Verizon: Healthcare Phishing and Ransomware Attacks Increase while Insider Breaches Fall
2020 was certainly not a typical year. The pandemic placed huge pressures on IT security teams and businesses were forced to rapidly accelerate their digital transformation plans and massively expand their remote working capabilities. Cyber actors seized the opportunities created by the pandemic and exploited vulnerabilities in security defenses to gain access to business networks and sensitive data.
In 2020, phishing and ransomware attacks increased, as did web application attacks, according to the recently published Verizon 2021 Data Breach Investigations Report. The report provides insights into the tactics, techniques and procedures used by nation state actors and cybercriminal groups and how these changed during the pandemic.
To compile the Verizon 2021 Data Breach Investigations Report, the researchers analyzed 79,635 incidents, of which 29,207 met the required quality standards and included 5,258 confirmed data breaches in 88 countries – one third more data breaches than the previous year’s DBIR.
2020 saw an 11% increase in phishing attacks, with cases of misrepresentation such as email impersonation attacks at 15 times the level of 2019. There was a 6% increase in ransomware attacks, with 10% of all data breaches in 2020 involving the use of ransomware – Twice the level of the previous year.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Across all industry sectors, phishing was the main cause of data breaches and was involved in 36% of incidents. The researchers attributed the increase in phishing attacks to the pandemic, with COVID-19 and other related pandemic lures extensively used in targeted attacks on at-home workers. While phishing attacks and the use of stolen credentials are linked, the researchers found attacks involving stolen credentials were similar to the level of the previous year and were involved in 25% of breaches. Exploitation of vulnerabilities was also common, but in most cases it was not new vulnerabilities being exploited but vulnerabilities for which patches have been available for several months or years.
The increase in remote working forced businesses to move many of their business functions to the cloud and securing those cloud resources proved to be a challenge. Attacks on web applications accounted for 39% of all data breaches, far higher than the previous year. Attacks on external cloud assets were much more common than attacks on on-premises assets.
61% of data breaches involved credential theft, which is consistent with previous data breach investigation reports and 85% of data breaches involved a human element. In the majority of cases (80%), data breaches were discovered by a third party rather than the breached entity.
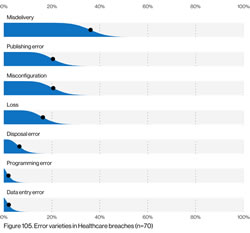
There were considerable variations in attacks and data breaches across the 12 different industry verticals represented in the report. In healthcare, human error continued to be the main cause of data breaches, as has been the case for the past several years. The most common cause of data breaches in misdelivery of paper and electronic documents (36%), but this was far higher in the financial sector (55%). In public administration, the main cause of data breaches was social engineering, such as phishing attacks to obtain credentials.
Verizon analyzed 655 healthcare security incidents, which included 472 data breaches. 221 incidents involved malware, 178 hacking, 137 human error, and 106 social attacks. For the second consecutive year, incidents involving malicious insiders have fallen out of the top three attack types. While it is certainly good news that the number of malicious insider incidents is falling, that does not mean that these incidents are no longer occurring. It could indicate malicious insiders are able to cover their tracks much better. Attacks by external threat actors significantly increased, with healthcare industry cyberattacks commonly involving the use of ransomware. 61% of incidents were the work of external threat actors and 39% were internal data breaches.
Interestingly, considering the value of medical data on the black market, medical data was not the most commonly breached data type. Medical data was breached in 55% of data breaches, with personal data breached in 66% of incidents. 32% of breached involved the theft of credentials. Verizon suggests that could be due to the opportunistic nature of attacks by external threat actors. “With the increase of External actor breaches, it may simply be that the data taken is more opportunistic in nature. If controls, for instance, are more stringent on Medical data, an attacker may only be able to access Personal data, which is still useful for financial fraud. Simply put, they may take what they can get and run.
Breach detection has been steadily improving since 2016, when the majority of data breaches took months or more to identify. The majority of data breaches are now being discovered in days or less, although most commonly not by the breached entity. 80% of data breaches were identified by a third party.
The cost of a data breach is now estimated to be $21,659 on average, with 95% of data breaches having a financial impact of between $826 and $653,587.