September 2024 Healthcare Data Breach Report
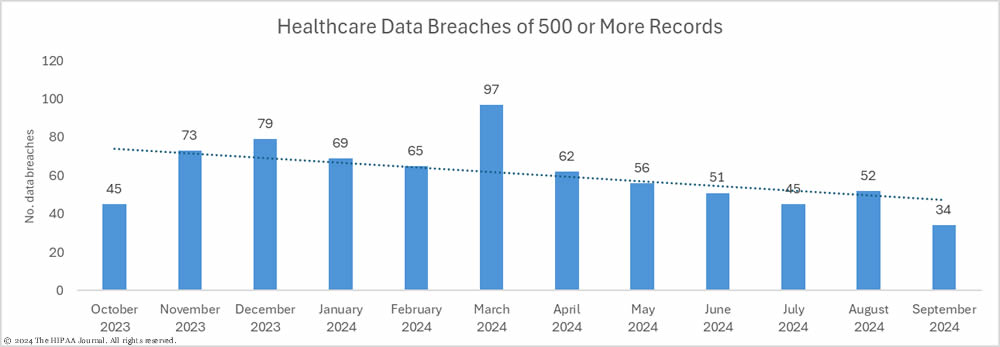
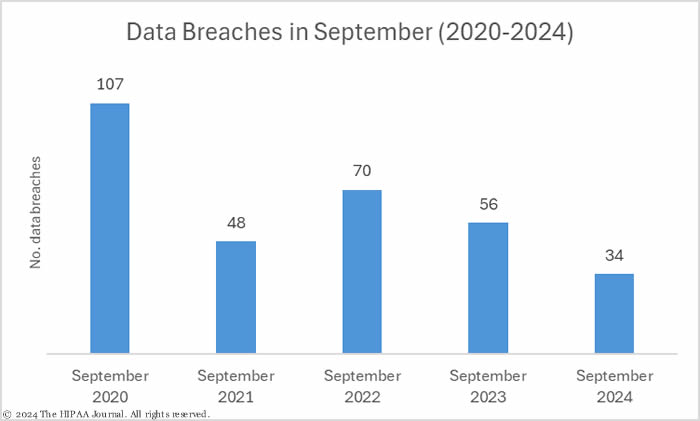
Apart from a blip in August, the number of healthcare data breaches reported each month has fallen from an annual high of 97 breaches in March 2024. September saw the lowest number of healthcare data breaches since May 2020, with just 34 data breaches of 500 or more records reported to the Department of Health and Human Services (HHS) Office for Civil Rights (OCR).
In the first half of the year it was looking like another new record would be set for healthcare data breaches, but as the year draws to an end, 2024 is now looking like it will be a rare year where the number of healthcare data breaches reduces year-over-year. So far in 2024, 531 data breaches of 500 or more records have been reported to OCR. In the first half of 2024, data breaches were reported at a rate of 67 a month. In the second half of 2024, data breaches have been reported at a rate of 44 a month.
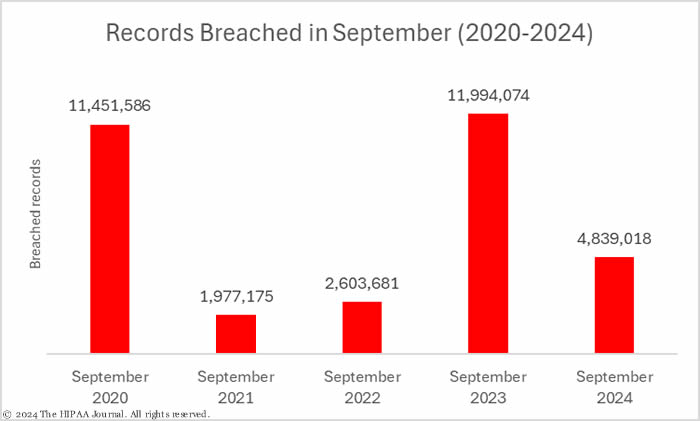
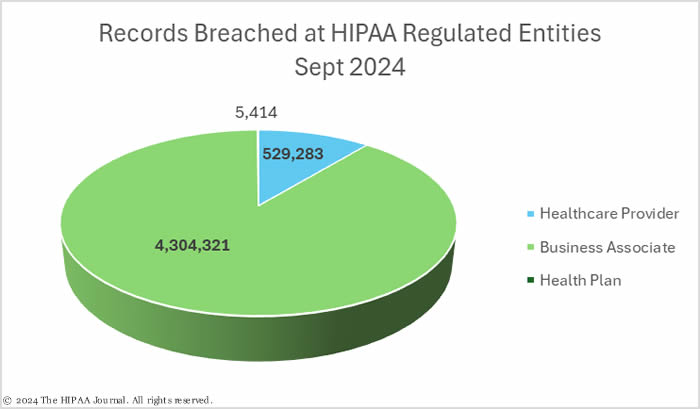
Across the 34 reported data breaches, the records of 4,839,018 individuals were exposed or impermissibly disclosed – The third lowest monthly total of the year to date, and well below the average of 7,082,007 records a month for the first 9 months of 2024.
Between January 1 and September 30 this year, the protected health information of 63,738,063 individuals was exposed or impermissibly disclosed. That total includes 52 breaches that were reported to OCR as affecting 500 or 501 individuals – placeholders often used when the total number of affected individuals has yet to be determined. One of those is the data breach at Change Healthcare, which was reported using a placeholder of 500 affected individuals, even though UnitedHealth Group CEO said the breach may affect a substantial proportion of Americans.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Biggest Healthcare Data Breaches in September 2024
In September, there were 13 healthcare data breaches of 10,000 or more records and 4 breaches reported with potential placeholder figures of 500 or 501 records. The largest confirmed breach was reported by the Department of Health and Human Services’ Centers for Medicare and Medicaid Services (CMS) and was one of many breaches due to the mass exploitation of a vulnerability in Progress Software’s MOVEit file transfer solution in May 2023.
The file transfer solution was used by a CMS business associate, Wisconsin Physicians Service Insurance Corporation, which investigated a potential breach in 2023 but did not find evidence that the Clop group had exfiltrated files. In May 2024, a year after the vulnerability was exploited, new evidence indicated files had been exfiltrated. It was determined that 947,000 individuals were affected; however, it has now been confirmed that the protected health information of more than 3 million individuals was stolen in the attack.
The next two biggest data breaches of the month were both confirmed ransomware attacks, a BlackSuit ransomware attack on the Georgia business associate Young Consulting involving the protected health information of more than 950,000 individuals and a ransomware attack on Muskogee City County Enhanced 911 Trust Authority in Oklahoma, which affected 180,000 individuals. Several email account breaches were reported in September, including 5 breaches of 10,000 or more records. The largest email breach was reported by Michigan Medicine, its second email breach of the year.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Breach |
| Centers for Medicare & Medicaid Services | MD | Health Plan | 3,112,815 | Exploited vulnerability (MOVEit) at business associate (Wisconsin Physicians Service Insurance Corporation) by the Clop threat group |
| Young Consulting LLC | GA | Business Associate | 954,177 | Ransomware attack (BlackSuit) with confirmed data theft |
| Muskogee City County Enhanced 911 Trust Authority | OK | Business Associate | 180,000 | Ransomware attack |
| Community Clinic of Maui, Inc. dba Malama I Ke Ola Health Center | HI | Healthcare Provider | 123,816 | Hacked network server |
| Richland County, WI | WI | Healthcare Provider | 76,365 | Hacked network server |
| Asheville Arthritis and Osteoporosis Center, P.A. | NC | Healthcare Provider | 58,251 | Hacked network server |
| University of Michigan/Michigan Medicine | MI | Healthcare Provider | 57,891 | Unauthorized access to email account (Phishing attack) |
| Guam Seventh-Day Adventist Clinic | GUAM | Healthcare Provider | 56,635 | Unauthorized access to email accounts |
| Prentke Romich Company dba PRC-Saltillo | OH | Healthcare Provider | 51,627 | Hacked network server – Data theft confirmed |
| Atrium Health | NC | Healthcare Provider | 32,120 | Unauthorized access to email accounts (Phishing attack) |
| Hafetz and Associates | NJ | Business Associate | 26,474 | Unauthorized access to email accounts (Phishing attack) |
| ERLC LLC, d/b/a Elitecare Emergency Hospital | TX | Healthcare Provider | 24,754 | Hacked network server |
| JTaylor & Associates LLC | TX | Business Associate | 22,315 | Unauthorized access to email accounts |
Causes of September 2024 Healthcare Data Breaches
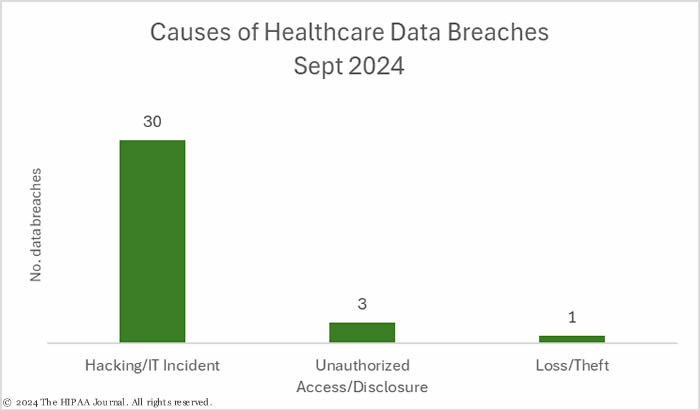
In September, 30 of the month’s data breaches were hacking/IT incidents (88%), 3 were unauthorized access/disclosure incidents (8.8%), and there was 1 theft incident (2.9%). There were no improper disposal or loss incidents in September.
The vast majority (99.85%) of the breached records were the result of hacking incidents. Across those 30 breaches, the records of 4,831,775 individuals were exposed or compromised. The average size of a hacking/IT incident in September was 161,059 records and the median breach size was 7,836 records.
Three relatively small unauthorized/disclosure incidents were reported involving a total of 4,625 records. The average size of these breaches was 1,542 records and the median breach size was 778 records. The theft incident involved the electronic records of 2,618 individuals, which were stored on electronic devices that were stolen from a medical center in Puerto Rico.
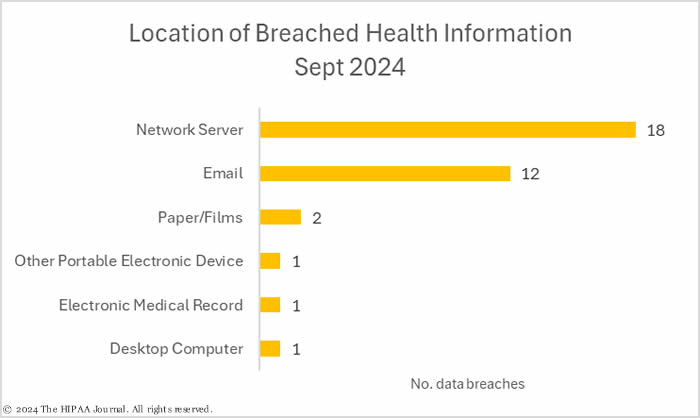
The most common location of breached protected health information in September was network servers, which is unsurprising due to the number of hacking incidents; however, only 52% of the breaches involved network servers – 35% involved compromised email accounts.
Where did the Data Breaches Occur?
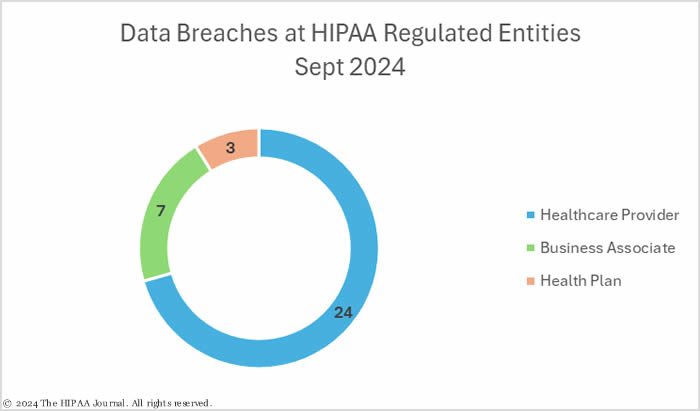
In September, 24 breaches were reported by healthcare providers, 6 by business associates, and four by health plans. When a data breach occurs at a business associate, it is often reported by the business associate; however, some covered entities choose to report the breach themselves even though the breach occurred at a business associate, as was the case with the CMS breach in September. It is not unusual for a business associate to report a breach for some covered entity clients while others report the breach themselves.
As a result, data breaches at business associates are often underrepresented in data breach reports. The HIPAA Journal calculates where the breach occurred rather than the entity that reported the breach to ensure business associates are reported accurately. The pie charts below are based on the location of the breach rather than the reporting entity.
Geographical Distribution of Healthcare Data Breaches
Texas was the worst affected state with 5 data breaches of 500 or more records, although only 57,123 individuals were affected by those breaches. The worst affected states in terms of the number of individuals affected were Maryland (3,112,815 records), Georgia (954,678 records), Oklahoma (180,000 records), and Hawaii (123,816 records).
| State | Breaches |
| Texas | 5 |
| California, Georgia, Michigan, New Jersey, North Carolina, Ohio & Pennsylvania | 2 |
| Arizona, Connecticut, Florida, Hawaii, Illinois, Maine, Maryland, Mississippi, New Hampshire, New York, Oklahoma, Utah, Wisconsin, Guam & Puerto Rico | 1 |
HIPAA Enforcement Activity in September 2024
OCR announced one HIPAA enforcement action in September that resulted in a financial penalty. Cascade Eye and Skin Centers, a Washington-based healthcare provider, fell victim to a ransomware attack in March 2017. The ransomware group had access to a server containing 291,000 files that contained patient data.
OCR investigated to determine if Cascade Eye and Skin Centers was in compliance with the HIPAA Rules and identified two common compliance issues – the failure to conduct a comprehensive, accurate, organization-wide risk analysis to identify potential risks and vulnerabilities to electronic protected health information and insufficient reviews of activity in information systems containing ePHI. The settlement includes a $250,000 financial penalty and a comprehensive corrective action plan to address the areas of noncompliance. This was the 8th financial penalty of the year and OCR’s fourth ransomware investigation to result in a financial penalty.