Ransom Payment Increase Driven by Accellion FTA Data Exfiltration Extortion Attacks
The increase in ransomware attacks in 2020 has continued in 2021 with healthcare one of the most targeted industries, according to the latest Coveware Quarterly Ransomware Report. Healthcare ransomware attacks accounted for 11.6% of all attacks in Q1, 2021, on a par with attacks on the public sector and second only to attacks on firms in professional services (24.9%).
While ransom demands declined in Q4, 2020, that trend abruptly stopped in Q1, 2021 with the average ransom payment increasing by 43% to $220,298 and the median ransom payment up 59% to $78,398. The increase in payments was not due to ransomware attacks but data exfiltration extortion attacks by the Clop ransomware gang.
The Clop ransomware gang exploited two zero-day vulnerabilities in the Accellion legacy File Transfer Appliance, exfiltrated customers’ data, then threatened to publish the stolen data if the ransom was not paid. When victims refused to pay, the stolen data were leaked on the Clop ransomware data leak site.
These attacks show that file encryption is not always necessary, with the threat of publication of stolen data often sufficient to ensure payment is made. Coveware notes that while exploitation of the vulnerabilities allowed data to be exfiltrated, it was not possible to deploy ransomware across victims’ networks, otherwise ransomware would most likely have also been used in the attacks.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
The Clop ransomware gang was particularly active in Q1, 2020. The group often attacks large enterprises and demands huge ransoms and like many other ransomware gangs, steals data prior to file encryption and threatens to expose that data if payment is not made. These double extortion tactics have become the norm and most ransomware attacks now involve data exfiltration. In Q1, 77% of ransomware attacks involved data exfiltration up from 70% in Q4, 2020.
Ransomware victims may have no choice other than paying the ransom if they are unable to recover encrypted data from backups, but there are risks associated with paying the ransom demand, especially to prevent a data leak. There is no guarantee that data will be destroyed and could still be traded or sold to other threat groups after payment is made. Exfiltrated data may also be stored in multiple locations. Even if the threat actor destroys the data, third parties may still have a copy. Coveware notes that while data exfiltration has increased, a growing number of ransomware victims are electing not to give in to the attackers’ demands and are refusing to pay the ransom to prevent a data leak for these and other reasons.
“Over hundreds of cases, we have yet to encounter an example where paying a cybercriminal to suppress stolen data helped the victim mitigate liability or avoid business / brand damage.” – Coveware.
Many RaaS operations have increased the number of attacks by recruiting more affiliates, but some RaaS operations have struggled to scale up their operations. The Conti gang outsourced their chat operations which made negotiations and recoveries more difficult. The Lockbit and BlackKingdom gangs experienced technical difficulties which resulted in permanent data loss for some of their victims, and even the most prolific ransomware operation – Sodinokibi – experienced problems matching encryption keys with victims resulting in permanent data loss.
These technical problems show that even ransomware operations that intend to provide the keys to decrypt data are not always able to. Coveware also observed a worrying trend where ransomware gangs deliberately disrupt recovery after the ransom is paid. The Lockbit and Conti gangs were observed attempting to steal more data during the recovery phase and even attempting to re-launch their ransomware after victims have paid. Coveware notes that this kind of disruption was rare in 2020, but it is becoming more common. Technical issues and disruption to the recovery process have contributed to an increase in downtime due to an attack, which is up 10% in Q1 to 23 days.
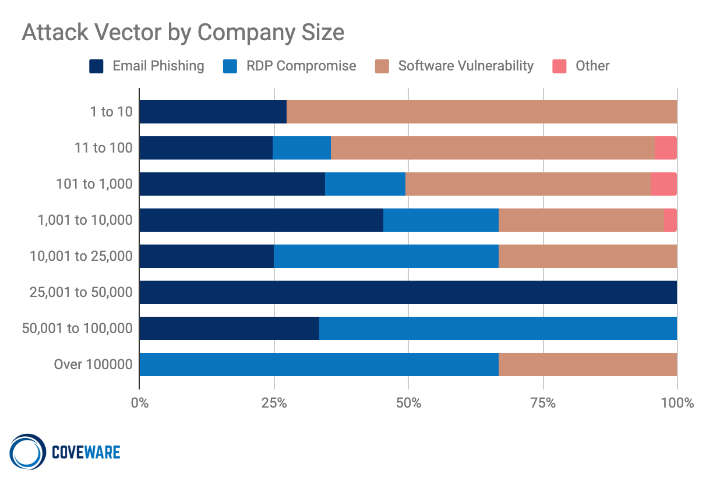
In Q4, email phishing became the most common method of ransomware delivery, but Remote Desktop Protocol connections are once again the most common method of gaining access to victim networks. Phishing is still commonly used and is the method of attack favored by the Conti ransomware gang – the second most prevalent ransomware operation in Q1.
Exploitation of software vulnerabilities also increased, with unpatched vulnerabilities in Fortinet and Pulse Secure VPN appliances the most commonly exploited flaws. Coveware believes the majority of ransomware-as-a-service operators and affiliates do not exploit software vulnerabilities, instead they pay specialist threat actors for access to compromised networks. Those threat actors mostly target smaller organizations, with RDP the most common method of attack for larger organizations.