December 2024 Healthcare Data Breach Report
It was a relatively quiet end to the year in terms of healthcare data breaches, with only 46 data breaches of 500 or more healthcare records reported to the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) in December. The low December total meant that for only the second time since 2009, there was a year-over-year reduction in healthcare data breaches. The OCR data breach portal currently shows 721 reports of large data breaches in 2024, down 3.48% from 2023’s record-breaking total of 747 large healthcare data breaches.
December saw the third-lowest monthly breach total of 2024, with large data breaches falling by 34.3% month-over-month to the second-lowest December total in the past 5 years, with 33 fewer large data breaches than December 2023.
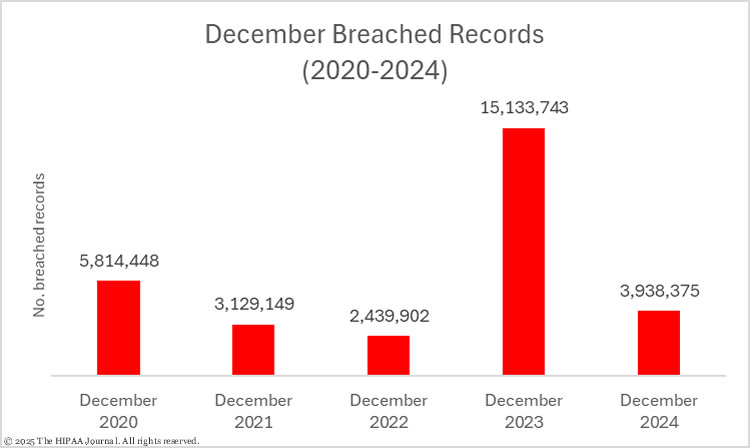
December was also a relatively good month in terms of breached healthcare records, with 3,938,375 healthcare records reported as exposed, impermissibly disclosed, or stolen – the second-lowest monthly total of 2024, although that does represent a 14.5% month-over-month increase in breached records.
Compared to the previous 5 years, December 2024 saw a return to a more typical number of breached records, down 74% from the unusually high number of breached records in December 2023. The good news ends there, however, as 2024 was the worst-ever year in terms of breached healthcare records, with a 9.96% increase from the record-breaking total in 2023. The OCR breach portal currently lists 185,043,568 breached records in 2024. That number will increase over the coming months as HIPAA-regulated entities finish their data breach investigations and report accurate figures. There are still many data breaches listed on the OCR breach portal with suspected placeholder figures of 500 or 501 affected individuals.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Biggest Healthcare Data Breaches in December 2024
While no data breaches of 1 million+ records were reported in December, one data breach came close, with 914,138 records compromised in a hacking incident at ConnectOnCall.com, a platform healthcare providers use to improve their after-hours call process and enhance patient communications. A major hacking incident was reported by Richmond University Medical Center, with hackers gaining access to systems containing the protected health information of 674,033 individuals, and large hacking incidents were also reported by River Region Cardiology (which has yet to publish a media notice or website substitute breach notice), the Center for Vein Restoration, Regional Care, and Tycon Medical Systems.
In total, 19 data breaches of 10,000 or more records were reported in December, the vast majority of which were hacking incidents and ransomware attacks; however, two data breaches in the list stand out as they involved neither. The third-largest data breach of the month was reported by Atrium Health and was due to the historic use of website tracking technologies that impermissibly transferred data to third parties such as Meta and Google. The breach potentially affected 585,959 patients.
The other non-hacking breach occurred at UT Southwestern Medical Center. Employees were found to be using an unauthorized calendar app to which patient data was added. The provider of the tool could access data in the app, and since the app was unauthorized there was no business associate agreement in place.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Business Associate Present |
| ConnectOnCall.com, LLC | DE | Business Associate | 914,138 | Hacking incident |
| Richmond University Medical Center | NY | Healthcare Provider | 674,033 | Hacking incident |
| Atrium Health | NC | Healthcare Provider | 585,959 | Website tracking tools disclosed PHI to third parties |
| River Region Cardiology | AL | Healthcare Provider | 500,000 | Hacking incident |
| Center for Vein Restoration | MD | Business Associate | 446,094 | Hacking incident |
| Regional Care, Inc. | NE | Healthcare Clearing House | 225,728 | Hacking incident |
| Tycon Medical Systems, Inc. | VA | Healthcare Provider | 112,847 | Hacking incident |
| Brockton Neighborhood Health Center | MA | Healthcare Provider | 97,488 | Ransomware attack (Interlock) – data theft confirmed |
| VisionPoint Eye Center, PLLC | IL | Healthcare Provider | 66,926 | Hacking incident |
| Dignity Health Lassen Medical Clinic | CA | Healthcare Provider | 65,482 | Hacking incident |
| UT Southwestern Medical Center | TX | Healthcare Provider | 43,048 | Employees used an unauthorized calendar management tool that exposed data to an unauthorized third party |
| SAG-AFTRA Health Plan | CA | Health Plan | 35,592 | Phishing attack – Single email account |
| Lexington Diagnostic Center | KY | Healthcare Provider | 29,819 | Hacking incident |
| Ott Cone & Redpath, P.A. | NC | Business Associate | 22,171 | Phishing attack – Single email account |
| In-Home Attendant Services Ltd. | TX | Healthcare Provider | 22,000 | Hacking incident |
| Rumpke Consolidated Companies, Inc. & Affiliates Benefits Plan | OH | Health Plan | 16,946 | Hacking incident – Data theft confirmed, extortion attempted |
| Lifetime Psychiatry, LLC | MO | Healthcare Provider | 16,926 | Hacked email account |
| PracticeSuite, Inc. | FL | Business Associate | 13,000 | Hacking incident |
| Alta Resources Corp. | WI | Health Plan | 12,162 | Ransomware attack |
In addition to the above data breaches, four breaches were reported to OCR as affecting 500 or 501 individuals. These figures are often used when the breach reporting deadline arrives, but the total number of affected individuals has not yet been determined. These could easily make the above list when the investigations conclude.
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Breach |
| Dragonfly Health | AZ | Business Associate | 501 | Hacking/IT Incident |
| Word & Brown Insurance Administrators, Inc. | CA | Business Associate | 501 | Hacking/IT Incident |
| Youth Eastside Services | WA | Healthcare Provider | 501 | Hacking/IT Incident |
| Kitsap Mental Health Services | WA | Healthcare Provider | 500 | Hacking/IT Incident |
Causes of December 2024 Healthcare Data Breaches
Hacking and other IT-related incidents continue to dominate the breach reports, as has been the case throughout 2024 and over the past few years. The nature of these incidents is not always disclosed by HIPAA-regulated entities such as if ransomware was used, even when ransomware gangs have announced that they have stolen data and added the data to their data leak sites. Several ransomware groups have dispensed with ransomware and now focus on data theft and extortion. Healthcare organizations can often recover their data from backups, and dispensing with file encryption makes attacks quieter and faster. Oftentimes, the threat of exposing stolen data is the main driver behind the decision to pay a ransom.
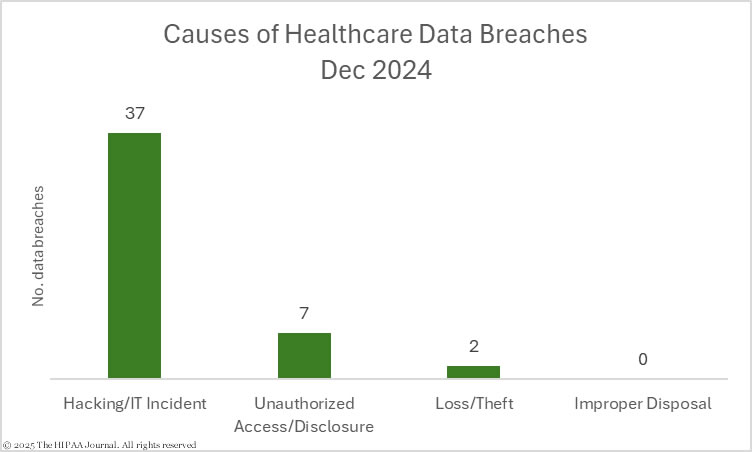
In December, hacking and other IT incidents accounted for 80.4% of the large data breaches (37 incidents) and 83.81% of the month’s breached records. The average size of a hacking incident in December was 89,212 records and the median breach size was 3,112 records. There were 7 unauthorized access/disclosure incidents involving 635,149 records, with an average breach size of 90,736 records and a median breach size of 1,317 records. The average breach size was skewed because 92.5% of those records were impermissibly disclosed in one data breach. Loss and theft incidents are now only reported in very low numbers, largely due to the migration to the cloud and the widespread use of encryption on portable electronic devices. Two loss incidents were reported involving a total of 2,375 records. There were no theft or improper disposal incidents.
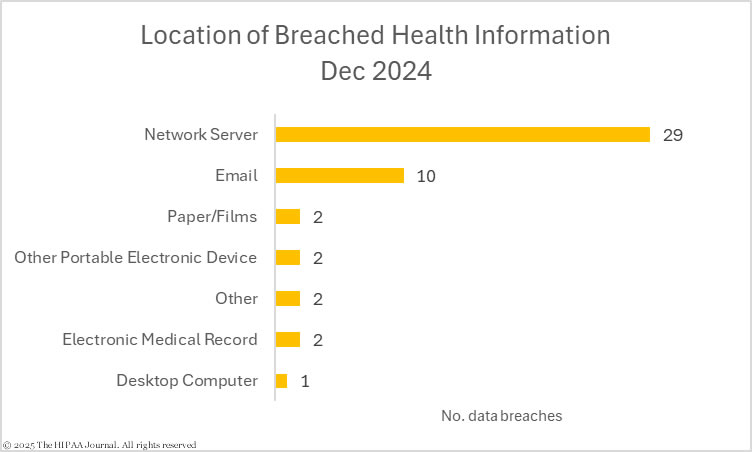
Network servers were the most common location of breached protected health information due to the number of hacking incidents; however, more than one-fifth of breaches involved data stored in email accounts, highlighting the need for strong password policies, multifactor authentication, and security awareness training for the workforce.
Where did the Data Breaches Occur?
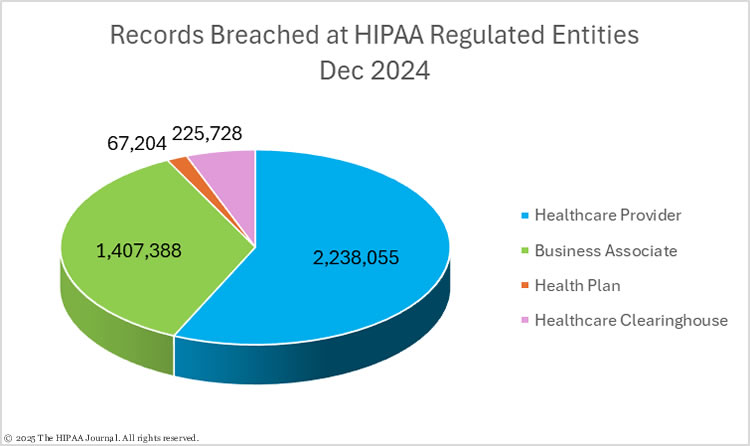
Healthcare providers reported 30 data breaches in December (2,243,060 records), 8 data breaches were reported by business associates (1,401,066 records), 7 data breaches were reported by health plans (68,521 records) and there was one data breach at a healthcare clearinghouse (225,728 records). When a data breach occurs at a business associate, the business associate must report the data breach to each affected covered entity, and the covered entity must decide who should send out individual notifications and notify OCR and the media. Some covered entities choose to report business associate breaches to OCR and issue their own notifications, while others delegate that responsibility to the business associate. If a business associate works with multiple covered entities, a combination of the two may occur.
That means data breaches at business associates are often underrepresented in data breach reports. The HIPAA Journal calculates where the breach occurred rather than the entity that reported the breach to ensure business associate data breaches are reported accurately. As you can see from the pie chart below, while 8 data breaches were reported by business associates, another 3 occurred at business associates but were reported by the affected covered entities. The pie charts below are based on the location of the breach rather than the reporting entity.
Geographical Distribution of Healthcare Data Breaches
In December, California was the worst-affected state with 5 reported data breaches, followed by Texas with 4 breaches, and Illinois, Massachusetts, Tennessee, and Washington which each had 3 data breaches.
| State | Breaches |
| California | 5 |
| Texas | 4 |
| Illinois, Massachusetts, Tennessee & Washington | 3 |
| Alabama, Florida, Missouri, Nebraska & North Carolina | 2 |
| Arizona, Connecticut, Delaware, Indiana, Kentucky, Maryland, Michigan, Nevada, New York, Ohio, Oklahoma, Utah, Virginia, Wisconsin & the District of Columbia | 1 |
Delaware topped the list for breached records, as while only one breach was reported by a Delaware-headquartered HIPAA-regulated entity, it was the largest data breach of the month. New York and Maryland also made the top five having only experienced one breach apiece.
| State | Individuals Affected |
| DE | 914,138 |
| NY | 674,033 |
| NC | 608,130 |
| AL | 500,776 |
| MD | 446,094 |
HIPAA Enforcement Activity in December 2024
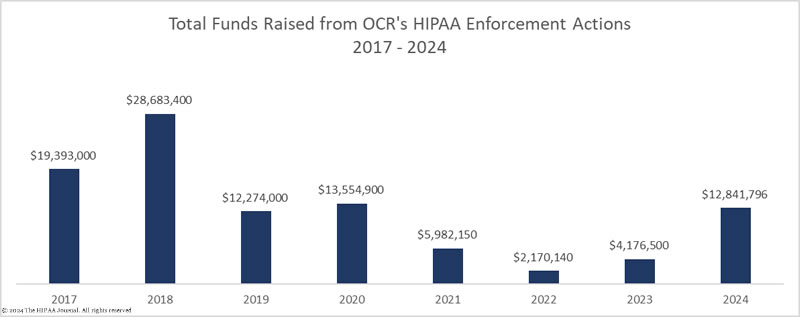
OCR closed out the year with 9 settlements with HIPAA-regulated entities in December to resolve alleged violations of the HIPAA Rules. In 2024, OCR closed 22 investigations of complaints and data breach investigations with settlements (15) and civil monetary penalties (7), collecting $12,841,796 in penalties, making it one of the business years of HIPAA enforcement to date.
Solara Medical Supplies
The biggest settlement of the month and the second largest penalty of 2024 was agreed upon with the direct-to-patient distributor of medical products for diabetes management, Solara Medical Supplies. Solara Medical Supplies agreed to pay a $3,000,000 penalty to resolve alleged violations of the HIPAA Security Rule and Breach Notification Rule. OCR identified noncompliance in the areas of risk analysis, risk management, and delayed notifications to the HHS, individuals, and the media, as well as the impermissible disclosure of the data of 114,007 and 1,531 individuals. The latter occurred when notifying individuals about the first breach.
Gulf Coast Pain Consultants, LLC d/b/a Clearway Pain Solutions Institute
Clearway Pain Solutions Institute agreed to settle its HIPAA violation case with OCR for $1,190,000. The Florida pain management practice failed to terminate the access rights of a former contractor when the contractor stopped working for the company. The contractor accessed health records on three occasions after stopping working for the company. OCR identified noncompliance with the HIPAA Security Rule in areas of risk analysis, reviews of records of activity in IT systems, and a lack of procedures for modifying workforce members’ access to patient data.
Children’s Hospital Colorado
Children’s Hospital Colorado was investigated over a 2017 phishing incident, although OCR took no action over the breach. The IT department had failed to reenable 2-factor authentication on the compromised account. Then, 3 years later another phishing incident was reported. In total, 14,210 records were compromised across the two incidents. While investigating the breach, OCR discovered that 6,666 members of the workforce, including 3,495 nursing students, had not been provided with HIPAA training. OCR determined there had been HIPAA violations in the areas of risk analysis, workforce Privacy Rule training, and the impermissible disclosure of PHI. The case was settled for $548,265.
USR Holdings
USR Holdings, a holding company that manages primary mental health and substance abuse treatment facilities in Florida, was investigated over unauthorized access to a database over 4 months, resulting in the deletion of protected health information from the database. OCR identified HIPAA violations in the areas of risk analysis, recording activity in information systems, procedures for creating and maintaining retrievable exact copies of ePHI, and there was an impermissible disclosure of the ePHI of 2,903 individuals. USR Holdings settled and paid a $337,750 penalty.
Inmediata Health Group
The Puerto Rican healthcare clearinghouse Inmediata Health Group had already settled alleged violations of the HIPAA Rules and state laws in a multistate action involving 32 states and Puerto Rico in 2023 and paid a $1.5 million penalty. In December, Inmediata settled alleged violations of the HIPAA Rules with OCR and paid a $250,000 penalty. The HIPAA violations were identified following a report of a breach of the protected health information of 1,565,338 that had been stored on an improperly secured server, resulting in the exposure of the data over the Internet. OCR identified HIPAA violations related to the risk analysis, monitoring and reviewing health information system activity, and the impermissible disclosure of the protected health information of 1,565,338 individuals.
Virtual Private Network Solutions
Virtual Private Network Solutions, a Virginia-based provider of data hosting and cloud services, was investigated over a reported breach of the protected health information of 6,400 individuals. The report was submitted on behalf of 12 covered entity clients and at least one other client was affected, exposing 17,468 records. OCR identified a failure to conduct a comprehensive and accurate risk analysis. The case was settled for $90,000.
Elgon Information Systems
Elgon Information Systems, a Massachusetts provider of electronic medical records and billing support services, was investigated over a breach of the protected health information of 31,248 individuals. A ransomware group accessed its network via open ports on its firewall, stole data, and encrypted files. OCR identified a failure to conduct a comprehensive and accurate risk analysis. Elgon Information Systems settled the alleged HIPAA violation and paid an $80,000 penalty.
South Broward Hospital District (Memorial Health System)
South Broward Hospital District, DBA Memorial Health System, was investigated over a complaint from a patient who had not been provided with his requested records, despite making multiple requests to the Florida health system. Memorial Health System maintained there was no HIPAA violation, as prior to those requests, the requested test results had been provided to the patient. OCR determined that there had been a HIPAA Right of Access violation, and while Memorial Health System requested a hearing with an Administrative Law Judge to fight its case, a settlement was negotiated, and a $60,000 penalty was paid.
Northeast Surgical Group
Northeast Surgical Group in Michigan was investigated over a ransomware-related data breach involving the protected health information of 15,298 patients, which was exfiltrated and encrypted in the attack. OCR investigated and determined that Northeast Surgical Group had failed to conduct a comprehensive and accurate risk analysis. The alleged HIPAA violation was settled, and Northeast Surgical Group paid a $10,000 penalty.
Enforcement Actions by State Attorneys General
There were also two enforcement actions announced by State Attorneys General in December, one by New York and one by Indiana.
HealthAlliance
HealthAlliance was investigated by the Office of the New York Attorney General over a breach of the personal and protected health information of 242,641 New Yorkers. HealthAlliance had been notified by a vendor, Citrix, about vulnerabilities in its NetScaler networking products. Patches were made available, but they could not be implemented due to technical problems. HealthAlliance worked to resolve the issues over the following 3 months but continued to use the vulnerable products. The vulnerabilities were found and exploited by hackers who stole patient data. While security failures were likely HIPAA violations, the New York Attorney General took action over the violations of New York Executive & General Business Law. The case was settled with a $1,500,000 penalty and a commitment by HealthAlliance to improve security. $850,000 of the penalty was suspended due to HealthAlliance’s financial position.
Westend Dental
The last penalty was one of the worst HIPAA violation cases The HIPAA Journal has seen. Westend Dental was investigated by the Indiana Attorney General over a complaint from a patient who had not been provided with their requested health records. The patient was told the records could not be provided due to a hacking incident, which had not been reported to OCR or the state. The investigation uncovered multiple violations of HIPAA and state law, and there was an attempted cover-up of a ransomware attack and data breach.
The Indiana Attorney General identified multiple violations of the HIPAA Security Rule, impermissible disclosures of protected health information, the failure to post a notice of privacy practices, the failure to comply with the requirements of the HIPAA Breach Notification Rule and the Indiana Disclosure of Security Breach Act, and violations of the Indiana Deceptive Consumer Sales Act. The number of affected individuals is unknown as the ransomware attack was not remediated or investigated. Westend Dental maintained, until evidence was provided to the contrary, that data had been accidentally wiped due to a drive formatting error. Westend Dental agreed to a consent order involving a $350,000 fine and will implement a long list of measures to ensure HIPAA compliance.
About This Report
The data for this report was obtained from the HHS’ Office for Civil Rights on January 20, 2025, and has been supplemented with information from HIPAA Journal breach reporting and other media sources. HIPAA-regulated entities may amend their breach reports after they have been submitted to OCR when more information is known about the data breach, such as the number of affected individuals. The HIPAA Journal does not update past monthly data breach reports to reflect any changes that come to light after publication; however, they will be reflected in future monthly breach reports and on our healthcare data breach statistics page, which is updated regularly.