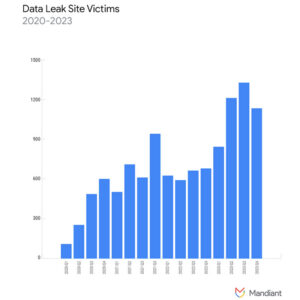
Ransomware Victim Count Increased by 75% in 2023
A new report from the Google-owned cybersecurity firm Mandiant has confirmed that there was a significant rise in ransomware activity in 2023 compared to 2022 and that the slight fall in ransomware and extortion activity in 2022 was an anomaly that was due, in part, to the invasion of Ukraine and the leaked Conti chats.
Mandiant has been tracking the activities of ransomware groups and reports a 75% increase in the number of victims that were added to the groups’ data leak sites in 2023, which peaked in Q3, 2023 when almost 1,400 new victims were listed. The percentage of cyberattacks involving ransomware that Mandiant has investigated increased by 20% in 2023. Mandiant’s findings are consistent with other reporting, such as a report from Chainalysisthat showed a record amount was paid to ransomware groups in 2023, with payments topping $1 billion for the first time.
In 2023, law enforcement agencies around the world stepped up their efforts to disrupt the operations of ransomware groups, including international law enforcement operations against two of the most prolific ransomware groups, LockBit and ALPHV/Blackcat. While those operations resulted in seized infrastructure and disruptions, only a handful of individuals were arrested, the core members of the groups are still at large, and most affiliates continued to conduct attacks, either with the same group or with other ransomware-as-a-service (RaaS) operations.
The attacks tracked by Mandiant were spread across 110 countries and involved more than 50 new ransomware families and variants, a number consistent with new variants and families observed in 2021 and 2022. One change that was observed in 2023 was an increase in the proportion of new variants to new families, indicating ransomware groups are concentrating on updating existing ransomware families rather than creating new families from scratch. Many of the new detections included code from other ransomware families, were rebrands of existing ransomware groups or had actor overlaps. Mandiant also observed a broadening of systems targeted by attacks, with the number of ransomware variants capable of encrypting data on Linux and ESXi systems increasing throughout 2023.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
After networks are compromised, most ransomware actors use commercially available, legitimate tools for their post-compromise activities before deploying their ransomware payloads. Mandiant has observed a decline in the use of Cobalt Strike BEACON with attackers favoring legitimate remote access tools. In 2023, 41% of intrusions involved legitimate remote access and management tools compared to 23% in 2022. In 2023, the main initial access vectors were the exploitation of known vulnerabilities, stolen credentials, brute force attacks, phishing, and web compromise, including SEO poisoning and malvertising. Vulnerabilities were exploited for initial access in 30% of attacks and the CitrixBleed flaw – CVE-2023-4966 – was one of the most widely exploited. Stolen credentials were used in 25% of attacks, brute force tactics in 14% of attacks, and a further 14% used phishing. Around 59% of ransomware attacks involved confirmed or suspected data theft.
The median dwell time between initial access and ransomware deployment increased slightly from 5 days in 2022 to 6 days in 2023, although this is significantly lower than the median time of 21 days in 2017 and 2019 and almost twice as long as the median time of 3.5 days in 2020. In 2023, almost one-third of attacks saw ransomware deployed within 48 hours of the initial compromise, and the majority of attacks were timed to coincide with periods of lower vigilance. 76% of attacks saw ransomware deployed outside of working hours when staffing levels are at their lowest to increase the probability of the attack going undetected. The most common time for ransomware to be deployed was in the early morning.
Mandiant suggests several reasons for the increase in attacks. First, there has been a resetting of the cybercriminal ecosystem after a tumultuous year in 2022, an influx of new actors conducting attacks, new partnerships between existing groups, and members of disrupted, prolific ransomware groups such as Conti starting up their own RaaS operations. While the attacks in 2023 largely followed the same patterns as the previous year, there were some notable changes with several groups trialing new tactics, techniques, and procedures. For example, to increase the pressure on victims to pay, attacks on healthcare providers saw extortion demands issued to patients whose data were stolen, threatening to publish their medical data if they did not personally pay a ransom. The ALPHV group created a searchable database to make stolen data more accessible, and threats were issued to report attacks on publicly traded companies to the Securities and Exchange Commission (SEC).