Web Application Attacks Double as Threat Actors Target Cloud Data
The 2020 Verizon Data Breach Investigations Report shows malware attacks are falling as threat actors target data in the cloud. This is the 13th year that the report has been produced, which this year contains an analysis of 32,002 security incidents and 3,950 confirmed data breaches from 81 global contributors in 81 countries.
The report confirms that the main motivator for conducting attacks is financial gain. 86% of all security breaches were financially motivated, up from 71% last year. 70% of breaches were due to external actors, with 55% of attacks conducted by cybercriminals.
67% of breaches were the result of credential theft or brute forcing of weak credentials (37%) and phishing and other social engineering attacks (25%). 22% of those breaches involved human error.
Only 20% of breaches were due to the exploitation of vulnerabilities. It should be noted that it is much easier to conduct attacks using stolen credentials rather than exploiting vulnerabilities, so the relatively low number of vulnerability-related attacks may not be due to organizations patching vulnerabilities more promptly.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
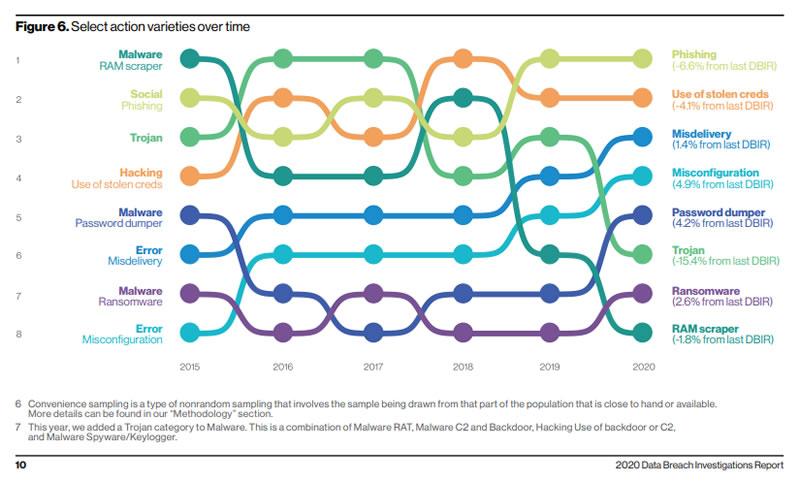
The ease of conducting attacks using stolen or brute forced credentials has seen malware attacks become less popular. That said, ransomware is proving to be an attractive option, which has seen an increase from 24% to 27% of all malware related attacks.
There was a significant increase in web application attacks over the past 12 months, which doubled to 43% of all breaches. 80% of those breaches involved credential theft. With more organizations moving their data from traditional domain controllers and internal infrastructure, it is no surprise that there has been a sizeable increase in attacks on the cloud.
The data collected for the report does not cover the period of the COVID-19 public health emergency, when many organizations accelerated their cloud migration plans to allow more employees to work from home. It is likely that next year’s report will see an even higher percentage of attacks on cloud resources.
“As remote working surges in the face of the global pandemic, end-to-end security from the cloud to employee laptop becomes paramount,” said Tami Erwin, CEO, Verizon Business. “In addition to protecting their systems from attack, we urge all businesses to continue employee education as phishing schemes become increasingly sophisticated and malicious.”
Attack Trends Over the Past 6 Years
Source: Verizon
Cyberattacks and Insider Breaches in Healthcare
Financially motivated cyberattacks accounted for 88% of healthcare breaches, with many of the attacks involving ransomware. 4% of healthcare cyberattacks were conducted for fun and 3% of attacks were conducted out of convenience.
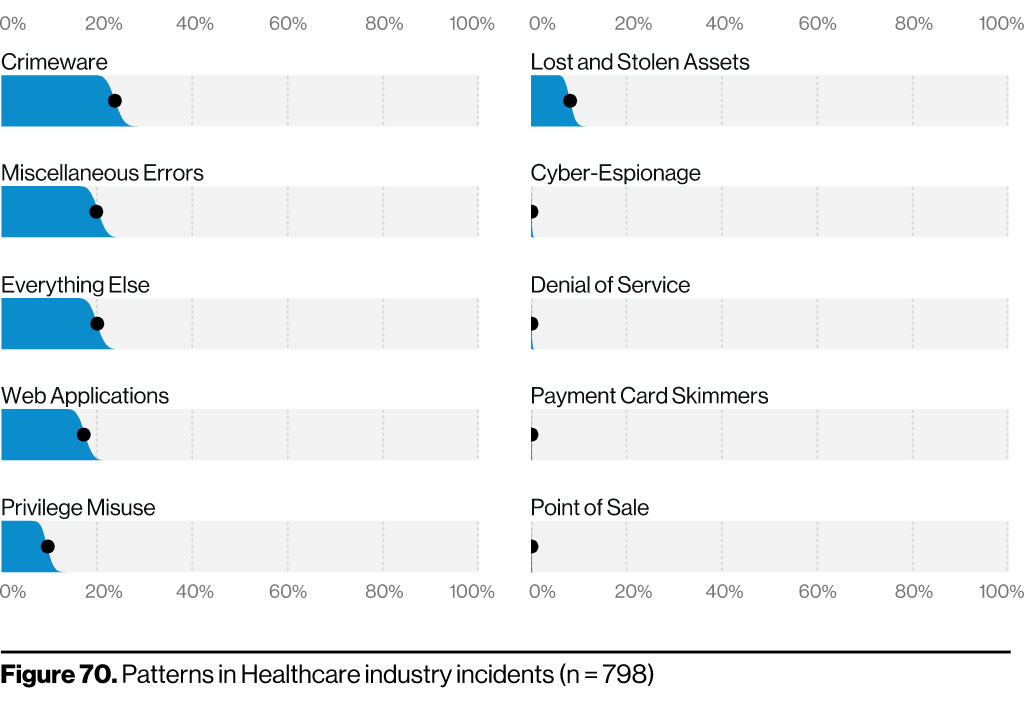
Verizon reports a significant increase in healthcare data breaches in the past 12 months. Last year’s report included 304 healthcare data breaches but this year the number has increased to 521 breaches. The figure below shows the patterns for cyberattacks in the healthcare industry. Crimeware includes malware and ransomware, which is the most common type of attack on healthcare organizations. As in other industry sectors, attacks on web applications are increasing.
Source: Verizon
The healthcare industry usually has a higher than average number of cases of privilege misuse, where insiders with access to sensitive data abuse their access rights to view or steal data. With so many employees given access to patient data and its high value on the black market, this is to be expected.
There is some good news in this year’s report. For the first time privilege misuse has dropped out of the top three causes of healthcare data breaches. This is part of a trend that can be seen across all industry sectors, which suggests that employees are thinking twice about accessing data without authorization and healthcare providers are getting better at protecting data.
Verizon notes that there has also been a decrease in breaches involving multiple actors, which is usually a third-party such as an identity thief working with an insider who supplies the data. In the 2019 report, 4% of breaches involved multiple actors whereas in 2020 the percentage dropped to 1%. The percentage of breaches caused by internal actors vs external actors also changed significantly. In the 2019 report, 59% of healthcare breaches were caused by internal actors with 42% caused by external attackers. This year’s report sees internal actors responsible for 48% of breaches with external actors accounting for 51% of breaches.
This year, the biggest cause of breaches in healthcare were miscellaneous errors and breaches of web applications. The main cause of those miscellaneous breaches was misdirection, which is the sending of emails to incorrect recipients and mass mailings that see letters sent to incorrect patients, such as happens when there is a mail merge error.