April 2024 Healthcare Data Breach Report
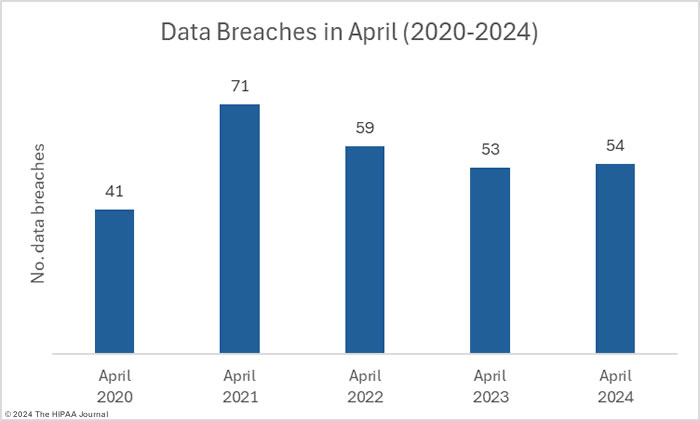
Healthcare data breaches fell 43% month-over-month, with 54 data breaches of 500 or more records reported to the HHS’ Office for Civil Rights. That’s the lowest monthly total so far this year, the second lowest monthly breach count in the past 12 months, and well below the 12-month average of 63 HIPAA data breaches a month.
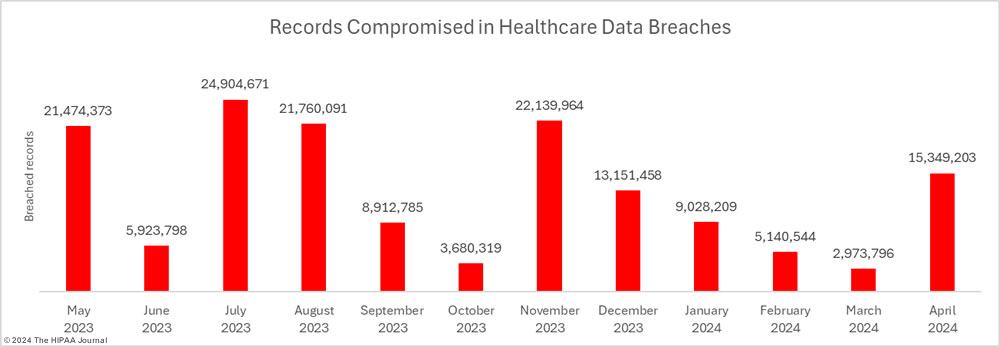
While the reduction in data breaches is great news, April was the worst month of the year to date in terms of breached healthcare records. Across the 54 data breaches, 15,349,203 records were reported as exposed or impermissibly disclosed. The number of breached records is likely to increase, as 5 breaches were reported as involving 500 or 501 records – placeholders commonly used for reporting breaches when the number of affected individuals has yet to be determined.
Biggest Healthcare Data Breaches Reported in April 2023
One breach that has not yet been included in the HIPAA Journal breach reports is the ransomware attack on Change Healthcare, as while this is undoubtedly the biggest data breach of the year, the number of affected individuals is still not known. At a recent House subcommittee hearing, UnitedHealth Group (UHG) CEO Andrew Witty confirmed that data was stolen in the attack but could not say how many individuals had been affected. When pressed on the issue, he said up to a third of U.S. residents may have been affected by the attack, which could mean more than 110 million Americans.
The largest confirmed data breach occurred at Kaiser Foundation Health Plan and resulted in the impermissible disclosure of the personally identifiable information of 13.4 million individuals. Like many other healthcare organizations, Kaiser added tracking technologies to its websites and apps. When individuals visited the websites or used the apps, the technologies transferred data collected during those visits to third parties such as Microsoft (Bing), Google, and X (Twitter). The HHS’ Office for Civil Rights confirmed in guidance released in December 2022 – and updated in March 2023 – that if these tools collect personally identifiable health information and transmit that data to third parties who have not signed a business associate agreement, it is a HIPAA breach.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
The second largest breach of the month also occurred at a health plan. Group Health Cooperative of South Central Wisconsin fell victim to a ransomware attack involving the theft of the PHI of 533,809 individuals. Several cybercriminal groups have dispensed with ransomware and instead concentrate on breaching networks, stealing data, and demanding payment to prevent the stolen data from being leaked or sold, as was the case with the attacks on Otolaryngology Associates and Optometric Physicians of Middle Tennessee.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Breach |
| Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 | Impermissible disclosure of PHI – Website tracking technologies |
| Group Health Cooperative of South Central Wisconsin | WI | Health Plan | 533,809 | Ransomware attack – Data theft confirmed |
| Otolaryngology Associates, LLC | IN | Healthcare Provider | 316,802 | Hacking incident involving theft of PHI and extortion |
| Knowles Smith & Associates, d/b/a Village Family Dental | NC | Healthcare Provider | 240,214 | Hacked network server – Data theft possible |
| LivaNova USA, Inc. | TX | Business Associate | 180,000 | Ransomware attack (LockBit) – Data theft confirmed |
| OrthoConnecticut PLLC | CT | Healthcare Provider | 118,141 | Hacked network server – Data theft possible |
| Inland Physicians Billing Services | CA | Healthcare Clearing House | 77,434 | Hacked network server – No information available |
| Bluebonnet Trails Community Services | TX | Healthcare Provider | 76,165 | Unauthorized access to email accounts – Data theft possible |
| Gaia Software, LLC | CO | Business Associate | 56,676 | Hacked network server – No information available |
| Bridgeway Center, Inc. | FL | Healthcare Provider | 36,353 | Hacked network server – Data theft possible |
| The Prudential Insurance Company of America | NJ | Health Plan | 36,092 | Ransomware attack (Blackcat) – Data theft confirmed |
| Blackstone Valley Community Health Care | RI | Healthcare Provider | 34,518 | Hacked network server – Data theft possible |
| Politzer and Durocher, PLC d/b/a Optometric Physicians of Middle Tennessee | TN | Healthcare Provider | 29,000 | Hacking incident involving theft of PHI and extortion (BianLian) |
| Moffitt Cancer Center and Research Institute | FL | Healthcare Provider | 26,577 | Hacked network server at an unnamed business associate – Data theft confirmed |
| University of Tennessee Health Science Center | TN | Healthcare Provider | 19,353 | Hacked network server at business associate (KMJ Health Solutions) – Data theft confirmed |
| Aspire Health Alliance | MA | Healthcare Provider | 17,490 | Hacked network server – Data theft confirmed |
| Cattaraugus-Allegany Board of Cooperative Education Services | NY | Business Associate | 15,203 | Hacked network server – Data theft possible |
| Bay Oral Surgery & Implant Center | WI | Healthcare Provider | 13,055 | Unauthorized access to email account – Data theft possible |
| Somerset Dental Las Vegas | NV | Healthcare Provider | 11,321 | Hacked network server – Data theft possible |
Data Breach Causes and Location of Compromised PHI
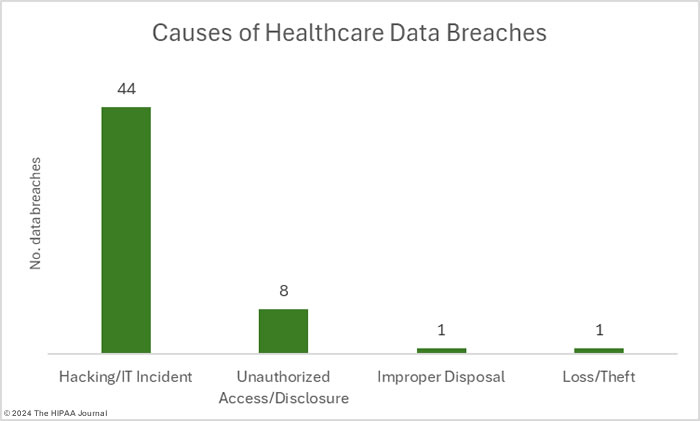
Hacking and other IT incidents were the main cause of healthcare data breaches in April, accounting for 84.5% of the month’s data breaches. In terms of breached records, hacks and ransomware attacks usually account for the bulk of breached records; however, in April, unauthorized disclosures affected the most people due to the massive breach at Kaiser. The protected health information of 1,919,637 individuals was exposed or stolen in hacking and other IT incidents in April, which is 12.5% of the month’s breached records. The average breach size was 43,628 records and the median breach size was 6,812 records, both of which are up month-over-month from an average of 38,402 records (+13.6%) and a median of 3,144 records (+53.8%).
There were 8 unauthorized access/disclosure incidents reported in April involving 87.5% of the month’s breached records. Across those data breaches, the protected health information of 13,428,243 individuals was accessed without authorization or was impermissibly disclosed. The average breach size was 1,678,530 records, a month-over-month increase of 50,442.9%, and the median breach size was 4,550 records, an increase of 132.6%.
While the loss and theft of paper records and electronic devices containing PHI used to account for the majority of data breaches, these incidents are now relatively rare. There were no reported thefts in April, one loss incident involving 755 paper records, and one improper disposal incident involving 568 paper records.
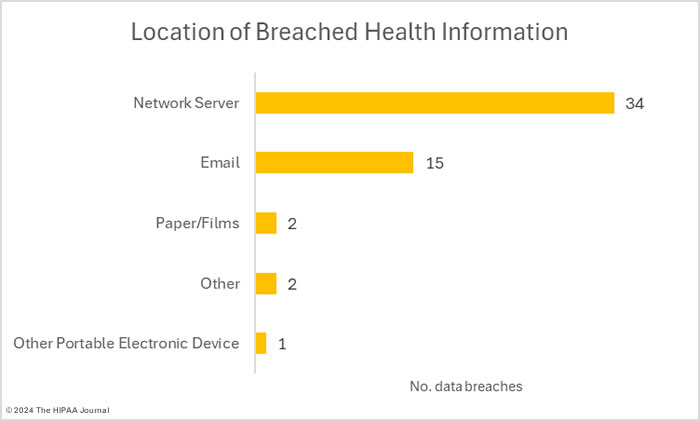
The most common location of breached protected health information was network servers. The next most common location was email accounts, breaches of which could be reduced if phishing-resistant multi-factor authentication is implemented. More than 133,000 records were compromised in email breaches in April.
Where did the Data Breaches Occur?
The HIPAA Breach Notification Rule requires data breaches to be reported to OCR and notifications to be issued to the affected individuals. When a data breach occurs at a business associate of a covered entity, the business associate must notify each of the affected covered entities and it is ultimately the responsibility of each covered entity to ensure that OCR and the affected individuals are notified. As OCR recently confirmed in its FAQs about the Change Healthcare ransomware attack, a covered entity may delegate the responsibility of providing individual notices to the business associate, and while this is common, some covered entities prefer to issue notifications themselves.
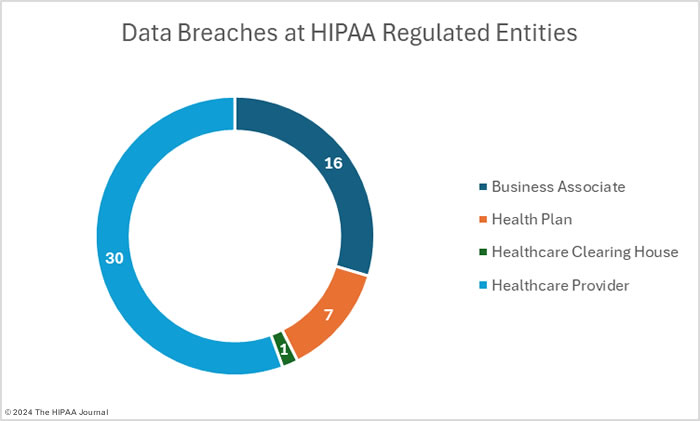
A consequence of that is that business associate data breaches are not always apparent on the OCR data breach portal. In April, the portal shows 34 breaches at healthcare providers (1,012,114 affected individuals), 12 breaches at business associates (1.919,637 affected individuals), 7 breaches at health plans (13,985,180 affected individuals), and one breach at a healthcare clearinghouse (77,434 affected individuals). The charts below show where the breaches occurred rather than the entity that reported them.
Geographical Distribution of Healthcare Data Breaches
Data breaches were reported by HIPAA-regulated entities in 26 U.S. states in April, with California the worst affected state in terms of the number of breaches and the number of breached records. California had 7 breaches that affected 13,502,632 individuals – 88% of the individuals affected by April data breaches. There were 5 breaches at HIPAA-regulated entities in Washington, involving the PHI of at least 15,489 individuals. That number is likely to grow considerably, as two of the breaches were reported to OCR as involving 500 and 501 records because the total number of affected individuals has yet to be determined. There were 4 breaches in Tennessee involving the records of at least 49,404 individuals. One of those breaches is still being investigated, so the total is likely to increase. While Wisconsin only suffered two breaches, it was the second worst affected state in terms of breached records, with 546,864 records breached.
| State | Breaches |
| California | 7 |
| Washington | 5 |
| Tennessee | 4 |
| Florida, New Jersey, New York, North Carolina, & Pennsylvania | 3 |
| Illinois, Maryland, Ohio, Texas & Wisconsin | 2 |
| Alabama, Arizona, Colorado, Connecticut, Georgia, Idaho, Indiana, Kentucky, Massachusetts, Montana, Nevada, New Hampshire & Rhode Island | 1 |
HIPAA Enforcement Activity in April 2024
In 2019, OCR launched a HIPAA Right of Access enforcement initiative which continues to be an enforcement priority. In April, OCR resolved its 48th HIPAA Right of Access case under this initiative with a $100,000 civil monetary penalty imposed on the New Jersey nursing care provider Essex Residential Care, which does business as Hackensack Meridian Health, West Caldwell Care Center. Most cases under this initiative are settled with OCR; however, West Caldwell Care Center chose not to settle. West Caldwell Care Center admitted to the HIPAA Right of Access violation but disagreed with OCR’s determination and penalty amount. West Caldwell Care Center argued that imposing a civil monetary penalty “would be arbitrary and capricious and would violate the Administrative Procedure Act (APA). OCR disagreed and offered the opportunity to take the case to an Administrative Law Judge; however, on advice from its legal counsel, West Caldwell Care Center chose to waive that right and agreed to pay the penalty.
HIPAA Compliance Audits to Commence This Year
OCR Director, Melanie Fontes Rainer, has confirmed that OCR has resurrected its HIPAA audit program and audits will start to be conducted at some point in 2024. Earlier this year, OCR sent a questionnaire to HIPAA-regulated entities audited in the last round of HIPAA audits in 2016/2017 and sought feedback to improve OCR’s audit protocol. OCR is now finalizing the new audit protocol and Fontes Rainer said OCR will be conducting proactive audits this year focusing on HIPAA Security Rule compliance. OCR launched an enforcement initiative targeting the risk analysis provision of the HIPAA Security Rule in 2023, as poor risk analysis practices are frequently identified in OCR’s data breach investigations and are a significant factor contributing to data breaches. Risk analyses and risk management practices will be scrutinized in the upcoming 2024 HIPAA audits.
FTC Issues Final Rule Updating Health Breach Notification Rule
HIPAA-regulated entities are required to comply with the HIPAA Breach Notification Rule and must issue notifications in the event of a data breach. Breaches of health data at non-HIPAA-regulated entities may require notifications under the Federal Trade Commission’s (FTC) Health Breach Notification Rule. The FTC felt an update to its Health Breach Notification Rule was necessary due to the increasing number of companies collecting health data. On April 26, 2024, the FTC issued a final rule updating the Health Breach Notification Rule with new definitions and clarifications. Definitions have been broadened to include health apps and other technologies not covered by HIPAA. As is the case with the HIPAA Breach Notification Rule, notifications must be issued without undue delay and no later than 60 days from the discovery of a data breach.