Lessons from 2024 Healthcare Data Breaches
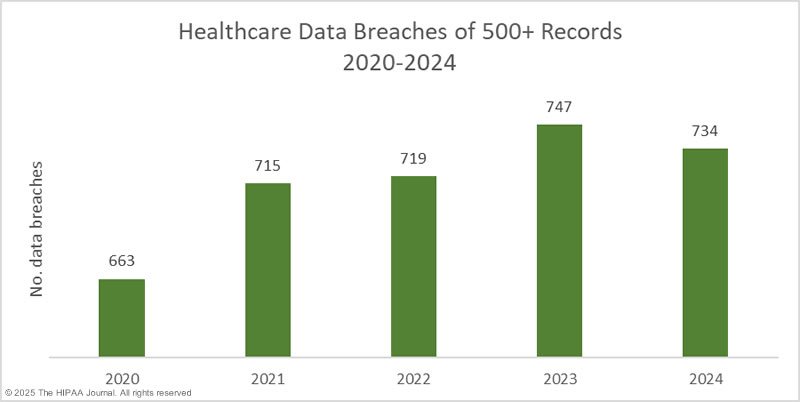
For the fourth consecutive year, more than 700 data breaches of 500 or more healthcare records were reported to the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR). At present, it looks like there has finally been a fall in healthcare data breaches, although OCR has yet to finalize its data for 2024, so the total may still increase. In order to see a more significant reduction in data breaches, healthcare organizations will need to invest more time and effort into cybersecurity.
As it currently stands, 2024 was a record-breaking year in terms of breached healthcare records. It has already been confirmed that the personal and healthcare data of more than 278 million individuals was exposed, stolen, or impermissibly disclosed in 2024, more than any other year to date, and there are still many investigations of 2024 data breaches that are yet to conclude. OCR’s data breach portal currently lists 66 data breaches that have been reported as affecting 500 or 501 individuals – commonly used placeholder figures when the breach reporting deadline is reached before the investigation and file review have concluded. On January 18, 2023, the total stood at 133 million breached records for the year, to which a further 35 million records have since been added.
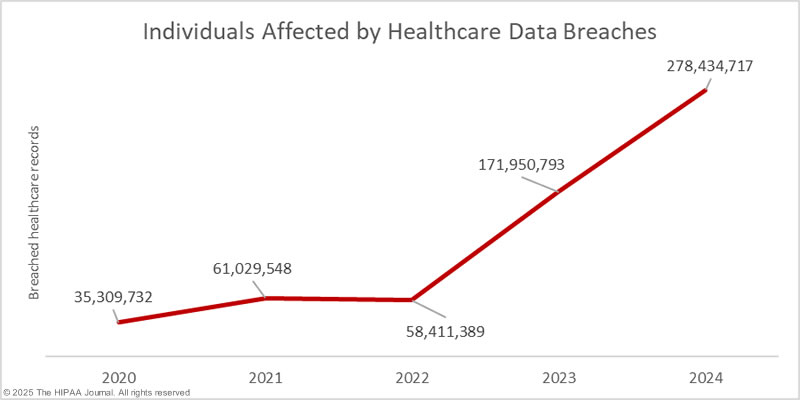
Data breach severity has been increasing, with 2024 seeing some of the largest-ever data breaches, including the data breach at Change Healthcare, which involved an estimated 190,000,000 healthcare records. The file review from that February 2024 attack has not concluded, so the total could grow further still. Last year, the fourth-largest healthcare data breach was also announced by Kaiser Foundation Health Plan, potentially involving the protected health information of 13,400,000 individuals. If some good news can be drawn from last year’s breached record data, it is that only 13 data breaches of 1 million or more records were reported, down from 34 in 2023.
The high number of data breaches over the past four years suggests the Privacy and Security Rules of the Health Insurance Portability and Accountability Act (HIPAA) are not effective, or non-compliance with those Rules is commonplace. The reality appears to be a combination of the two, which I will explore later in this article. First, let’s take a look at some of the biggest healthcare data breaches of 2024.
The Biggest Healthcare Data Breaches of 2024
| Name of Covered Entity | State | Covered Entity Type | Individuals Affected | Cause of Data Breach |
| Change Healthcare, Inc. | MN | Business Associate | 190,000,000 | Ransomware attack (BlackCat) – Data theft confirmed |
| Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 | Website tracking tools disclosed PHI to third parties |
| Ascension Health | MO | Healthcare Provider | 5,599,699 | Ransomware attack (Black Basta) – Data theft confirmed |
| HealthEquity, Inc. | UT | Business Associate | 4,300,000 | Hacking incident using a business partner’s compromised credentials |
| Concentra Health Services, Inc. | TX | Healthcare Provider | 3,998,163 | Hacking incident at a business associate (PJ&A) |
| Centers for Medicare & Medicaid Services | MD | Health Plan | 3,112,815 | Hacking incident at business associate (Wisconsin Physicians Service Insurance Corporation)- Clop Group exploited MOVEit Transfer vulnerability |
| Acadian Ambulance Service, Inc. | LA | Healthcare Provider | 2,896,985 | Hacking incident (Daixin Team – Data theft confirmed |
| A&A Services d/b/a Sav-Rx | NE | Business Associate | 2,812,336 | Ransomware attack |
| WebTPA Employer Services, LLC (“WebTPA”) | TX | Business Associate | 2,518,533 | Hacking incident |
| INTEGRIS Health | OK | Healthcare Provider | 2,385,646 | Hacking incident (Hunters International) data theft confirmed |
| Medical Management Resource Group, L.L.C. | AZ | Business Associate | 2,350,236 | Hacking incident |
| Summit Pathology and Summit Pathology Laboratories, Inc. | CO | Healthcare Provider | 1,813,538 | Ransomware attack (Medusa) data theft confirmed |
You can read more about these incidents in our post – The Biggest Healthcare Data Breaches of 2024, and up-to-date breach figures can be found on our Healthcare Data Breach Statistics page.
Lessons from 2024 Healthcare Data Breaches
2024 has clearly shown that even the biggest healthcare organizations can fall victim to hugely damaging cyberattacks and data breaches. In 2024, Change Healthcare and Ascension Health suffered ransomware attacks involving the theft of millions of patient records, while a privacy breach occurred at Kaiser Foundation involving the impermissible disclosure of the protected health information of up to 13.4 million plan members.
Large healthcare organizations have deep enough pockets to implement robust cybersecurity defenses; however, errors can easily be made that open the door to hackers. In the case of Change Healthcare, multifactor authentication had not been implemented on a Citrix server, which meant compromised credentials could be used to access its network. From there, a ransomware affiliate moved laterally and exfiltrated a huge volume of patient data and the outage lasted for weeks. The attack is still having an impact not just on Change Healthcare, but on providers and patients across the country.
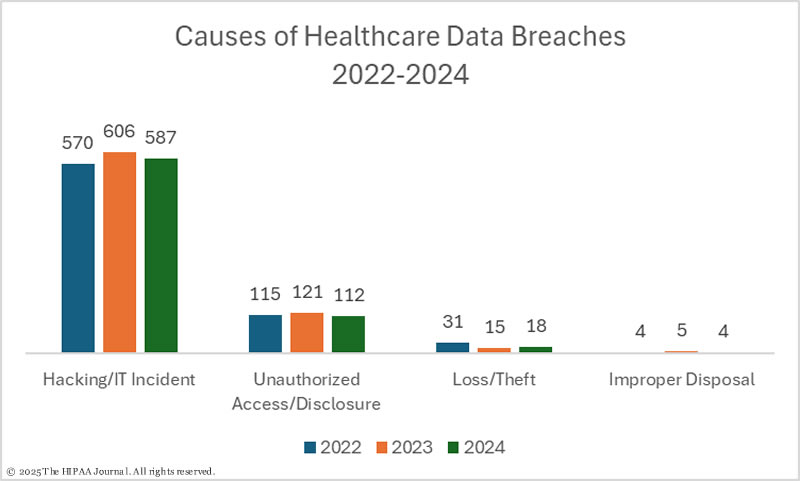
Hacking incidents accounted for the majority of healthcare data breaches last year. These incidents are costly to mitigate and can cause outages that last for weeks. They often result in the theft of huge numbers of patient records, and the disruption caused has an impact on care delivery. Essential care is delayed, and various studies have shown poorer patient outcomes following a cyberattack, an increase in mortality rate, and that cyberattacks can have far-reaching effects. Attacks on business associates can affect healthcare providers across the country, and attacks on hospitals often affect entire communities, not just patients of the hospital suffering the cyberattack.
There are lessons to be learned from 2024 data breaches but little appears to have changed over the past few years. Little has been achieved in addressing the root causes of these data breaches, and there is little to suggest that much will change in the coming 12 months. Cyberattacks, and ransomware attacks in particular, have a major impact on healthcare services and are clearly a patient safety issue and even a matter of national security.
The problem cannot simply be addressed by further regulation, although that would certainly make a difference. Congress needs to make sure that funds are available to help healthcare organizations make the necessary security upgrades, education about cybersecurity must be improved, guidance is required to help healthcare organizations address security issues and comply with security standards, the unnecessary administrative burden on healthcare organizations needs to be reduced, there needs to be more effective enforcement of HIPAA compliance with higher penalties for serious violations, and efforts need to be increased to tackle the cybercriminal groups that are currently running riot.
Single Points of Failure Need to be Identified and Addressed
One clear lesson from 2024 is that supply chains are only as strong as the weakest link. When that weak link is a business associate used by many healthcare organizations, a disaster such as a cyberattack can have a catastrophic impact, as demonstrated by the ransomware attack on Change Healthcare. Change Healthcare is relied upon by healthcare providers, health insurers, and patients, although the latter were largely oblivious to even the existence of Change Healthcare until the outage prevented them from getting the care they needed.
The attack on Change Healthcare highlighted the risks of single points of failure in the healthcare supply chain, a disaster at which – be that a cyberattack or a natural disaster – can have far-reaching implications. Healthcare organizations must look at their suppliers and develop contingency plans that can be implemented in the event of service disruption, and regulators should identify these potential single points of failure and conduct proactive audits to ensure that these companies are fully compliant and have adequate cybersecurity.
HIPAA-Regulated Entities are Failing Cybersecurity 101
The HIPAA Security Rule sets minimum standards for cybersecurity, so it is concerning just how often Security Rule violations are identified, especially considering it has been two decades since the Security Rule took effect. When OCR conducted its last round of HIPAA compliance audits in 2016 and 2017, noncompliance with the Security Rule standards was rife, especially in the area of risk analysis and risk management, where most audited entities were found to be non-compliant. Those audits only covered 8 of the 180 HIPAA provisions, including just 2 of the administrative safeguards of the HIPAA Security Rule. It is reasonable to assume that similar levels of noncompliance would be identified if the audits were expanded to cover a more comprehensive set of HIPAA Security Rule standards.
Five years on and little appears to have changed. Incomplete or nonexistent risk analyses are still frequently identified, hence OCR’s latest enforcement initiative targeting risk analysis noncompliance. If a risk analysis is not conducted covering all electronic protected health information (ePHI), all systems that touch ePHI, and all external sources of ePHI, it is inevitable that risks will remain unaddressed and can be exploited by threat actors.
Risks are often only identified once they have been exploited. The breached entity then addresses those vulnerabilities to prevent further breaches. This reactive approach to cybersecurity needs to change, and conducting a comprehensive and accurate risk analysis is the best place to start. This is not only an issue at small to medium healthcare organizations, as the Change Healthcare ransomware attack demonstrated. Change Healthcare failed Cybersecurity 101 by failing to comprehensively implement multifactor authentication and did not have effective policies and procedures for rapidly restoring systems in the event of a disaster.
What is needed is a change of mindset, where Security Rule compliance is not viewed as a checkbox item to keep regulators happy or the final goal in cybersecurity. Security Rule compliance is just the first step. Cybersecurity needs to be improved further still.
Healthcare Organizations Should Implement the HPH Sector Cybersecurity Performance Goals
Based on breach reporting at The HIPAA Journal, it is clear that many of the year’s data breaches could have been prevented by implementing recognized security practices and the voluntary cybersecurity performance goals (CPGs) published by OCR in January 2024. Implementing those measures should be one of the key cybersecurity priorities for 2025 in healthcare.
For many low-resource hospitals and small healthcare providers, finding the funds to make the necessary improvements to cybersecurity and recruiting and retaining skilled cybersecurity staff can be a major challenge. OCR proposed a federal assistance program to help low-resource healthcare providers cover the cost of implementing the CPGs. It is vital for Congress to approve the necessary funding to make that happen and pursue initiatives to increase the size of the US cybersecurity workforce to ensure that cybersecurity can be maintained. New York is leading the way at the state level, having made funds available to help hospitals in the state make the necessary cybersecurity improvements and comply with the stricter cybersecurity regulations implemented last year.
Updates are Needed for Out-of-Date Healthcare Cybersecurity Regulations
It is too early to tell what impact the publication of the voluntary cybersecurity goals will have on healthcare cybersecurity, given that they were only published 12 months ago and there is limited adoption data. What is abundantly clear is that the Security Rule is in desperate need of an update to incorporate the latest best practices and new requirements for cybersecurity.
One of the last actions of OCR under the Biden Administration was to publish a proposed update to the HIPAA Security Rule, which eliminated some of the confusing language such as “addressable” implementation specifications, stipulated what a risk analysis should entail in more detail than the rather vague requirements of the current Security Rule, and made several cybersecurity 101 practices and security measures a requirement. While some of the proposed new requirements could place a considerable financial and administrative burden on regulated entities and may be challenging to implement, the update is desperately needed and long overdue. The hope is that, unlike the Privacy Rule update proposed by the previous Trump Administration, which has been gathering dust over the past 4 years, the new administration will press ahead and review the comments and implement a new rule.
The HHS Needs to Conduct More Audits, Increase Enforcement, and Impose Bigger Penalties for Cybersecurity Failures
An audit of the OCR HIPAA audit program by the HHS Office of Inspector General found that while OCR had met its responsibilities under the HITECH Act to conduct HIPAA audits (for the investigated period), they were far too narrow in scope and OCR’s oversight of the HIPAA audit program was not effective at improving cybersecurity at HIPAA-regulated entities. In May 2024, in an interview with ISMG, OCR Director Melanie Fontes Rainer said, “We have reopened our HITECH audits. And so we’re proactively doing audits as well right now.” It is unclear to what extent those audits have been conducted so far, but the audit program needs to be expanded and should primarily focus on entities that are critical to the functionality of the healthcare system, where a successful cyberattack could have a far-reaching impact.
OCR increased HIPAA enforcement in 2024, with OCR Director Melanie Fontes Rainer confirming that OCR closed 22 enforcement actions with financial penalties in 2024, collecting more than $12 million in settlements and civil monetary penalties. The penalties for non-compliance with the HIPAA Rules should serve as an effective deterrent; however, the reinterpretation of the language of the HITECH Act saw penalties significantly reduced. An increase in penalties may be enough to spur healthcare organizations into ensuring they are fully compliant with the HIPAA Rules. That is something that OCR has been pushing for, but it is a decision that lies with Congress.
More Must be Done to Combat Ransomware Groups
The increase in ransomware attacks on critical infrastructure, especially Colonial Pipeline and JBS, which respectively disrupted fuel supplies and food production, spurred the Biden Administration to take action. Efforts were increased to tackle the problem, and Russia and other states were pressed to take action over ransomware attacks by threat actors operating within their own countries. An international effort at disrupting these cybercriminal groups has been effective, although progress has been slow.
The Annual Report from GuidePoint Security on the ransomware and cyber threat landscape highlighted the extent of the problem. The law enforcement operations have been successful and have dealt significant blows to certain groups, but their impact on the overall threat landscape has been limited. Ransomware-as-a-service groups continue to proliferate, and there were record numbers of victims in Q4, 2024 (1,600+), although year-over-year growth in victims fell to 8.72% from 76.8% growth from 2022 to 2023. While actions against large groups such as ALPHV and LockBit have hampered their ability to operate, the RaaS business model means that affiliates are free to leave a disrupted operation and join another group, and the last year has seen a 40% year-over-year increase in active threat groups.
President Biden put pressure on President Putin to take action to stop ransomware attacks on the United States from within Russia, with little effect. Perhaps President Trump, who claims to have “a very, very good relationship” with Putin, will fare better. President Trump said in January 2025 that he wants to meet Putin soon to ensure the end of the Ukraine war. Hopefully, the ransomware problem will also be on the agenda in that meeting.
Steve Alder, Editor-in-Chief, HIPAA Journal



