OCR Imposes $240,000 HIPAA Fine on Californian Healthcare Provider
The Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has imposed a $240,000 civil monetary penalty on Providence Medical Institute to resolve potential violations of two provisions of the HIPAA Security Rule. This is the fifth investigation of a ransomware attack to result in a penalty for noncompliance with the HIPAA Rules.
Providence Medical Institute (PMI) is a Californian healthcare provider that acquired a full-scope orthopedic medical service provider – Center for Orthopaedic Specialists (COS) – in July 2016. PMI planned to fully integrate COS as a PMI unit within 2 years, although the integration was delayed until May 2019. On February 18, 2018, a ransomware group encrypted files on COS systems. The threat actor gained a foothold in the network after an employee responded to a phishing email and disclosed their credentials. Within a few days of the encryption event, systems were restored from backup tapes; however, on February 25, 2018, COS systems were encrypted a second time. Within a few days, files were restored from backup tapes for a second time, only for them to be encrypted for a third time on March 4, 2018. The repeat attacks were thought to have been conducted by the same threat actor, who retained access to systems after data was restored from backups. In the third attack, the threat actor had remote desktop access to COS systems using administrator credentials believed to have been obtained in either the first or second attack.
According to OCR, a breach report was received from COS-PMI on April 18, 2024, involving the PHI of 85,000 individuals (The OCR breach report currently shows the breach as affecting 81,550 individuals). The data compromised in the attack included names, addresses, dates of birth, driver’s license numbers, Social Security numbers, lab results, medications, treatment information, credit card information, bank account numbers, and other financial information.
Around three months after the attack, PMI conducted a post-incident assessment of COS systems and found multiple security failures. At the time of the attacks, COS was using unsupported and obsolete operating systems to host its ePHI data. A demilitarized zone (DMZ) network had not been enabled or configured to separate its private network from the public internet and untrusted networks. The COS firewall had not been correctly configured to monitor and track access or changes to its network. Remote Desktop Protocols (RDPs) had been enabled which allowed insecure remote access to COS workstations from external sources. There was no encryption of electronic protected health information (ePHI) on the network and members of the COS workforce were sharing generic credentials that provided administrative access to workstations.
OCR’s investigation found that COS was using an IT vendor – CSnC – which provided data management services for its network, which required access to COS eClinicalWorks servers containing ePHI. The business relationship required CSnC to manage the ePHI on the servers, yet there was no business associate agreement with the vendor until June 15, 2018. OCR determined that the lack of a business associate agreement between July 2016 and June 2018 was in violation of 45 C.F.R. § 164.308(b) of the HIPAA Security Rule. There were also insufficient technical policies and procedures for restricting access to systems containing ePHI to only individuals and software authorized to access the data, in violation of 45 C.F.R. § 164.312(a)(1) of the HIPAA Security Rule. That violation persisted until May 23, 2019, when COS systems were fully integrated into those of PMI.
OCR attempted to resolve the alleged violations through informal means, but when those attempts failed, OCR offered PMI the opportunity to submit evidence as a mitigating factor. OCR rejected the arguments put forward by PMI as providing a basis for an affirmative defense and moved to impose a civil monetary penalty. “Failures to fully implement all of the HIPAA Security Rule requirements leaves HIPAA covered entities and business associates vulnerable to cyberattacks at the expense of the privacy and security of patients’ health information,” said OCR Director Melanie Fontes Rainer. “The health care sector needs to get serious about cybersecurity and complying with HIPAA. OCR will continue to stand up for patient privacy and work to ensure the security of health information of every person. On behalf of OCR, I urge all health care entities to always stay alert and take every precaution and steps to keep their systems safe from cyberattacks.”
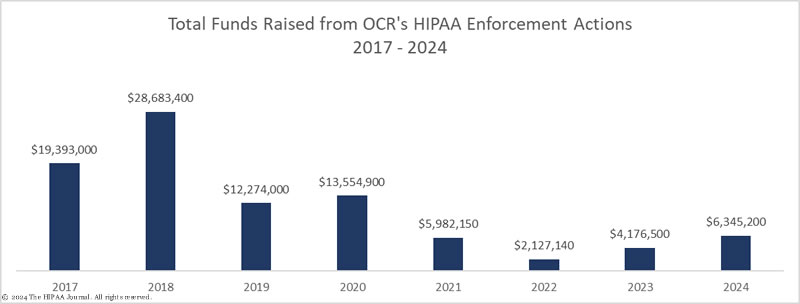
This is the 8th HIPAA enforcement action in 2024 to result in a financial penalty. OCR has imposed 3 civil monetary penalties to resolve potential HIPAA violations and has entered into 5 settlements. The latest settlement would have been 20% higher; however, OCR reduced the financial penalty by $60,000 as Providence Medical Institute demonstrated it had implemented recognized security practices for 12 continuous months prior to the attack.