Study Shows Only 49% of Hospitals Use 2-Factor Authentication to Improve ePHI Security
Under HIPAA Rules, access to Protected Health Information must be strictly controlled. HIPAA-covered entities must therefore implement technical safeguards to ensure that only authorized individuals are able to gain access to data. EHRs and other software systems that are used to store or send ePHI must be protected by a minimum of a username and password, and any attempt to gain access to ePHI must be logged and periodically audited.
Improving ePHI Security with Two-Factor Authentication
Data security can be greatly enhanced by the use of two-factor authentication. Two factor authentication requires an additional identification factor (other than a username/password combo) to be entered prior to access to ePHI being granted. Under the HIPAA Security Rule – 45 CFR § 164 – this control is strongly advisable but not mandatory; however, under the DEA’s Electronic Prescription for Controlled Substances rules, it is mandatory for 2-factor authentication to be used by all entities that e-prescribe controlled substances.
Typically, the additional factor is a security question, a code sent to an email address or mobile phone, or any other data element that can be used to confirm the identity of an individual. This additional control is important in case a password is accidentally divulged or is guessed. Many web services now require the use of two-factor authentication as a protection against hacking of individual accounts, and it is strongly advisable for HIPAA-covered entities to do the same.
First Study on the Use of Two-Factor Authentication by Non-Federal Acute Care Hospitals
Last month the Office for the National Coordinator for Health Information Technology published the results of a study on non-federal acute care hospitals’ use of two-factor authentication to improve ePHI security. This is the first time state and federal trends have been analyzed on this security control.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
The results of the study show significant improvements have been made since 2010, with an increase of 53% of non-federal acute care hospitals using this additional security control being recorded between 2010 and 2014. However, even with the current high threat of healthcare hacking, only 49% of hospitals are employing 2-factor authentication.
Perhaps unsurprisingly, larger healthcare facilities were more likely to employ the additional security measure than smaller healthcare providers. 63% of large hospitals had capability for two-factor authentication compared to just 40% of small rural hospitals and 35% of critical access facilities.
There was also considerable variation between states. Ohio was shown to be the most secure state with 93% of hospitals using the ePHI security control. Vermont (83%) and Connecticut (81%) were the only two other states having between 80% and 100% of hospitals using 2-factor authentication. Montana had the lowest percentage of hospitals using the control, with fewer than 20% of hospitals having the capability for two-factor authentication. Rhode Island did not meet the standard for reliability and was therefore excluded from the figures.
Use of 2-Factor Authentication Controls to Secure ePHI by State
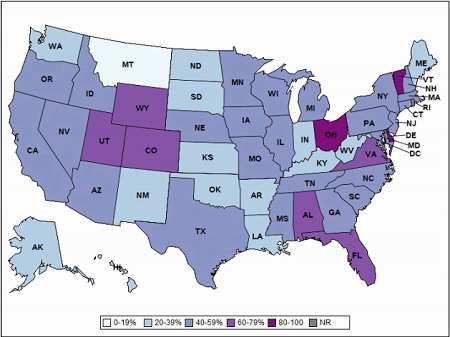
SOURCE: ONC/American Hospital Association (AHA), AHA Annual Survey Information Technology Survey, 2014
The full ONC report can be downloaded here.



