The Biggest Healthcare Data Breaches of 2024
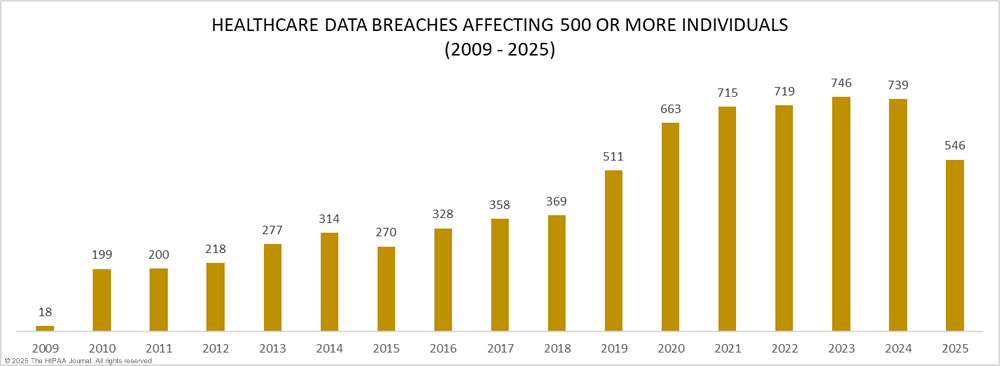
Last year was an annus horribilis for healthcare data breaches. While there appears to have been a slight year-over-year reduction in the number of reported data breaches of 500 or more records, the number of individuals affected by those breaches has risen considerably. As of March 19, 2025, 734 large data breaches have been reported to OCR, a percentage decrease of 1.74% from the 747 large healthcare data breaches reported in 2023. While a reduction in healthcare data breaches is a step in the right direction, 2024 was the worst-ever year in terms of breached healthcare records, which jumped by 64.1% from last year’s record-breaking total to 276,775,457 breached records, or 81.38% of the 2024 population of the United States.
Those figures will surely grow over the coming weeks and months as more data breaches are expected to be added to OCR’s breach portal for December, and 64 data breaches in 2024 have been reported using potential placeholder estimates of 500 or 501 breached records. These figures are commonly used when the file review has not been completed by the breach reporting deadline.

The Biggest Healthcare Data Breaches in 2024
In 2024, there were 14 data breaches involving more than 1 million healthcare records, including the biggest healthcare data breach of all time that affected an estimated 190,000,000 million individuals. Across those 14 data breaches alone, the records of 237,986,282 U.S. residents were exposed or compromised—around 69.97% of the U.S. population. All but two of the 14 data breaches were hacking incidents, and 8 involved business associates of HIPAA-covered entities.
Change Healthcare
The largest healthcare data breach of the year occurred at Change Healthcare. On February 12, 2024, a ransomware affiliate accessed the Change Healthcare network and used ransomware to encrypt files on February 21, 2024. Prior to encrypting files, the ransomware affiliate exfiltrated the protected health information of an estimated 190 million individuals – 69% of the year’s breached records. The BlackCat/ALPHV ransomware group was behind the attack and pulled an exit scam after being paid a $22 million ransom. The affiliate behind the attack claims not to have been paid and provided the stolen data to the RansomHub group, which tried unsuccessfully to extort Change Healthcare a second time.

Get The FREE
HIPAA Compliance Checklist
Immediate Delivery of Checklist Link To Your Email Address
Please Enter Correct Email Address
Your Privacy Respected
HIPAA Journal Privacy Policy
Not only was this the largest healthcare data breach of all time it also caused more disruption than any other healthcare cyberattack due to the number of healthcare organizations that relied on Change Healthcare’s systems and the prolonged outage. The attack prevented patients from obtaining medications unless they were able to pay for them out of their own pockets, and the outage caused severe disruption to healthcare providers’ revenue cycles, pushing many small practices to the brink of closure.
The investigation of the attack revealed the ransomware affiliate used compromised credentials for a Citrix portal that did not have multifactor authentication enabled. The scale of the disruption prompted lawmakers to ask questions about the impact of consolidation in healthcare. As this attack clearly showed, consolidation can create a single point of failure that brings the U.S. healthcare system to its knees. Questions were also asked about how it is possible for a company as large as Change Healthcare, which is a subsidiary of the healthcare behemoth UnitedHealth Group, to fail to implement such a fundamental cybersecurity protection as multifactor authentication and not have tested protocols and procedures for rapidly restoring systems in the event of a ransomware attack.
Kaiser Foundation Health Plan
The second biggest healthcare data breach of the year was announced in April and involved the protected health information of up to 13,400,000 individuals. The scale of the breach makes it one of the largest healthcare data breaches of all time, although the negative impacts of the breach were minimal.
Like many healthcare organizations, Kaiser Foundation Health Plan had added tracking technologies such as pixels to its websites and applications, which recorded user interactions and transmitted that information to third parties such as Meta, Google, Microsoft, and X. The information transferred depended on user interactions and may have included an identifier such as an IP address together with the pages visited, including search terms of its health encyclopedia that revealed symptoms, drugs, injuries, and exercises. The tracking tools were identified during a voluntary internal investigation.
OCR issued guidance to HIPAA-regulated entities on HIPAA and tracking technologies in December 2022, which stated that these tools are generally not HIPAA compliant. The guidance was challenged by the American Hospital Association and OCR issued updated guidance in 2024; however, a judge ruled that the guidance was unlawful and partially vacated the guidance. That decision means tracking technologies can be used on healthcare websites but only on unauthenticated web pages, not on authenticated web pages such as patient portals.
Ascension Health
The third biggest healthcare data breach of 2024 was another ransomware attack. In May, Ascension Health fell victim to a Black Basta ransomware attack that disrupted clinical operations across the Catholic health system’s 142 hospitals. The attack was detected on May 8, 2024, and resulted in an electronic health record outage that lasted for almost 4 weeks. The investigation of the Ascension ransomware attack identified the initial access vector as a malicious file that had been inadvertently downloaded by an employee, which gave the ransomware group access to the user’s device, and from there they were able to move laterally to compromise 7 of its 25,000 servers.
The attack was reported to OCR using a placeholder figure of 500 affected individuals. That total was updated in December 2024 when it was confirmed that the hackers had access to the protected health information of 5,599,699 patients. Some patients are not expected to receive notification letters until January 2025, 8 months after their data was stolen.
HealthEquity
In March 2024, the Utah-based financial technology and business services company, HealthEquity, detected unauthorized activity in a device used by one of its business partners. HealthEquity provides health savings account (HSA) services and other consumer-directed benefits solutions such as health reimbursement arrangements and manages millions of HSAs, HRAs, and other benefit accounts.
The vendor’s device had been compromised by a threat actor who used the vendor’s credentials to access SharePoint, which contained the protected health information of 4,300,000 individuals. The threat actor copied data from SharePoint using the business partner’s account. The investigation confirmed the breach was limited to SharePoint, with none of its core systems compromised. HealthEquity did not disclose how the vendor’s device and credentials were compromised.
Concentra Health Services
Concentra Health Services, a Texas-based physical and occupational health provider, was one of the companies affected by a major data breach at business associate PJ&A, a provider of medical transcription services. The PJ&A cyberattack was first identified in May 2023, with hackers having access to its systems from March 27, 2023, to May 2, 2023. The affected clients were notified in July 2023, and PJ&A announced the breach in November 2023, although it took Concentra until January 2024 to confirm that the protected health information of 3,998,163 individuals had been compromised in the attack.
PJ&A reported the data breach to OCR as affecting 9,302,588 individuals, not including the Concentra total or other clients that issued their own notifications. Other healthcare organizations affected include Cook County Health, Northwell Health, Salem Community Hospital, and Kansas City Hospital.
Centers for Medicare & Medicaid Services
The Department of Health and Human Services’ Centers for Medicare and Medicaid Services (CMS) reported a breach of the protected health information of 3,112,815 individuals in September 2024. CMS contracted with Wisconsin Physicians Service Insurance Corporation (WPS) to handle Medicare Part A/B claims, and WPS used file transfer software to transfer large files containing protected health information – Progress Software’s MOVEit Transfer solution.
In May 2023, the Clop threat group mass-exploited a zero day vulnerability in the solution. In total, the Clop group exploited the vulnerability to access the MOVEit environments of more than 2,500 companies worldwide and stole the personal data of almost 100 million individuals.
The CMS was one of the last organizations to disclose the breach, 16 months after the data breach occurred. WPS applied the patch provided by Progress Software in May 2023, and the initial investigation uncovered no evidence to suggest any data had been stolen. A further review was conducted a year later in May 2024, and it was confirmed that data had been stolen.
Acadian Ambulance Service
Acadian Ambulance Service is a medical transportation company serving patients in Louisiana, Tennessee, Texas, and Mississippi. On June 23, 2024, suspicious activity was identified within its network. Daixin Team claimed responsibility for the attack and claimed to have obtained the records of 10 million patients; however, the review of the stolen data confirmed that the protected health information of 2,896,985 individuals had been stolen between June 19, 2024, and June 21, 2024. Daixin Team demanded a $7 million ransom and Acadian Ambulance Service attempted to negotiate, saying the maximum the company could pay was $173,000. That was not enough to prevent the release of the stolen data.
A&A Services d/b/a Sav-Rx
The Nebraska-based pharmacy benefit management company, Sav-Rx, announced in May 2024 that hackers had gained access to its network in October 2023, although it took until April 2024 to notify its health plan customers about the data breach, and individual notifications did not start to be mailed to the 2,812,336 affected individuals until late May 2024.
Sav-Rx was able to quickly recover from the attack and fully restored the impacted systems the following day without any material disruption to patient care or prescription shipping. This appeared to have been a ransomware attack, although it was described as a cyberattack that caused disruption to IT systems. The ransom appears to have been paid, as Sav-Rx said it has confirmed that the stolen data has been permanently deleted and not further disseminated.
WebTPA Employer Services
WebTPA, a Texas-based provider of administration services to health insurance and benefit plans, detected a network intrusion on December 28, 2023; however, the forensic investigation revealed hackers had first accessed its network 8 months previously, and exfiltrated files containing the protected health information of 2,518,533 individuals between April 18 and April 23, 2023.
The affected clients, which included The Hartford, Transamerica, and Gerber Life Insurance, were notified about the breach in March 2024; however, it took until May 2024 for the WebTPA data breach to be reported to the HHS’ Office for Civil Rights and for individual notifications to be mailed, more than a year after the data had been stolen. Several lawsuits have been filed in response to the data breach, with the lack of timely notifications criticized in the litigation.
Integris Health
The Oklahoma hospital operator Integris Health reported a data breach to the HHS’ Office for Civil Rights in January 2024 involving the protected health information of 2,385,646 current and former patients. Hackers breached its network over the Thanksgiving weekend in November 2023 and exfiltrated patient data. The Hunters International hacking group claimed responsibility for the attack.
While Hunters International has used ransomware in the past, it is primarily a data theft and extortion group and did not encrypt data on the Integris Health network. When Integris Health refused to pay to have the stolen data deleted, Hunters International started contacting patients directly to demand a $50 payment to have their data deleted, otherwise, the group claimed it would sell the stolen data.
Medical Management Resource Group
Arizona-based Medical Management Resource Group, LLC (MMRG), doing business as American Vision Partners, reported a 2,350,236-record data breach to the HHS’ Office for Civil Rights in February 2024. American Vision Partners provides administrative services to ophthalmology practices in Arizona, Texas, New Mexico, and California, and shares a management system, IT, and infrastructure with 12 practices. The cyberattack was detected on November 14, 2023, although it is unclear when the hackers first gained access to its network. Patients of all 12 of those practices had data compromised in the attack. The breached data included names, dates of birth, medical information, and for some individuals, Social Security numbers.
Summit Pathology and Summit Pathology Laboratories, Inc.
Summit Pathology and Summit Pathology Laboratories, Colorado-based pathology service providers, reported a cyberattack and data breach in October 2024 that involved the protected health information of 1,813,538 patients. Hackers gained access to its network on or around April 18, 2024, and exfiltrated files containing patient data. Summit Pathology confirmed that the Medusa ransomware group was behind the attack and gained access to the network after an employee was tricked into opening a malicious file attached to an email. While data was stolen, there was no data leak, which indicates the ransom was paid.
OnePoint Patient Care
OnePoint Patient Care, a Tempe, AZ-based hospice-dedicated pharmacy and pharmacy benefit manager, fell victim to an INC Ransom ransomware attack. The ransomware group was initially thought to have stolen the protected health information of 795,916 individuals, but as the investigation progressed, more individuals were discovered to have been affected, and the total was increased to 1,741,152 individuals. When the ransom was not paid, INC Ransom published the stolen data on its data leak site.
Geisinger
Aside from the Kaiser Foundation Health Plan data breach, all of the above million+ record data breaches have been hacking incidents conducted by financially motivated cybercriminal groups. The data breach reported by the Pennsylvania healthcare provider Geisinger is a little different.
Geisinger contracted with a company called Nuance Communications, which provided IT services to Geisinger. On November 29, 2023, Geisinger detected unauthorized access to patient data by a former Nuance employee. Nuance investigated and confirmed there had been unauthorized access to the data of 1,276,026 patients by a former employee two days after the employee was terminated. The breach shows why it is important to ensure that login credentials are revoked immediately when an employee is terminated or otherwise leaves the company.
Top 10 Biggest Healthcare Data Breaches of All Time
As the table below shows, two of the biggest healthcare data breaches of 2024 rank in the top ten healthcare data breaches of all time, and half of the top ten data breaches have occurred in the past 2 years, showing it is not only the number of data breaches that has been increasing but also the severity of the data breaches. With record numbers of healthcare records being compromised, it is clear that more needs to be done to improve healthcare cybersecurity.
| Year | Regulated Entity | State | Entity Type | Individuals Affected | Cause of Breach |
| 2024 | Change Healthcare, Inc. | MN | Business Associate | 100,000,000 | Hacking/IT Incident |
| 2015 | Anthem Inc. | IN | Health Plan | 78,800,000 | Hacking/IT Incident |
| 2023 | Welltok, Inc. | CO | Business Associate | 14,782,887 | Hacking/IT Incident |
| 2024 | Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 | Unauthorized Access/Disclosure |
| 2019 | Optum360, LLC | MN | Business Associate | 11,500,000 | Hacking/IT Incident |
| 2023 | HCA Healthcare | TN | Business Associate | 11,270,000 | Hacking/IT Incident |
| 2015 | Premera Blue Cross | WA | Health Plan | 11,000,000 | Hacking/IT Incident |
| 2019 | Laboratory Corporation of America Holdings dba LabCorp | NC | Healthcare Provider | 10,251,784 | Hacking/IT Incident |
| 2015 | Excellus Health Plan, Inc. | NY | Health Plan | 9,358,891 | Hacking/IT Incident |
| 2023 | Perry Johnson & Associates, Inc. dba PJ&A | NV | Business Associate | 9,302,588 | Hacking/IT Incident |
At the start of 2024, the HHS’ Office for Civil Rights published two sets of healthcare-specific cybersecurity performance goals (CPGs). The CPGs consist of cybersecurity best practices that should have the biggest impact on security posture, and all healthcare organizations are encouraged to adopt the CPGs to improve their defenses against external and internal threats. OCR is well aware that while the voluntary CPGs should have a massive impact on healthcare cybersecurity and help to drastically reduce the number of data breaches, voluntary goals alone are unlikely to be sufficient.
In December 2024, the HHS published a long-awaited proposed update to the HIPAA Security Rule that will, if enacted, force healthcare organizations to implement a range of measures to improve their security posture. The proposed update includes some of the recommended measures in the CPGs, such as multifactor authentication, encryption for data at rest and in transit, mitigating known vulnerabilities, network segmentation, maintaining an accurate asset inventory, and cybersecurity testing.
The proposed HIPAA Security Rule should go a long way toward reducing healthcare data breaches and will help OCR hold healthcare organizations accountable for security failings and insufficient investment in cybersecurity. The fate of the HIPAA Security Rule update now lies with the incoming Trump administration.



