of current controls must be assessed and documented, including all security solutions such as AV software, endpoint protection systems, encryption software, and the implementation of patch management processes.
- The likelihood that a specific threat will exploit a vulnerability and the impact should a vulnerability be exploited must be assessed and documented.
- The level of risk should be determined for any specific threat or vulnerability. With a risk level assigned, it will be easier to determine the main priorities when mitigating risks through the risk management process.
- The risk analysis must be documented in sufficient detail to demonstrate that a comprehensive, organization-wide risk analysis has been conducted, and that the risk analysis was accurate and covered all locations, devices, applications, policies, and procedures involving ePHI. OCR will request this documentation in the event of an investigation or compliance audit.
- A risk analysis is not a one-time event to ensure compliance with the HIPAA Security Rule – It must part of an ongoing process for continued compliance. The process must be regularly reviewed and updated, and risk analyses should be performed regularly. HIPAA does not stipulate how frequently a full or partial risk analysis should be performed. OCR suggests risk analyses are most effective when integrated into business processes.
Once a risk analysis has been performed, all risks and vulnerabilities identified must be addressed through a HIPAA-compliant security risk management process – 45 CFR § 164.308(a)(1)(ii)(B) – to reduce those risks to a reasonable and appropriate level.
Guidance on conducting an organization-wide risk analysis can be found on this link (HHS)
The Gap Analysis
A gap analysis is not a requirement of HIPAA Rules, although it can help healthcare organizations confirm that the requirements of the HIPAA Security Rule have been satisfied.
A gap analysis can be used as a partial assessment of an organizations compliance efforts or could cover all provisions of the HIPAA Security Rule. Several gap analyses could be performed, each assessing a different set of standards and implementation specifications of the HIPAA Security Rule.
The gap analysis can give HIPAA-covered entities and their business associates an overall view of their compliance efforts, can help them discover areas where they are yet compliant with HIPAA Rules, and identify any gaps in the controls that have already been implemented.
Note that a gap analysis is not equivalent to a risk analysis, as it does not cover all possible risk to the confidentiality, integrity, and availability of ePHI as required by 45 C.F.R. §164.308(a)(1)(ii)(A).
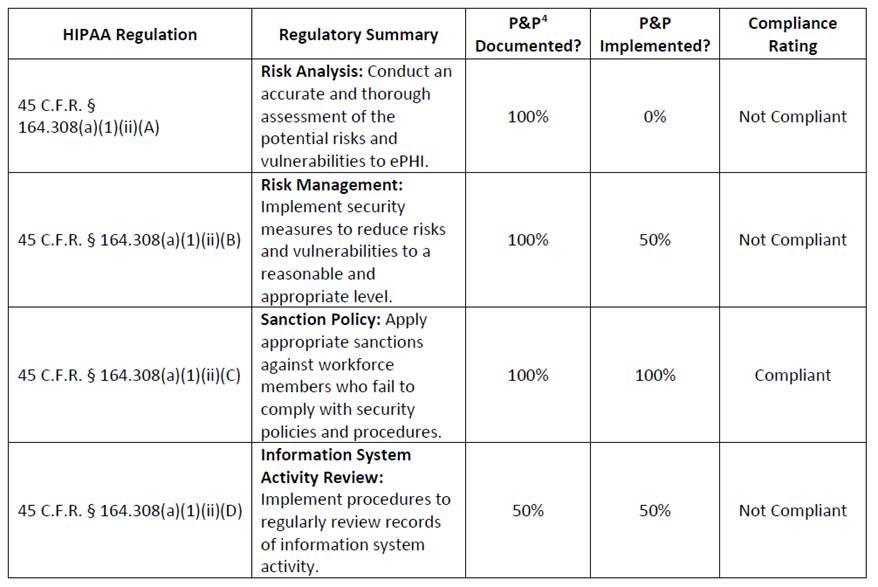
OCR offers the following example of a simple gap analysis:
Source: OCR