April 2025 Healthcare Data Breach Report
April saw a 17.9% month-over-month increase in healthcare data breaches, with 66 data breaches of 500 or more records reported to the HHS’ Office for Civil Rights (OCR). Last month, it looked like data breach numbers were starting to reduce; however, April’s figures are well above the 12-month average of 57 data breaches per month, with breaches reported in similar numbers to April 2024.


There’s further bad news, as April saw a massive increase in the number of individuals affected by healthcare data breaches, which increased by 371% month-over-month from 2.7 million in March to 12.9 million in April, largely due to two massive data breaches at Yale New Haven Health System and Blue Shield of California, which combined affected more than 10.26 million individuals.
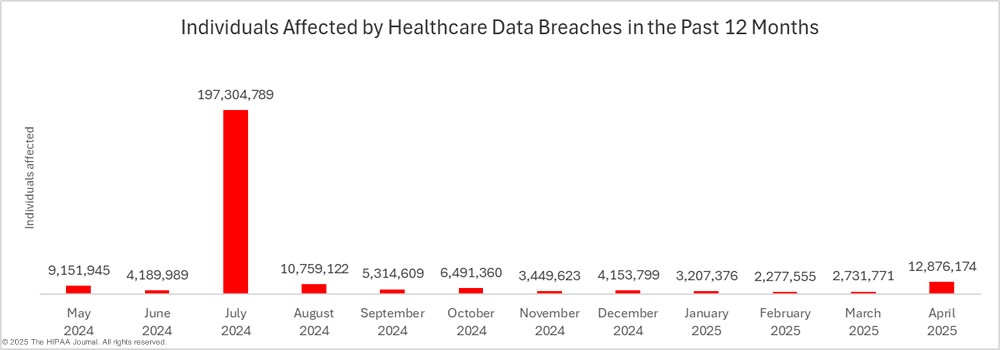
Excluding the massive data breach at Change Healthcare as an outlier, over the past 12 months, an average of 5,992,343 individuals have been affected by large healthcare data breaches each month. April’s total is more than twice that number, although well below the 17 million individuals affected by healthcare data breaches in April 2024.

Biggest Healthcare Data Breaches in April 2025
In April, 27 data breaches of 10,000 or more records were reported to OCR, including 11 data breaches of 100,000 or more records. All but 5 of the 10,000+ record data breaches were hacking/IT incidents, with the remaining four being unauthorized access/disclosure incidents.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
The hacking incident at Yale New Haven Health System stands out due to the scale of the data breach. With more than 5.5 million individuals affected, this was the largest healthcare data breach of the year to date, taking that unenviable record from Blue Shield of California, which announced its 4.7 million-record data breach just a few days earlier. Blue Shield of California discovered that Google Analytics code had been added to its websites but had been misconfigured, which meant visitor data was sent to Google’s advertising product, Google Ads, and was likely used to serve individuals with personalized ads. The code was active for almost 3 years, having first been installed in April 2021.
Other notable data breaches were announced in April, including one at Ascension Health, which discovered protected health information had been inadvertently shared with a former business partner that experienced a data breach exposing the protected health information of more than 437,000 patients. Gilead Sciences reported a breach at a mailing vendor used by one of its business associates. The mailing vendor sent out 1095-C tax forms, however, an 18-digit code on the front of the envelope included each recipient’s Social Security number.
Two large data breaches were reported in April that occurred way back in 2023, a ransomware attack on the City of Long Beach and a cyberattack on Dameron Hospital in California. Both incidents involved data theft, which gave the threat actors behind those incidents ample time to misuse the data before the victims of those breaches were made aware that their data had been stolen.
In April, 18 large data breaches were reported that involved protected health information stored in email accounts. One of those email breaches involved a single compromised email account that contained the protected health information of 357,265 individuals. Given how common email breaches are, it is important to implement data retention policies that limit the amount of patient data stored in email accounts.
We have also started to see breach reports submitted by healthcare providers and health plans affected by large data breaches at the debt collection agency Nationwide Recovery Service and Oracle Health/Cerner. These are likely to continue to be reported by affected HIPAA-regulated entities over the next few weeks.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Type of Breach | |
| Yale New Haven Health System | CT | Healthcare Provider | 5,556,702 | Hacking/IT Incident | Hacking incident – Data theft confirmed |
| Blue Shield of California | CA | Business Associate | 4,700,000 | Unauthorized Access/Disclosure | Tracking code on websites allowed PHI sharing with the Google Ads platform. |
| Ascension Health | MO | Healthcare Provider | 437,329 | Hacking/IT Incident | Inadvertent disclosure of PHI to a former business partner, which was stolen from the business partner in a hacking incident |
| Onsite Mammography | MA | Business Associate | 357,265 | Hacking/IT Incident | Unauthorized access to an employee’s email account |
| Union Health System, Inc. | IN | Healthcare Provider | 262,831 | Hacking/IT Incident | PHI stolen in a hacking incident at business associate Oracle Health/Cerner |
| The City of Long Beach, CA | CA | Healthcare Provider | 258,191 | Hacking/IT Incident | 2023 hacking incident – Data theft confirmed |
| Dameron Hospital | CA | Healthcare Provider | 210,706 | Hacking/IT Incident | 2023 hacking incident – Data theft confirmed |
| Central Texas Pediatric Orthopedics | TX | Healthcare Provider | 140,000 | Hacking/IT Incident | Hacking Incident – Qilin ransomware group claimed responsibility and said data stolen in the attack |
| Alabama Ophthalmology Associates | AL | Healthcare Provider | 131,576 | Hacking/IT Incident | Hacking incident |
| Endue Software | ME | Business Associate | 118,028 | Hacking/IT Incident | Hacking incident – Data theft confirmed |
| Bell Ambulance, Inc. | WI | Healthcare Provider | 114,000 | Hacking/IT Incident | Hacking incident |
| Alternate Solutions Health Network, LLC | OH | Healthcare Provider | 93,589 | Hacking/IT Incident | Unauthorized access to an employee’s email account |
| Whitman County Public Hospital District No. 3 | WA | Healthcare Provider | 63,453 | Hacking/IT Incident | Hacking incident |
| Horizon Behavioral Health | VA | Healthcare Provider | 49,822 | Hacking/IT Incident | Ransomware attack – Data theft confirmed |
| Benefits Partner, LLC dba Salus Group | MI | Business Associate | 40,177 | Hacking/IT Incident | Unauthorized access to an employee’s email account (Phishing) |
| Kelly & Associates Insurance Group, Inc. | MD | Business Associate | 32,234* | Hacking/IT Incident | Hacking incident affecting multiple clients |
| Rheumatology Associates of Baltimore | MD | Healthcare Provider | 28,968 | Unauthorized Access/Disclosure | Data breach at business associate (Endue Software) – Data theft confirmed |
| Gardner Health Services | CA | Healthcare Provider | 26,000 | Unauthorized Access/Disclosure | Hacking incident (Cl0p ransomware group) – Data theft confirmed |
| Orthopaedic Specialists of Connecticut | CT | Healthcare Provider | 22,541 | Hacking/IT Incident | Hacking incident |
| Drug and Alcohol Treatment Services, Inc. | PA | Healthcare Provider | 22,215 | Hacking/IT Incident | Hacking incident |
| Cabot Medical Care | AR | Healthcare Provider | 21,467 | Hacking/IT Incident | Hacking incident |
| Northeast Georgia Health System | GA | Healthcare Provider | 21,000 | Hacking/IT Incident | Hacking incident at business associate (Nationwide Recovery Service) – Data theft confirmed |
| True Dental Care for Kids and Adults LLC | PA | Healthcare Provider | 17,640 | Hacking/IT Incident | Ransomware attack – Data theft confirmed |
| Hamilton County Government | TN | Healthcare Provider | 14,081 | Hacking/IT Incident | Hacking incident at business associate (Nationwide Recovery Service) – Data theft confirmed |
| Family Christian Health Center | IL | Healthcare Provider | 12,500 | Hacking/IT Incident | Ransomware attack – Data theft confirmed |
| Gilead Sciences, Inc. | CA | Health Plan | 12,224 | Unauthorized Access/Disclosure | Mailing incident involving mailing vendor (Billing Documents Specialists) – Shipping labels contained Social Security numbers. |
| Blue Cross and Blue Shield of Texas | IL | Health Plan | 12,086 | Unauthorized Access/Disclosure | Misconfigured member portal exposed plan member data over the Internet |
*The number of individuals affected by the data breach at Kelly & Associates has been increased to 413,032; however, the OCR breach portal is still showing the total as 32,234 affected individuals.
The HIPAA Breach Notification Rule requires data breaches affecting 500 or more individuals to be reported to the HHS Secretary within 60 days of discovery, which can mean the breach report has to be submitted before the investigation and file review have been completed. In such cases, an estimate of the number of affected individuals should be provided and amended when the investigation is completed. A placeholder figure tends to be provided of 500 or 501 affected individuals. In April, at least 6 HIPAA-regulated entities reported breaches with placeholder figures. These data breaches could increase the monthly number of affected individuals considerably when the file reviews are concluded.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Type of Breach |
| Berkeley Research Group, LLC | CA | Business Associate | 500 | Hacking/IT Incident |
| HEALTH AND WELLNESS OF TEXAS | TX | Healthcare Provider | 500 | Unauthorized Access/Disclosure |
| Prestonwood Baptist Church, Inc. | TX | Health Plan | 501 | Hacking/IT Incident |
| Brainard Surgery Center LLC | OH | Healthcare Provider | 501 | Hacking/IT Incident |
| Friendship House, Inc. | NE | Healthcare Provider | 501 | Hacking/IT Incident |
| Loretto Hospital | IL | Healthcare Provider | 501 | Hacking/IT Incident |
Causes of April 2025 Healthcare Data Breaches
For several years, hacking and other types of IT incidents have dominated the breach reports, and April was no different, with 47 hacking-related data breaches reported to OCR, which equates to 71% of the month’s total number of data breaches. Across those incidents, the electronic protected health information of 12,752,390 individuals was exposed or stolen – 99.03% of the month’s affected individuals. The average breach size was 271,327 records, and the median breach size was 6,270 records.

In April, 19 unauthorized access/disclosure incidents were reported to OCR involving the protected health information of 123,784 individuals – 0.96% of the month’s affected individuals. The average breach size was 6,515 records, and the median breach size was 3,561 records. Theft, loss, and improper disposal incidents are typically reported in low numbers, and in April, there were none of these types of breaches.
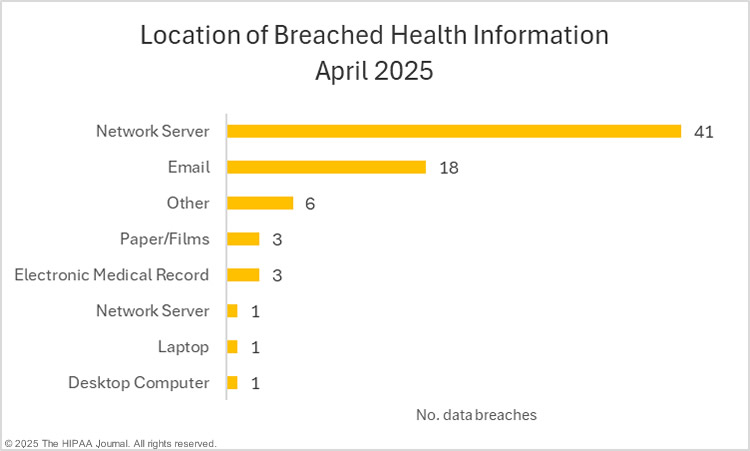
Given the high number of hacking incidents, it is unsurprising that a majority of the month’s data breaches involved electronic protected health information stored on network servers. Email accounts are also commonly compromised, which is why it is important to implement multi-factor authentication, and ideally, phishing-resistant MFA on all email accounts.
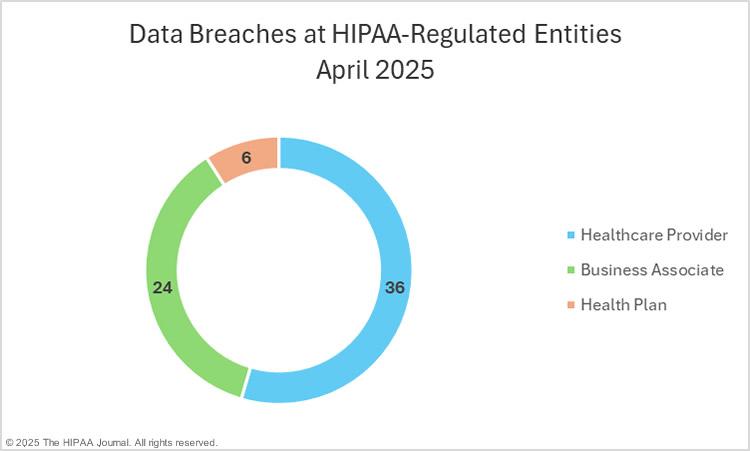
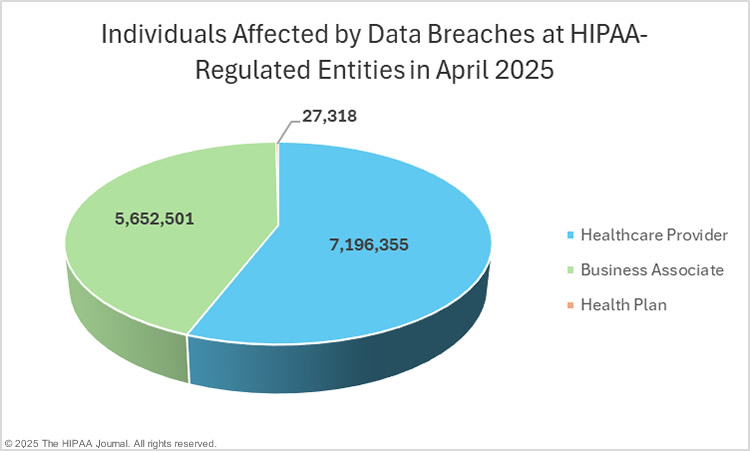
Data Breaches at HIPAA-Regulated Entities
Healthcare providers were the worst-affected HIPAA-covered entities in April, with 47 large data breaches reported and 7,571,909 affected individuals. Business associates reported 12 breaches, affecting 5,264,723 individuals, and 7 data breaches were reported by health plans, affecting 39,542 individuals.
The reporting entity is not necessarily the entity that suffered the data breach, as HIPAA-covered entities frequently report data breaches that occur at their business associates. For instance, recently, Oracle Health/Cerner had a vulnerability exploited on its legacy servers, and made it clear that it is the responsibility of each affected covered entity to report the data breach.
The charts below are based on where the breach occurred, rather than the reporting entity, to better reflect data breaches at business associates. Taking these reporting discrepancies into consideration, the average data breach at a healthcare provider affected 199,899 individuals (median: 4,835), business associate data breaches affected an average of 235,521 individuals (median: 7,002), and data breaches at health plans affected an average of 4,553 individuals (median: 3,404).
Geographical Distribution of Healthcare Data Breaches
HIPAA-regulated entities in 29 U.S. states reported large data breaches in April. California was the worst-affected state with 11 data breaches, followed by Illinois with 8 breaches, and Ohio, Tennessee, and Texas, which each had 4 data breaches.
While only experiencing two data breaches, Connecticut was the worst-affected state in terms of affected individuals, with 5,579,243 individuals having their protected health information exposed or impermissibly disclosed. California was in close second with 5,217,690 individuals affected by its 11 data breaches, with Missouri in third place with 437,968 individuals affected by its two data breaches.
| State | Data Breaches |
| California | 11 |
| Illinois | 8 |
| Ohio, Tennessee & Texas | 4 |
| Florida | 3 |
| Arkansas, Connecticut, Georgia, Indiana, Maryland, Missouri, Pennsylvania, Virginia & Wisconsin | 2 |
| Alabama, Arizona, Kansas, Louisiana, Maine, Massachusetts, Michigan, Minnesota, Nebraska, New York, North Dakota, Oregon, Washington & West Virginia | 1 |
HIPAA Enforcement in April 2025
April was a busy month for HIPAA enforcement, with four HIPAA violation cases settled with OCR. OCR is continuing with its HIPAA risk analysis enforcement initiative, and all four of the settlements resolved alleged risk analysis failures.
PIH Health, Inc., a California health care network, was investigated by OCR over a major phishing-related data breach. Hackers gained access to the email accounts of 45 employees in June 2019, resulting in the exposure of the protected health information of 189,763 individuals. OCR determined that PIH Health had not conducted a comprehensive and accurate risk analysis, resulting in a preventable unauthorized disclosure of the electronic protected health information of 189,763 individuals. Further, it took PIH Health 7 months to issue breach notifications, in violation of the HIPAA Breach Notification Rule. The case was settled, and PIH Health paid a $600,000 financial penalty and agreed to adopt a comprehensive corrective action plan.
Northeast Radiology, the operator of medical imaging facilities in New York and Connecticut, was investigated by OCR over a March 2020 hacking incident that affected 298,532 individuals. Hackers exploited vulnerabilities in its PACS and gained access to sensitive patient data and medical images. Those vulnerabilities were exploited by a threat actor who accessed its PACS for 9 months between April 2019 and January 2020. OCR determined that Northeast Radiology had not conducted a HIPAA-compliant risk analysis. The case was resolved with a $350,000 settlement and a comprehensive corrective action plan.
Guam Memorial Hospital Authority was investigated after OCR received a complaint about a December 2018 ransomware attack. While investigating that complaint, another complaint was received about unauthorized access to patient information by former employees. OCR confirmed that up to 5,000 patients had their electronic protected health information accessed in the ransomware attack, and two former employees had accessed patient data after their employment ended. Neither breach was reported to OCR. OCR determined there had been a failure to conduct a HIPAA-compliant risk analysis, and the case was settled with a $25,000 financial penalty and a corrective action plan, which includes the requirement to notify OCR and the affected individuals about both data breaches.
Comprehensive Neurology, a small neurology practice in New York City, was investigated over a 2020 data breach that affected 6,800 individuals and resulted in the exposure of names, clinical information, health insurance information, demographic information, Social Security numbers, driver’s license numbers, and state identification numbers. OCR determined that Comprehensive Neurology had failed to conduct a HIPAA-compliant risk analysis. The case was settled with a $25,000 financial penalty and a corrective action plan.



